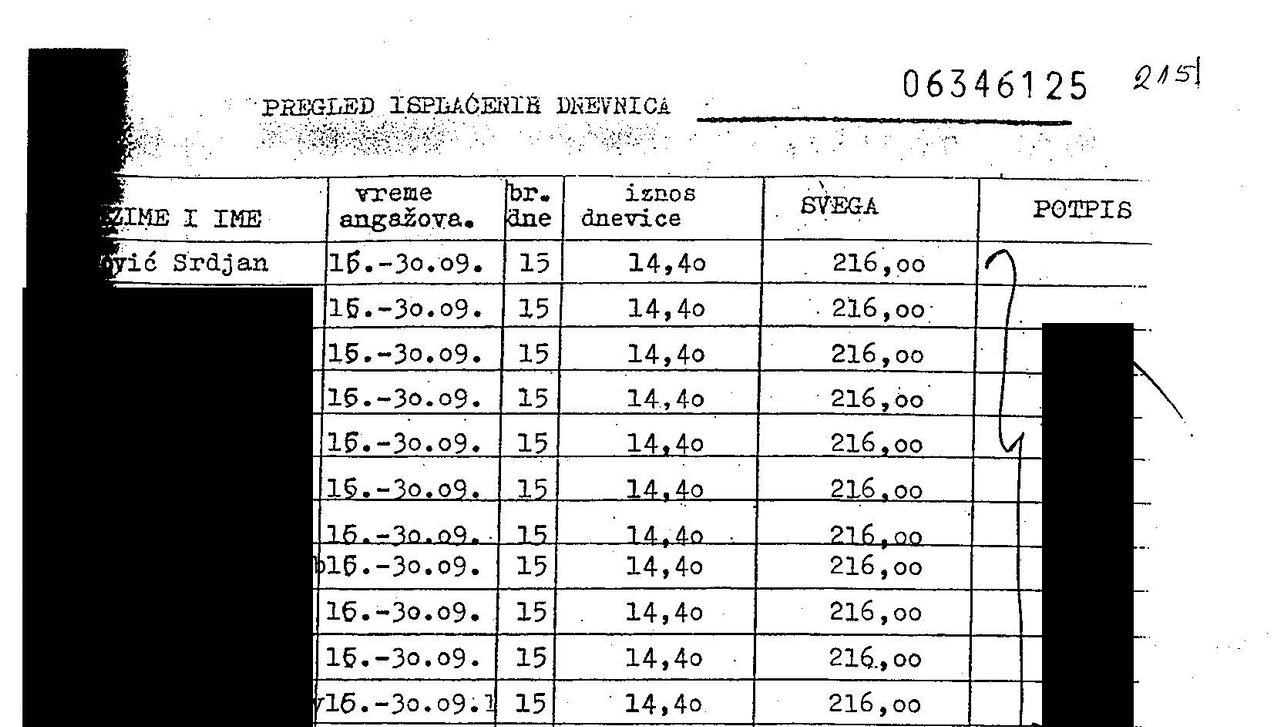
Evidence Collection & Consent
Law
A verifiable ingestion framework designed to transform multimedia submissions from secure messaging apps into court-admissible evidence.
By integrating decentralized chatbots with platforms like Signal and Telegram, it establishes a tamper-evident chain of custody that cryptographically binds media to the explicit, informed consent of the source.
This approach bridges the gap between high-risk field documentation and the rigorous evidentiary standards of international justice mechanisms, ensuring that humanity’s most critical records remain legally robust and ethically sound.
YEAR
2022
PARTNERS
Guardian Project
ProofMode app
Signal
Telegram
The Problem
Digital media captured in high-stakes environments, such as war zones or human rights crises, may be required to meet the evidentiary standards required for criminal trials. While photos and videos are persuasive, they often lack a verifiable “chain of custody”. Traditional messaging services routinely strip critical metadata to protect privacy; however, this decontextualization makes it nearly impossible for investigators to prove origin or authenticity once the file leaves the original device.
Furthermore, without documented, informed consent from the source, such records are often deemed inadmissible, leaving critical survivor testimonies legally invisible.
The Solution
Starling developed a chatbot, integrating with secure messaging services like Signal and Telegram, to automate the authenticated collection of digital evidence. When a source sends media to the bot, the system instantly generates a cryptographic fingerprint (SHA-256 hash) and seals the file alongside its associated metadata in a tamper-evident archive.
Crucially, the bot leads the documenter through an interactive back-and-forth to record the informed consent of the sender at the moment of ingestion. This consent is cryptographically bound to the media’s unique hash, creating an immutable record of usage permissions. This authentication layer ensures that crowdsourced evidence can be prioritized, processed, and examined by international prosecutors with its legal and ethical integrity fully intact.
GOING FURTHER
Case Study: Building ProofMode as a Library in a custom, bespoke Signal build
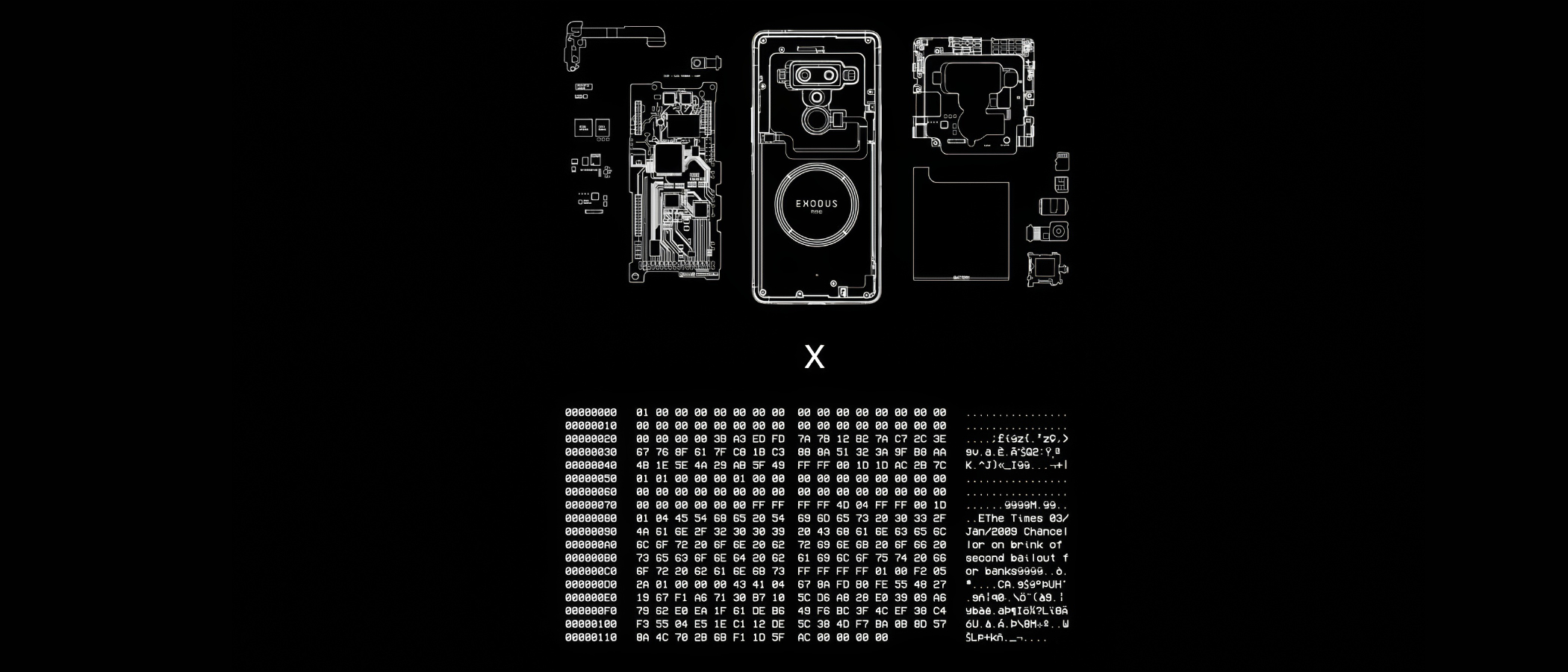
Secure Enclave Signing
Law
This prototype establishes a hardware-based root of trust for digital media by cryptographically sealing assets inside a device’s protected silicon environment. It shifts the security boundary from vulnerable software to dedicated cryptographic processors, ensuring that signing keys remain inaccessible to external threats and that every asset is tied to an immutable hardware identity.
