Starling Framework
How can we establish trust in our digital records?
Our Lab
The Starling Lab for Data Integrity at Stanford and the University of Southern California is the first academic research center dedicated to exploring how the ethical use of decentralized Web3 technologies can transform the work of historians, legal experts, and journalists.
More data is generated today than at any time in recorded history. More people are able to access the internet. Humanity is empowered as information democratized, but at the same time society must confront rising authenticity issues from misinformation and bad actors.
Our methodology provides a set of techniques and guidelines that tracks along the lifecycle of any piece of digital information. Front and center is strongly-authenticated data – data which contains verifiable markers of its provenance – and carefully designed measures for preservation.
We established The Starling Framework to address these new challenges to data integrity. In its simplest form, it is:
Capture, Store, Verify

Authenticity by Design
Authenticity by Design is the set of strategies and organizational principles we draw on when using our Framework of Capture, Store, Verify.
By prioritizing these throughout each step of the Framework, we can develop secure, effective ways of building trust in the authenticity of digital content, and build systems that leverage richer, more trustworthy data.
Root of Trust
In the context of the Starling Framework, a Root of Trust is the foundational source within a system where cryptographic trust is first established to ensure the authenticity and integrity of digital records. In an era of rampant misinformation and generative AI, establishing a clear “root” is essential for creating a verifiable audit trail that distinguishes genuine content from fabrications. It serves as the bedrock for a “trustless” system, where any third party can independently confirm a digital asset’s origin and history without needing to rely solely on the reputation of a centralized authority.
The Starling Framework prioritizes establishing this Root of Trust at the Capture phase – as close to the original event as possible. Ideally, this is anchored in the hardware or firmware of a device, such as a camera’s sensor or a smartphone’s secure enclave, to bind “birth certificates” of authenticity to an asset before it can be manipulated at the user level. By systematically hashing and signing digital media at this earliest stage, the framework creates an immutable provenance trail that remains with the data throughout its entire lifecycle.
Applying the Framework
Capture
We aim to establish a root of trust in an asset’s authenticity as early in its lifecycle as possible by binding authenticity metadata to an asset at the moment of creation.
We promote the creation of stronger, richer digital items by systematically hashing and signing media to preserve integrity while placing assets alongside robust provenance markers. By partnering with hardware developers, we verifiably capture data through secure enclaves, ensuring that “birth certificates” of authenticity are embedded before manipulation can occur.
This foundational step protects privacy and agency, empowering creators and investigators to control risks related to provenance data from the very start.
Store
Digital assets naturally decay due to hardware failure, media obsolescence, or malicious attacks, making resilient preservation essential.
We address this by leveraging tamper-evident data structures and constant audits to demonstrate integrity over time and immediately expose unauthorized changes. Assets are redundantly placed across distributed and peer-to-peer systems to eliminate single points of failure and ensure long-term availability.
Integrity proofs from the capture step are registered on consensus-based ledgers, creating an immutable record of the content and its time of creation that remains accessible even if original hardware fails.
Verify
Starling Labs embraces both human and technological approaches to verification, creating digital audit trails akin to a notary’s physical ledger.
Our workflows surface cryptographic integrity evidence and immutable registrations, allowing audiences to evaluate the evidence for themselves rather than relying on blind trust. These methods automate complex parts of the verification cycle, removing opportunities for human error and providing modern advantages for real-time authentication.
Ultimately, this enables current and future inspectors to definitively understand the provenance and integrity of digital media throughout its entire history.
