Witness Servers
Journalism
Establishing institutional trust and technical corroboration for web evidence through decentralized, simultaneous crawling and cryptographic signatures.
YEAR
2024
PARTNERS
Webrecorder
FFDW
Harvard Library Innovation Lab
LINKS
– Concept note and Call for Contributions
– Our whitepaper on best practices in web archiving
The Problem
Minute, technical, cosmetic errors plague efforts of open source monitors who scour the Web and archive its content. In the context of legal investigations, these minor defects are considerable challenges to the reliability of the artifacts, and thus to the facts they aim to prove. Moreover, small organizations and individual investigators face a greater burden in arguing the probative weight of the material they collect than large, reputable, and established institutions.
The Solution
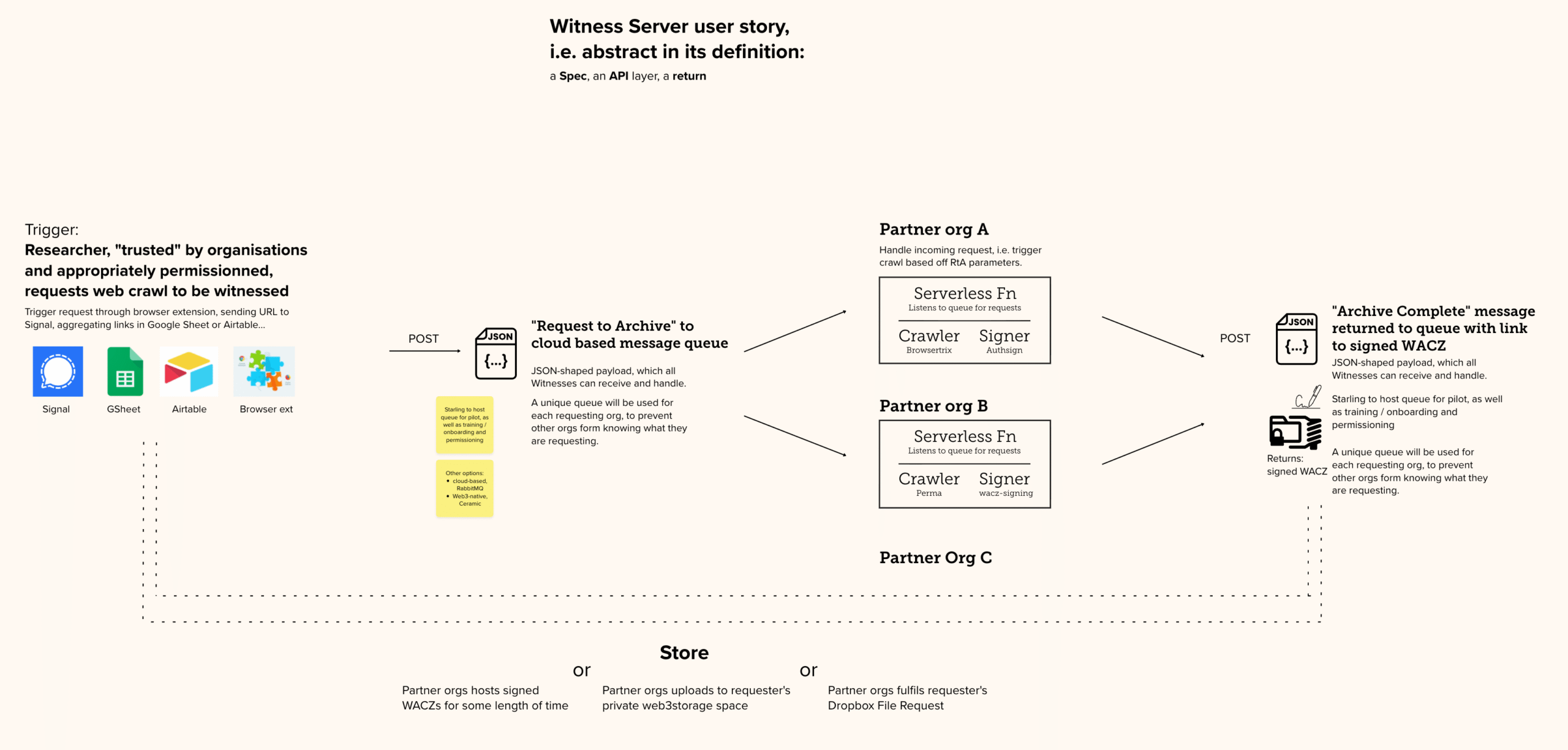
We are developing the Witness Server prototype To replicate social trust in digital capture by involving reputable institutions as simultaneous observers of the web.