By anchoring provenance at the absolute point of capture, it creates a foundational “proof of origin” that is resilient against both digital manipulation and systemic distrust.
YEAR
2022
PARTNERS
HTC
Numbers and the Numbers Protocol
LINKS
– HTX Exodus 1S Phone
– The Starling Framework
The Problem
The ideal environment to manage digital signing is a cryptographic processor within the capture device, where the keys are never revealed and the system will only sign data within a predefined pathway. This ensures all authenticated data carrying a signature by those keys are unambiguously originating from the capture device. Unfortunately, hardware secure enclaves and similar technology, are not widely included in professional capture devices, or implemented with sufficient firmware that supports these digital signing use cases.
JOURNALISM
Anchors in hardware rather than software support shielding reporters from deepfakes accusations, and gives them a digital “negative” as an origin record of their work.
HISTORY
By binding historical records to the unique physical identity of the capture device, it creates a resilient, verifiable archive that ensures the “first draft of history” cannot be silently altered by future actors.
LAW
Hardware-level signing establishes an airtight digital chain of custody and ensures cryptographic keys are physically isolated and never exposed, aiming to meet the most rigorous standards for legal admissibility.
The Solution
Starling Lab’s prototype utilizes Secure Enclaves (isolated cryptographic processors) to generate and store signing keys where they can never be revealed. This implementation creates a tethered workflow, pairing a digital camera with a secure-element-equipped device (such as the HTC Exodus 1S).
As media is captured, the system generates a cryptographic hash that is signed within the hardware’s protected environment, creating a tamper-evident record from the first millisecond of the asset’s existence.
This prototype serves as a technical blueprint for hardware vendors, advocating for a decentralized framework where privacy-respecting key management and data authentication are baked into the physical design of professional tools.
Document Redaction
Law
Establishing a cryptographic seal of transparency for sensitive digital records, moving beyond traditional “black-box” redaction.
Zero-Knowledge Proofs (ZKP) allow investigators to obscure personally identifiable information (PII) while providing a mathematical guarantee that no other part of the document has been altered.
This concept shifts the trust model from requiring blind faith in a publisher’s edits to providing affirmative proof of a document’s integrity, ensuring that critical primary sources remain both ethically protected and legally robust
YEAR
2022
PARTNERS
Stanford Applied Cryptography Group
LINKS
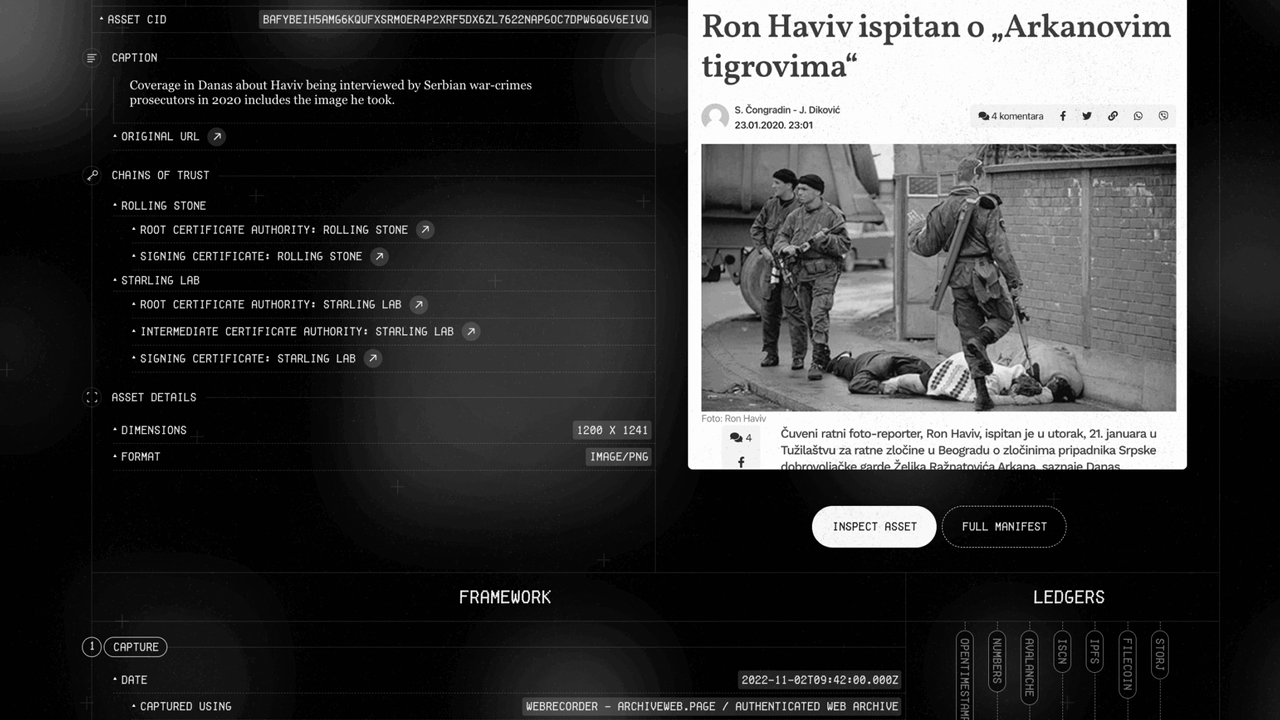
– Case Study: The DJ and the War Crimes
– Presentation from Trisha Datta and Dan Boneh
The Problem
Accountability investigations often rely on digitized primary sources – such as the UN payroll records unearthed in our Bosnia war crimes probe – that contain sensitive PII of individuals not central to the investigation. While redacting this information is a journalistic and ethical necessity, it creates a “trust gap”. In an era of widespread denialism and “cheapfakes,” any manual modification to a source document can be weaponized by bad actors to claim the entire record is a forgery, undermining the evidentiary weight of critical testimonies.