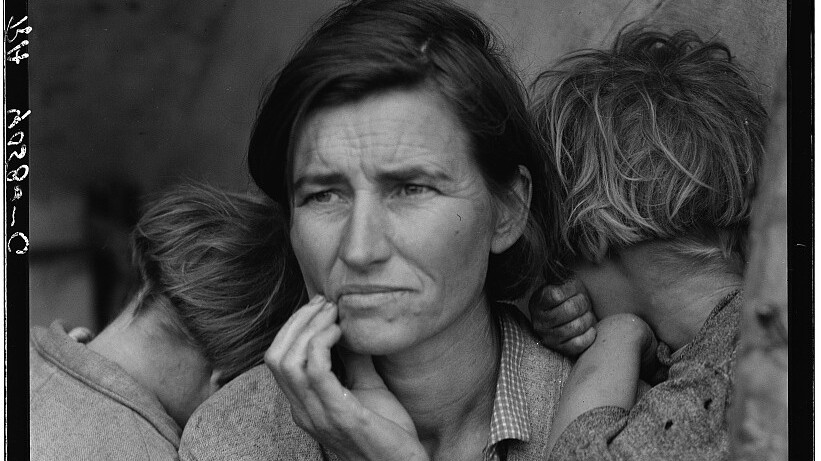
The Content Authenticity Initiative and the C2PA project
We were foundational partners in establishing digital trust, serving as early advisors to the Content Authenticity Initiative (CAI) and the C2PA project.
C2PA is an open technical standard designed to address misinformation by certifying the source and history, or provenance, of digital content.
Our team advised on the first whitepaper and contributed directly to writing the standard, culminating in our pioneering work with Reuters. This collaboration marked the first real-world implementation of the C2PA standard, setting a new benchmark for media authenticity.
The Framework in Practice
Capture
- Prove when and where you recorded photos or video by using a cryptographic root of trust in free mobile apps or professional cameras.
- Digitize physical media like 35mm film and add modern authenticity markers.
- Save social media posts and other webpages from disappearing, using tools that prove where you saw the content online.
Store
- Protect your published websites from censorship or digital decay by making portable backups on decentralized systems.
- Preserve investigative archives to ensure availability to selected researchers or the general public, complete with authenticity metadata.
- Future-proof public access to important digital collections by using new Web3 systems.
Verify
- Provide transparency to audiences, including an audit history of permissible edits.
- Redact sensitive information using cryptography to prove that nothing was inappropriately manipulated.
- Integrate verification tools into popular content management systems like WordPress and digital asset managers like Fotoware.
Capture
- Collect evidence in the field with cryptographically secure proof of location, time, and other critical metadata.
- Record webpages and other digital evidence using advanced standards to support admissibility.
- Incorporate independent witnesses to support claims about digital records.
Store
- Create tamper-evident seals around digital records by using advanced cryptography.
- Securely distribute backups to protect against cyber attacks.
- Support transitional justice by preserving digital evidence over generational timelines.
Verify
- Establish an auditable chain of custody for digital records.
- Share OSINT evidence with co-investigators along with authenticity markers.
- Prepare for the next generation of self-authenticating evidence and admissibility standards.
Capture
- Append existing digital collections with metadata that helps future researchers trust your digital records.
- Digitize physical collections with modern authenticity markers.
- Create authenticated scans of culturally important objects or scenes using VR approaches like photogrammetry and NeRFs.
Store
- Put archives on decentralized systems that overcome risk to your servers or other physical storage media.
- Establish long-term preservation plans to enlighten future generations.
Verify
- Apply tamper-evident cryptographic seals to thwart denialism.
- Use space-time proofs to ensure that your data hasn’t disappeared.
- Register collections using decentralized ledgers, proving the integrity of your collection.
Case Studies
Mar 3, 2026
Immersive Worlds for Documentary Filmmaking
Artificial intelligence is increasingly sophisticated in creating, understanding, and interacting in 3D environments. Also known as "spatial intelligence," this emerging field is being pioneered by world-class researchers and engineers around the world. As our own contribution to the field, Starling fellow Fred Grinstein has begun to explore how this use of generative AI might be applied to documentary filmmaking and non-fiction narrative works to engage audiences.
Oct 30, 2025
Beyond the Blackout: Documenting Atrocities in Tigray’s Forgotten War
Despite severed communications and infrastructure destruction, local journalists and healthcare professionals risked their lives to collect fragile digital and analog evidence of the 21st century's deadliest conflict.