In short: a Witness Server is a service hosted by an institution that conducts on-demand web crawls. When a researcher initiates a local capture, a request is simultaneously dispatched to several partner Witness Servers (such as Harvard LIL or the Atlantic Council). Each institution performs its own crawl independently using its own infrastructure, creating a multi-perspective record of the same web content at that exact moment.
The prototypes follow all our learnings about web archives, Including the use of the WACZ open source format which bundles signed and hashed files.
By comparing multiple institutional archives, investigators can explain away non-material “cosmetic” defects (like pop-up banners) and provide overwhelming proof of the core content’s authenticity.
REFERENCE IMPLEMENTATION
On Github →
SD Card Encryption
The Problem
Losing control of data can happen when journalists, historians, or legal experts least expect it. SD cards can be seized during border crossings, left behind in a taxi, or stolen from a hotel room. Evidence that has been captured on an SD card, and which has not yet been anonymized, might carry geolocation or identity information that can lead authorities or militants to vulnerable people being photographed or interviewed. Another risk to unencrypted data on an SD card is that it could be manipulated undetected when not in one’s possession, with files erased or modified.
Prototypes are being tested by Starling Lab that both encrypt and hide important data captured by those in the field.
The Solution
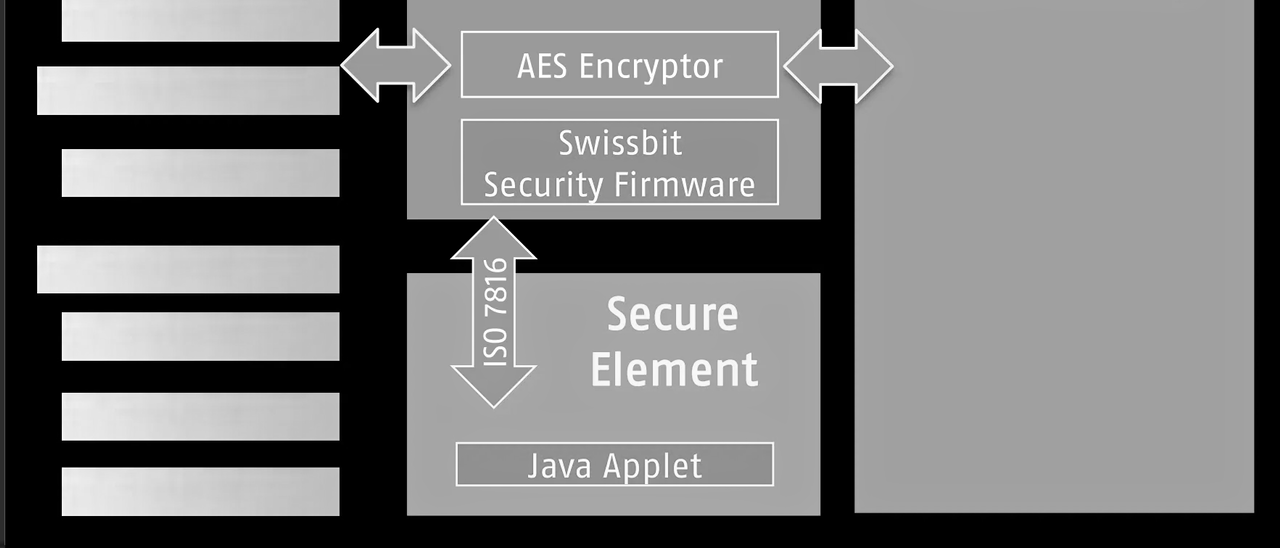
Starling Lab is collaborating with industry partners including Swissbit, a leader in secure storage, to deploy hardware-encrypted SD cards that protect media the moment it is written to disk. This prototype ensures that digital assets are secured independently of the camera’s software vulnerabilities.
The solution creates an “encrypted tunnel” between the camera lens and the storage medium. Swissbit’s hardware-based encryption automatically protects image and video data without requiring additional software on the capturing device, ensuring that media cannot be manipulated or viewed in transit.
To protect the safety of practitioners in the field, the prototype relies on hidden partitions on the SD card. Sensitive files are stored in a manner that makes them impossible for unauthorized parties to discover or decrypt (even if the physical card is seized and inspected), while providing a critical layer of plausible deniability.