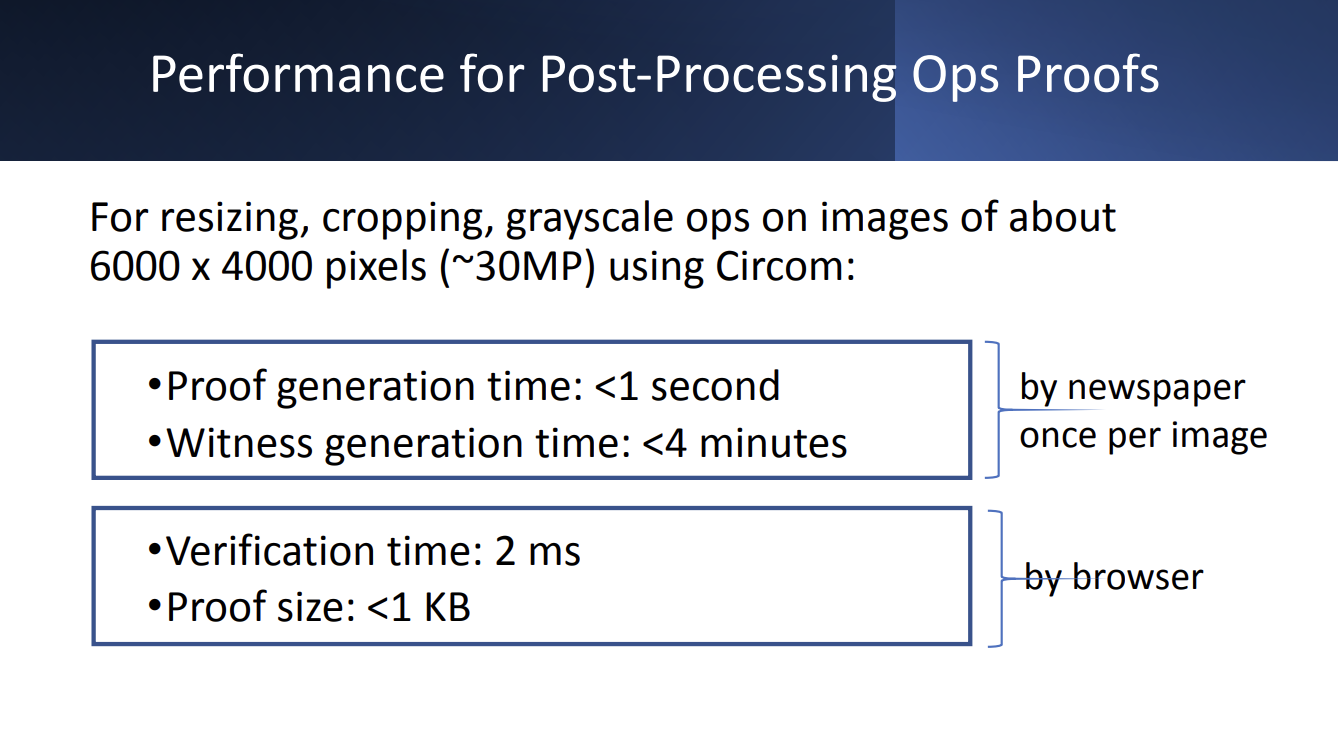
The Solution
In partnership with our principal investigator’s Professor Dan Boneh’s students from the Stanford Applied Cryptography Group, Starling developed a workflow that integrates forensic ingestion with cryptographic proof systems, and managed redactions.
It relies on a Zero-Knowledge Proof that certifies the relationship between the original and the redacted file. This technology generates a mathematical proof that the only changes made to the published PDF were the addition of black boxes over specific pixels. This allows third parties, such as expert witnesses, to “check the math” and verify that no text was altered or deleted, maintaining the document’s integrity while fulfilling privacy obligations
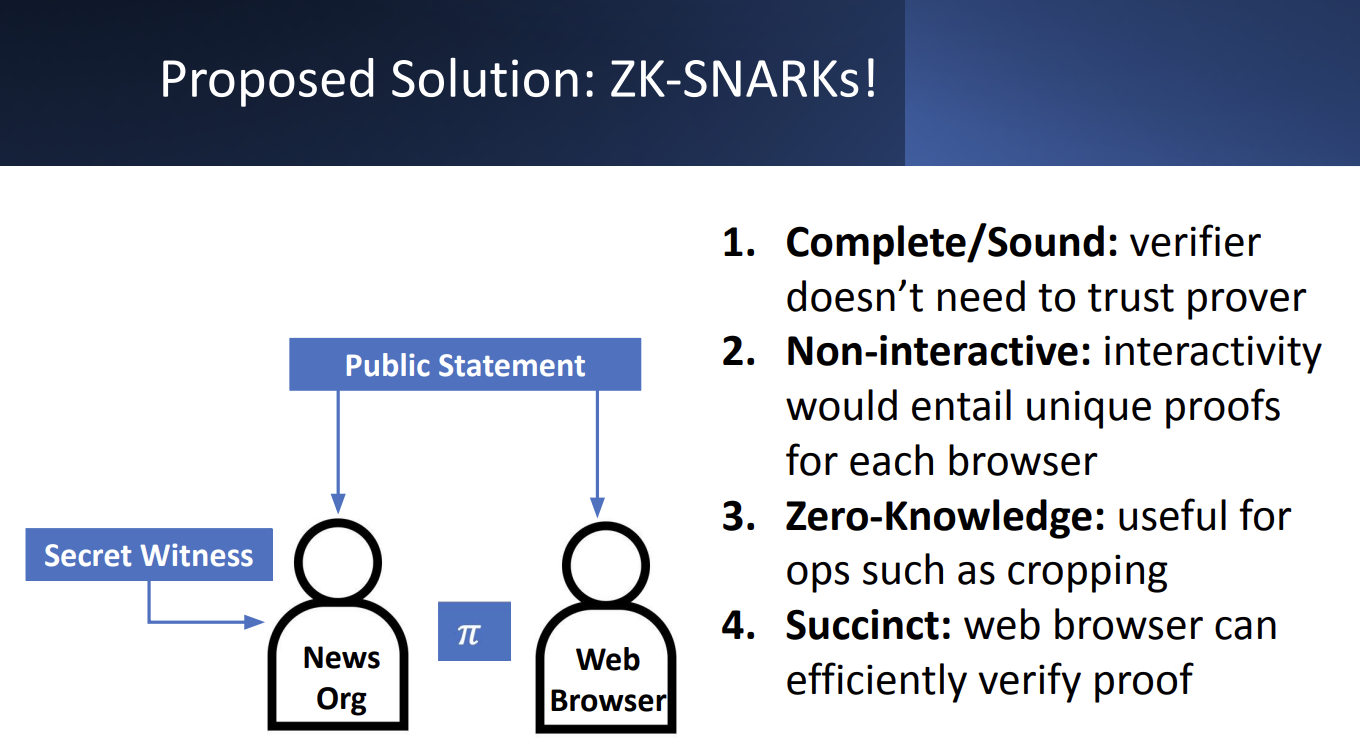
JOURNALISM
Verifiable Redaction allows newsrooms to protect the privacy of vulnerable bystanders without sacrificing the credibility of their reporting. By providing a cryptographic guarantee that only specific PII was obscured, journalists can defend their primary sources against bad-faith accusations of manipulation.
HISTORY
This technology safeguards the sanctity of historical records by ensuring that “anonymized” archives remain verifiable links to the past.
LAW
Verifiable Redaction establishes a court-admissible chain of custody for documents containing sensitive material. ZKPs benefit can facilitate the verification of proprietary forensic software, complex discovery datasets, and sensitive testimonial claims without compromising the underlying trade secrets or personal privacy that often create insurmountable disclosure dilemmas.
Distributed Storage
Law
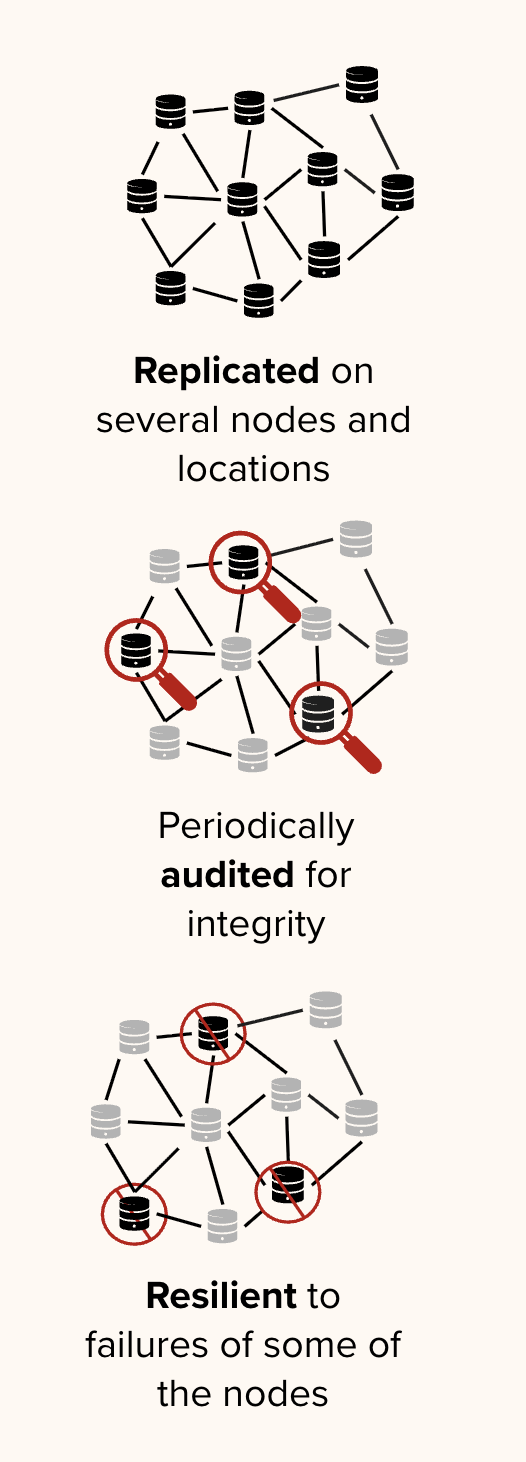
A decentralized infrastructure designed to ensure the long-term persistence and auditability of digital records by stripping centralized platforms of their outsized control over information.
Moving beyond fragile cloud silos, it cryptographically seals media and metadata across independent, multi-jurisdictional networks .
This framework shifts the preservation paradigm from blind trust in a single provider to a “proof of existence” model, where automated audits continuously verify that data remains untampered, replicated, and accessible .
YEAR
2021-25
PARTNERS
Filecoin
IPFS
Storacha
USC Libraries
The Problem
Traditional storage models rely on centralized cloud providers and social media platforms that exercise absolute authority over the availability and integrity of digital content. This creates a single point of failure: critical historical records can be silently modified, deleted due to shifting terms of service, or lost in jurisdictional disputes.
Standard databases also lack the transparency required for “chain-of-custody” documentation, making it difficult for archivists to prove that a file has not been altered since its initial preservation .
LINKS
– Case Study: Preserving 70 Years of Testimony with the USC Shoah Foundation
– Preserving Armenian Cultural Heritage on the Decentralized Web
– “Mom, I See War”, a collection of drawings from Ukrainian children, preserved on decentralised storage
The Solution
Starling Lab leads the world’s first academic center dedicated to using decentralized tools to advance human rights, backed by a multi-million dollar commitment from Protocol Labs and the Filecoin Foundation. We have moved beyond theoretical prototypes to large-scale implementations that safeguard humanity’s most sensitive digital records.
Our collaboration with the USC Shoah Foundation permanently preserves an archive of 55,000 video testimonies from genocide survivors. In tandem with the USC Digital Repository, a service of the USC Libraries, we run a 22-petabyte Filecoin node at USC – just one part of the Libraries’ deep expertise in preservation and archiving.
By housing this node within a leading research university, we combine the innovation of Web3 protocols with the rigorous preservation standards developed over decades by archivists and librarians.
Witness Servers
Law
Establishing institutional trust and technical corroboration for web evidence through decentralized, simultaneous crawling and cryptographic signatures.
YEAR
2024
PARTNERS
Webrecorder
FFDW
Harvard Library Innovation Lab
LINKS
– Concept note and Call for Contributions
– Our whitepaper on best practices in web archiving
The Problem
Minute, technical, cosmetic errors plague efforts of open source monitors who scour the Web and archive its content. In the context of legal investigations, these minor defects are considerable challenges to the reliability of the artifacts, and thus to the facts they aim to prove. Moreover, small organizations and individual investigators face a greater burden in arguing the probative weight of the material they collect than large, reputable, and established institutions.