5G Network Attestation
Journalism
Validating device metadata through fixed network infrastructure and reputable independent observers to establish trust in captured data.
YEAR
2024
PARTNERS
T-Mobile
Deutsche Telekom
Vonage
LINKS
– UN submission: Authenticity for human rights defenders in remote areas
The Problem
Mobile phones allow journalists to capture and transmit digital media with contextual information. However, since mobile phones are controlled by the end users, they permit manipulation of all forms of metadata, like GPS spoofers to fake location data. It is not enough for the location data collected by the Starling Capture app to be derived from metadata recorded solely by that mobile phone; it must be cross-referenced against the data signals transmitted and received by GPS, WiFi, cell towers, and/or beacons so that there is third-party attestations that the mobile phone is reporting location data correctly.
The Solution
Starling Lab is moving the “trust anchor” from the individual handset to the fixed infrastructure of the 5G network. By utilizing the C1 Mini framework, we enable a new class of “Network Attestations” that treat the mobile carrier as a reputable, independent witness to the capture of digital evidence.
The core of this prototype is the C1 Mini application, which leverages the standardized CAMARA APIs (exposed via Vonage and Deutsche Telekom). Instead of relying on easily phished 2FA codes, the system uses Silent Network Authentication (SNA). This process cryptographically verifies the unique identity of the subscriber’s SIM card directly with the carrier’s core network in the background. This ensures that the data registration request is coming from a legitimate, physical device authenticated by the network operator, not a spoofed virtual instance.
To support practitioners in remote or high-risk areas, the C1 Mini facilitates the “expedited registration” of asset fingerprints. Users can transmit the cryptographic hash of a photo or video via a secure SMS tunnel to a Starling registration server. This allows for a “proof of existence” to be anchored on a decentralized ledger (such as Solana or Hedera) even in low-bandwidth environments where uploading large raw files is impossible. This creates a tamper-evident timestamp that is significantly harder to manipulate than a device’s internal system clock.
This creates a multi-layered defense against disinformation: a hardware-signed image, a network-verified location, and a decentralized timestamp, all established at the point of capture.
Authenticated Camera Capture
Journalism
Authenticated Camera Capture establishes a root of trust at the absolute moment of creation by embedding cryptographically signed metadata directly into media files. Spearheaded by the C2PA standard and major manufacturers like Leica, Sony, and Nikon, these prototypes shift the verification paradigm from reactive deepfake detection to affirmative proof of origin.
They rely on hardware-backed secure enclaves to sign images with private keys, ensuring that every photo or video carries a tamper-evident record – a “birth certificate” – that traces back to the original sensor and time of capture.
YEAR
2020-26
PARTNERS
Canon Cameras
Reuters
Adobe (Content Authenticity Initiative)
Leica Cameras
The Problem
Photographs circulate globally, often years after capture, stripped of metadata and decontextualized. Viewers are left unsure of who captured an image, or when and where events occurred. This vulnerability is exploited by bad actors using AI to manipulate content, giving rise to the “Liar’s Dividend” where even authentic evidence can be dismissed as a deepfake.
Furthermore, existing “companion device” workflows (pairing a camera to a smartphone) often suffer from field challenges like Wi-Fi connection issues, battery drain, and the technical complexity of managing multiple devices in high-pressure conflict zones.
Finally, a core challenge in authenticating news media is accounting for the reality of permissible edits. In photojournalism, editing a raw file is not inherently deceptive; it is a necessary step in the editorial process. Photo editors routinely crop images to fit specific publication layouts, adjust exposure or color balance to ensure visual clarity, and append critical contextual metadata such as captions, location data, and copyright credits. While these routine, ethical adjustments do not alter the factual truth of the scene, they inherently change the digital fingerprint of the file.
CASE STUDIES
– Canon-Reuters Collaboration on Preserving Trust in Photojournalism
LINKS
– The Canon-Reuters prototype POC
– Petapixel: Canon and Reuters develop new photo authentication technology
– On offline benefits: our submission to the UN Special Rapporteur on Human Rights Defenders
The Solution
We experimented with several authenticated camera-centric workflows that enabled professional cameras to natively generate and sign C2PA manifests upon capture. By integrating signing keys into hardware-based secure enclaves (Trusted Platform Modules), the system ensures that private keys cannot be extracted or cloned, establishing a permanent “root-of-trust” within the device’s silicon.