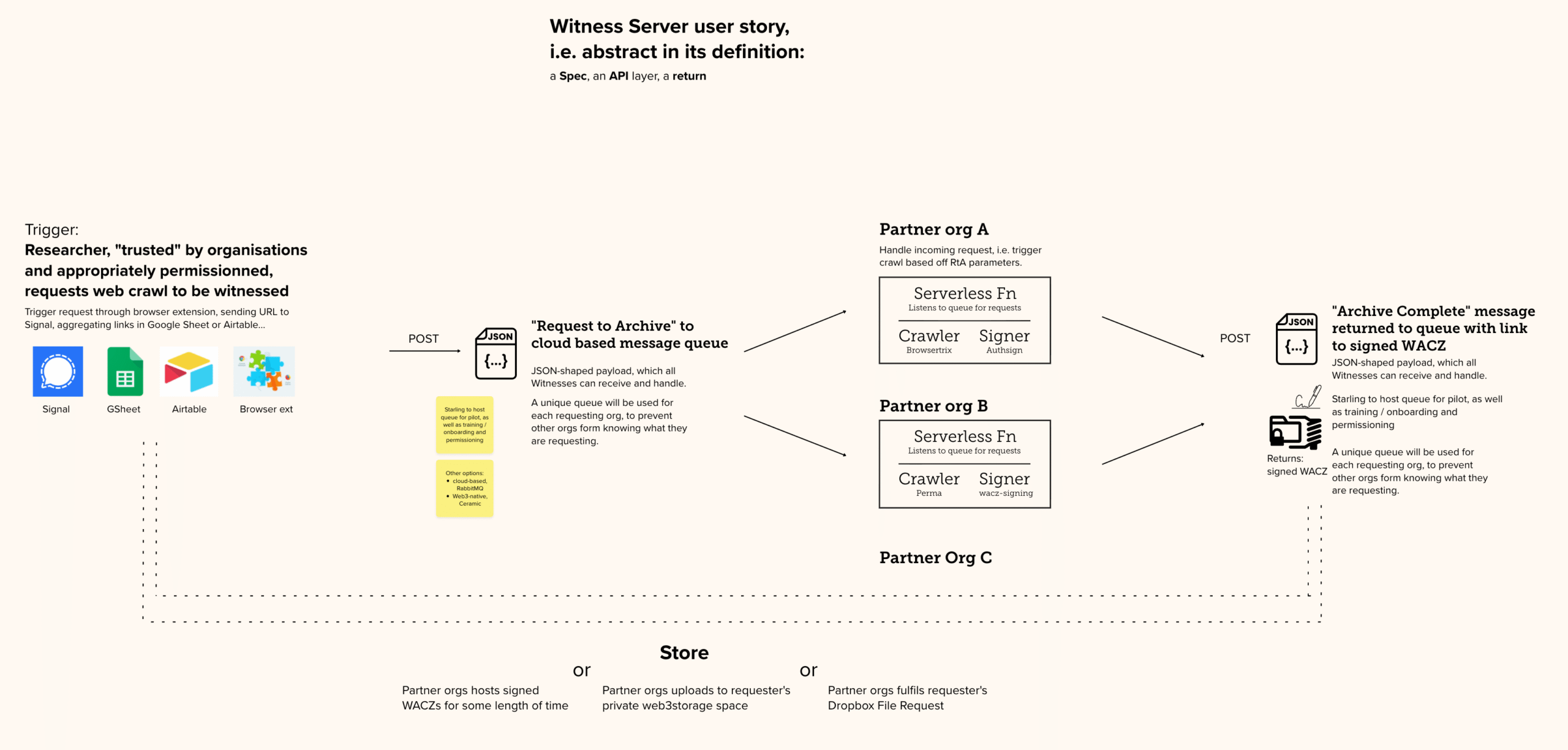
The Solution
We are developing the Witness Server prototype To replicate social trust in digital capture by involving reputable institutions as simultaneous observers of the web.
In short: a Witness Server is a service hosted by an institution that conducts on-demand web crawls. When a researcher initiates a local capture, a request is simultaneously dispatched to several partner Witness Servers (such as Harvard LIL or the Atlantic Council). Each institution performs its own crawl independently using its own infrastructure, creating a multi-perspective record of the same web content at that exact moment.
The prototypes follow all our learnings about web archives, Including the use of the WACZ open source format which bundles signed and hashed files.
By comparing multiple institutional archives, investigators can explain away non-material “cosmetic” defects (like pop-up banners) and provide overwhelming proof of the core content’s authenticity.
REFERENCE IMPLEMENTATION
On Github →
Still Photogrammetry
Law
Still Photogrammetry integrates authenticated metadata with 3D spatial reconstruction to provide a verifiable record of physical environments and historical sites.
By utilizing a decentralized framework where every source image is treated as an independently verifiable “atom” of fact, this prototype allows investigators to build unalterable, three-dimensional timelines of evidence. It anchors complex digital twins to a cryptographic “proof of existence,” proving that the spatial data has not been tampered with since the moment of capture and restoring trust in digital primary sources for law and journalism.
YEAR
2022-26
PARTNERS
Mike Caronna
Pixelrace
Artem Ivanenko
LINKS
The New Horizon Lab
Starling Lab’s Spatial Digest
The Problem
Techniques such as photogrammetry (and more recently, NeRF and Gaussian Splatting) permit the reconstruction of a space in 3D, from stitching together 2D photographs. These tools are key to both extended reality environments and to investigations driven by architectural practices. However, integrity and provenance data is lost in the computing that renders the 3D models.
The Solution
Starling experiments with capture techniques supportive of 3D reconstruction while including provenance and integrity markers. From using smartphones to professional DSLRs, we test the technical constraints against the needs of photogrammetry workflows, which require a large amount of photographs of the scanned location.
Furthermore, we are also prototyping virtual UIs in virtual reality aiming to bridge the gap between what the viewer can see (the 3D model) and the original location (as per the 2D photographs). The viewer can navigate the space and select these authenticated “anchors” to interrogate the model, furthering their trust in the reconstruction.
SELECTED WRITING
Our 2025 paper: Verifiable Reality: Contrasting Approaches to Photorealistic VR Using NeRF Streaming and Gaussian Splatting Technologies

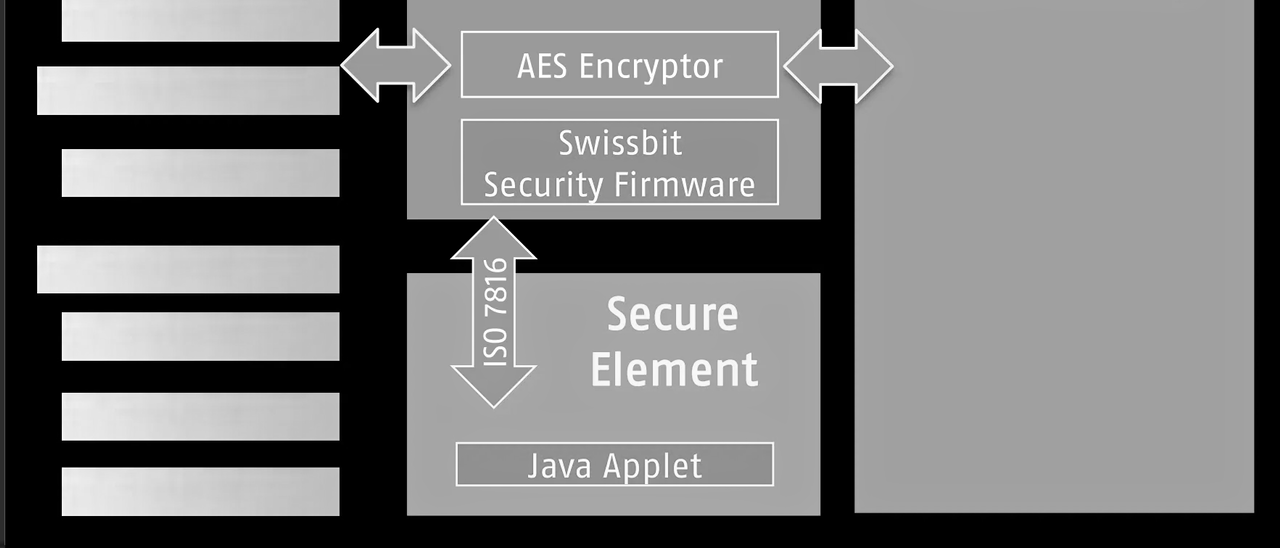
SD Card Encryption
The Problem
Losing control of data can happen when journalists, historians, or legal experts least expect it. SD cards can be seized during border crossings, left behind in a taxi, or stolen from a hotel room. Evidence that has been captured on an SD card, and which has not yet been anonymized, might carry geolocation or identity information that can lead authorities or militants to vulnerable people being photographed or interviewed. Another risk to unencrypted data on an SD card is that it could be manipulated undetected when not in one’s possession, with files erased or modified.
Prototypes are being tested by Starling Lab that both encrypt and hide important data captured by those in the field.
The Solution
Starling Lab is collaborating with industry partners including Swissbit, a leader in secure storage, to deploy hardware-encrypted SD cards that protect media the moment it is written to disk. This prototype ensures that digital assets are secured independently of the camera’s software vulnerabilities.
The solution creates an “encrypted tunnel” between the camera lens and the storage medium. Swissbit’s hardware-based encryption automatically protects image and video data without requiring additional software on the capturing device, ensuring that media cannot be manipulated or viewed in transit.
To protect the safety of practitioners in the field, the prototype relies on hidden partitions on the SD card. Sensitive files are stored in a manner that makes them impossible for unauthorized parties to discover or decrypt (even if the physical card is seized and inspected), while providing a critical layer of plausible deniability.
ProofMode Authentication
Law
Experimenting with the integration of lightweight, forensic-grade verification into secure messaging workflows.
YEAR
2022-23
PARTNERS
Guardian Project
Hala Systems
Signal Messenger
LINKS
– Case Study: The Proof’s in your Pocket
– From the Guardian Project team: Integrating libProofMode
The Problem
Citizen-captured photos and videos are becoming powerful reporting tools. But faked footage, or footage with missing crucial context, threatens to break the trust between a newsroom and its audience. Professional journalists thus need to be able to vet the footage captured by citizens to ensure that the files sent in by citizen journalists are authentic and accurate representations of the depicted event.
The Solution
ProofMode (developed by the Guardian Project) promotes trust by providing a means to strongly authenticate multimedia at the point of capture.
We were the first to experiment with its distribution as a software library, under the name libProofMode. Starling Lab developed a bespoke fork of Signal Messenger that embeds authentication as a native feature. Users of this custom app can snap photographs directly within the app, which automatically generates a unique OpenPGP key pair to sign the media and its surrounding sensor metadata, including location, time, and cell tower environment.
At capture, media hashes are automatically registered on OpenTimestamps to create a “proof of existence” on the Bitcoin ledger. To ensure secure transport, every file sent via Signal triggers an automated MobileCoin micro-transaction; the first 16 digits of the “proof hash” are embedded in the transaction memo, allowing the recipient to cryptographically verify that the file received exactly matches the file captured in the field.
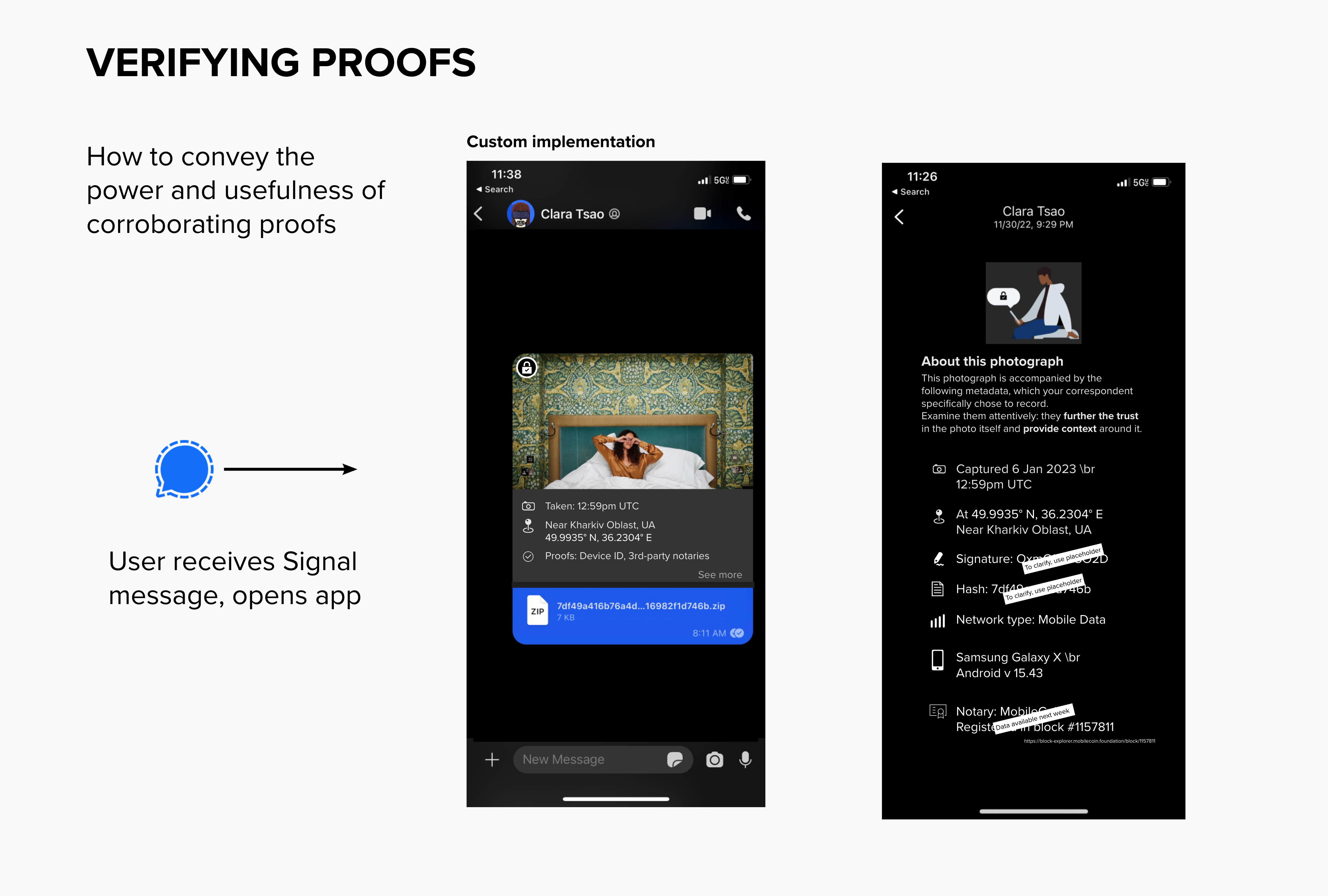
To reduce the burden on legal and journalistic investigators, the prototype features a visual layer of UI inside the Signal conversation view. Both sender and recipient can instantly surface contextual metadata snapshots and check them against immutable third-party record holders, such as the LikeCoin or Avalanche blockchains. This “glass-to-glass” approach ensures that technical authenticity markers are accessible and legible to the field practitioners who need them most.
HIGHLIGHT
In response to the shelling of Kharkiv’s schools, Starling Lab launched Project Dokaz (“Proof”). Local photographers were equipped with the custom Signal app to conduct “preventative documentation” in support of the Safe Schools Declaration. By capturing regular rounds of authenticated imagery, the team was able to verify the absence of military co-option at these sites, confirming their protected status under international law.
Read mode about Project Dokaz →
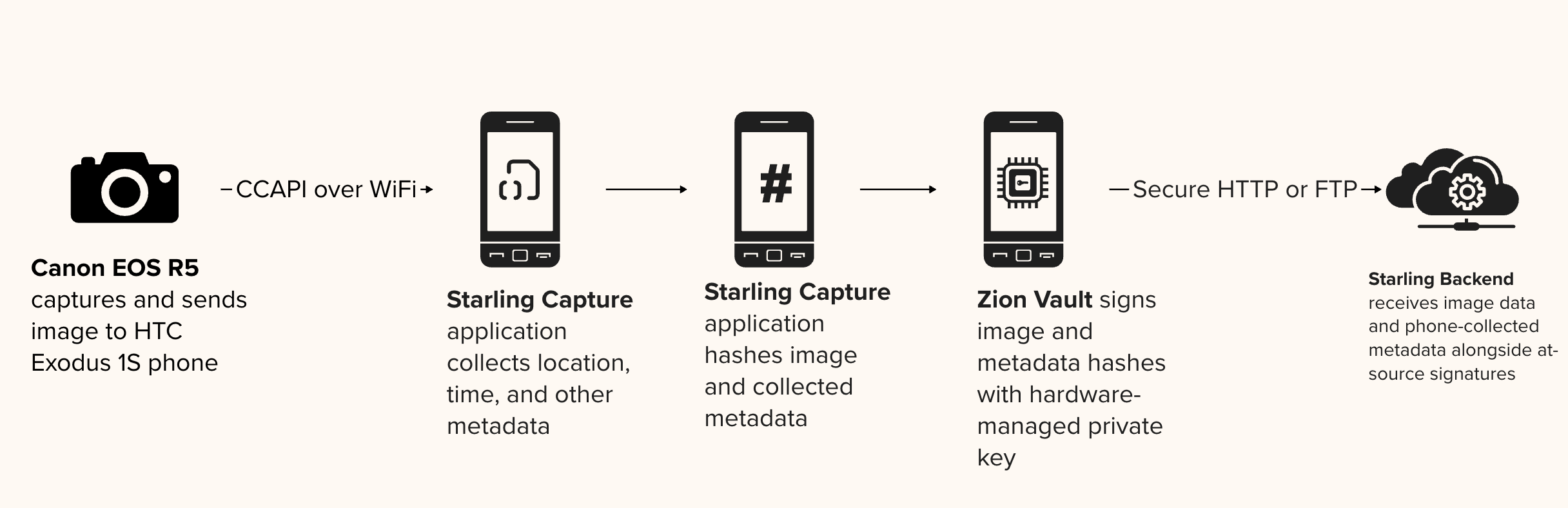
Companion Secure Enclave Authentication
Law
Companion Secure Enclave Authentication provides a “secure bridge” for professional photojournalism by tethering standalone cameras to mobile devices with hardware-level security. By pairing a professional camera with a smartphone’s secure enclave (such as the HTC Zion Vault), this prototype establishes a root-of-trust for images that traditional cameras cannot natively sign.
This method ensures that every photo is cryptographically sealed with a unique digital signature and sensor-rich metadata at the exact location and time of capture, creating an unalterable record of reality.
YEAR
2020-24
PARTNERS
HTC
Inside Climate News
Bay City News
Numbers
The Problem
Most professional cameras used in the field lack the internal hardware necessary to cryptographically sign assets or protect signing keys. Without a tamper-evident seal, digital photographs and their metadata (such as GPS and timestamps) are vulnerable to manipulation by AI tools or bad actors.
As these unverified images circulate, they lose their essential context, making it nearly impossible to determine the original version or defend against cheap- or deepfake allegations that distort the facts reported by photojournalists.
The Solution
Starling Lab pioneered a workflow that utilizes the hardware secure enclave of a companion smartphone to sign media from high-end cameras.
By tethering a professional camera (such as a Canon R5) to an HTC Exodus 1S phone via WiFi or USB, the Starling Capture app (co-developed with Numbers) instantly receives captured media. The phone’s Zion Vault hardware-secured signer then generates a cryptographic hash of the image and its associated sensor data (barometer, gyroscope, and GPS), sealing it with a private key that never leaves the device’s protected silicon.
CASE STUDIES
Stockton Homelessness: In 2022, Bay City News photojournalists documented the homelessness crisis in Stockton, CA, using Canon R5 cameras paired with HTC devices. These “authenticated time capsules” provided a verifiable record that challenged official statements and misinformation surrounding local funding disparities.
Brazil Pantanal: Photographer Felipe Albarenga documented the 2020 wildfires in the world’s largest wetland. By using the companion secure enclave, Albarenga created a tamper-evident archive of the devastation that could withstand the propaganda and denialism prevalent during the Brazilian presidential election.
Authenticated Web Archives
Law
Accurate, reliable, simple to use, and secure workflows for archiving web content.
The Problem
Online content disappears rapidly, erasing critical evidence for investigative journalism, accountability, and cultural preservation. Social media platforms and hosting providers face pressure to implement stricter content moderation, with automated filters and human moderators making rapid decisions about what stays online. Records documenting potential crimes – especially those with violent imagery – risk being permanently deleted. Restoring content is often impossible: original posters may be arrested, lose device access, or no longer be alive when investigations begin.
Existing archiving methods face three challenges: platforms actively block automated crawlers, preserved content lacks the cryptographic verification and chain-of-custody documentation required for legal admissibility, and saved material becomes unsearchable across large collections.
JOURNALISM
Strong web archives provide a tamper-evident way to capture online evidence, safeguarding reporting against censorship and the erosion of digital sources.
HISTORY
These archives create a trustworthy and resilient collection of digital primary sources, ensuring that the ephemeral nature of the web does not erase our collective memory.
LAW
This technology establishes an unbreakable digital chain of custody, transforming fleeting web content into verifiable, court-admissible evidence.
The Solution
Starling is developing workflows using open source software for archiving web content to ensure the preserved archives are accurate and reliable, taking into consideration the sensitivity of the data. We draw from the considerable expertise deployed by national libraries and legal deposits from around the world.
Our case studies have experimented with forensically-sound web archiving, focusing on capturing broad contextual snapshots of web material.
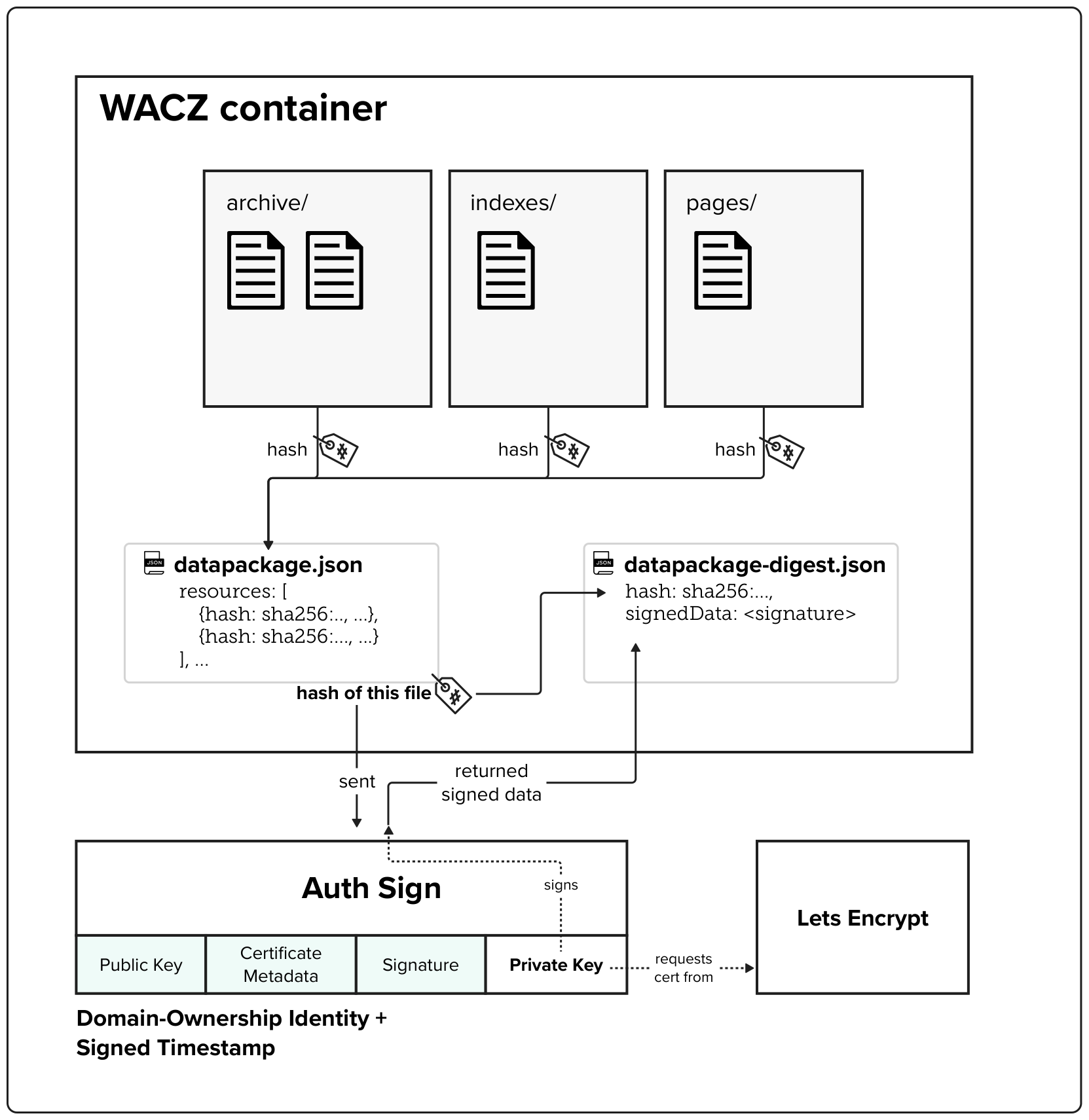
The WACZ standard and file format
The Web Archive Collection Zipped (WACZ) standard provides a portable packaging format for web archives that bundles WARC data, indexes, metadata, and verification information into a single ZIP file. Unlike traditional WARC files that lack contextual information and require complex server infrastructure for viewing, WACZ enables efficient browser-based rendering by organizing content with indexes that allow random access to only the data needed for each page.
Built-in Integrity Through Cryptographic Hashing
Every WACZ file includes a datapackage.json manifest that contains cryptographic hashes of all resources within the archive, providing a verifiable fingerprint to detect any unauthorized modifications. This hash-based integrity checking ensures that archived content remains tamper-evident throughout its lifecycle.
Authentication Through Digital Signatures
The specification adds optional authentication capabilities by allowing creators to digitally sign archives – notably using TLS certificates. These signatures validate both the identity of the entity creating the archive (using X.509 SSL certificates) and establish a trusted timestamp for when the capture occurred.