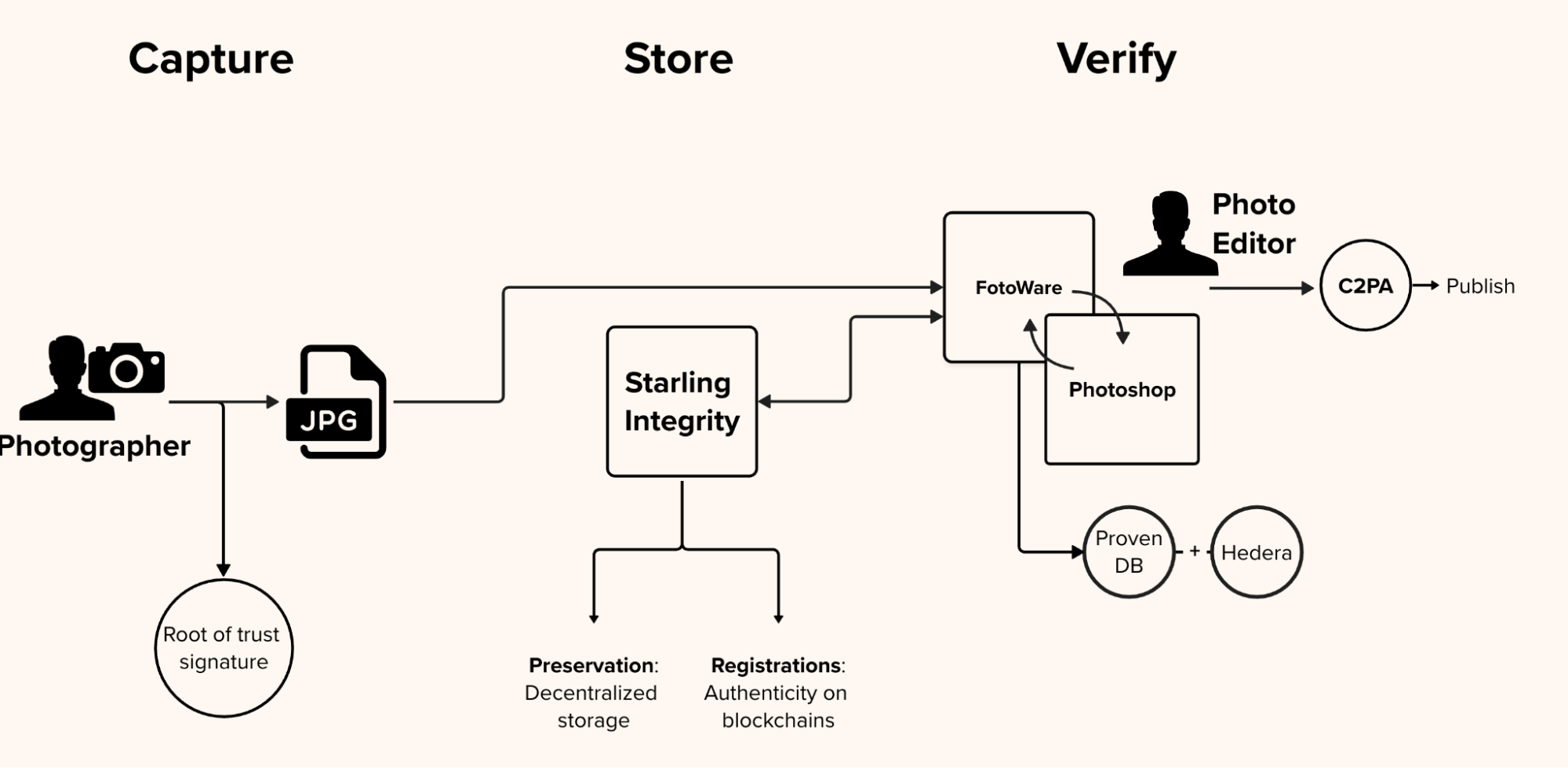
From lens to a reader’s screen, this “glass-to-glass” chain of custody, pioneered with specialized firmware for Canon devices, injects rich, signed metadata—including server-acquired timestamps and GPS coordinates—directly into JPEG files. This ensures that every asset carries its own proof of integrity, allowing audiences to audit the steps taken from the initial shutter click to publication through standard inspection tools.
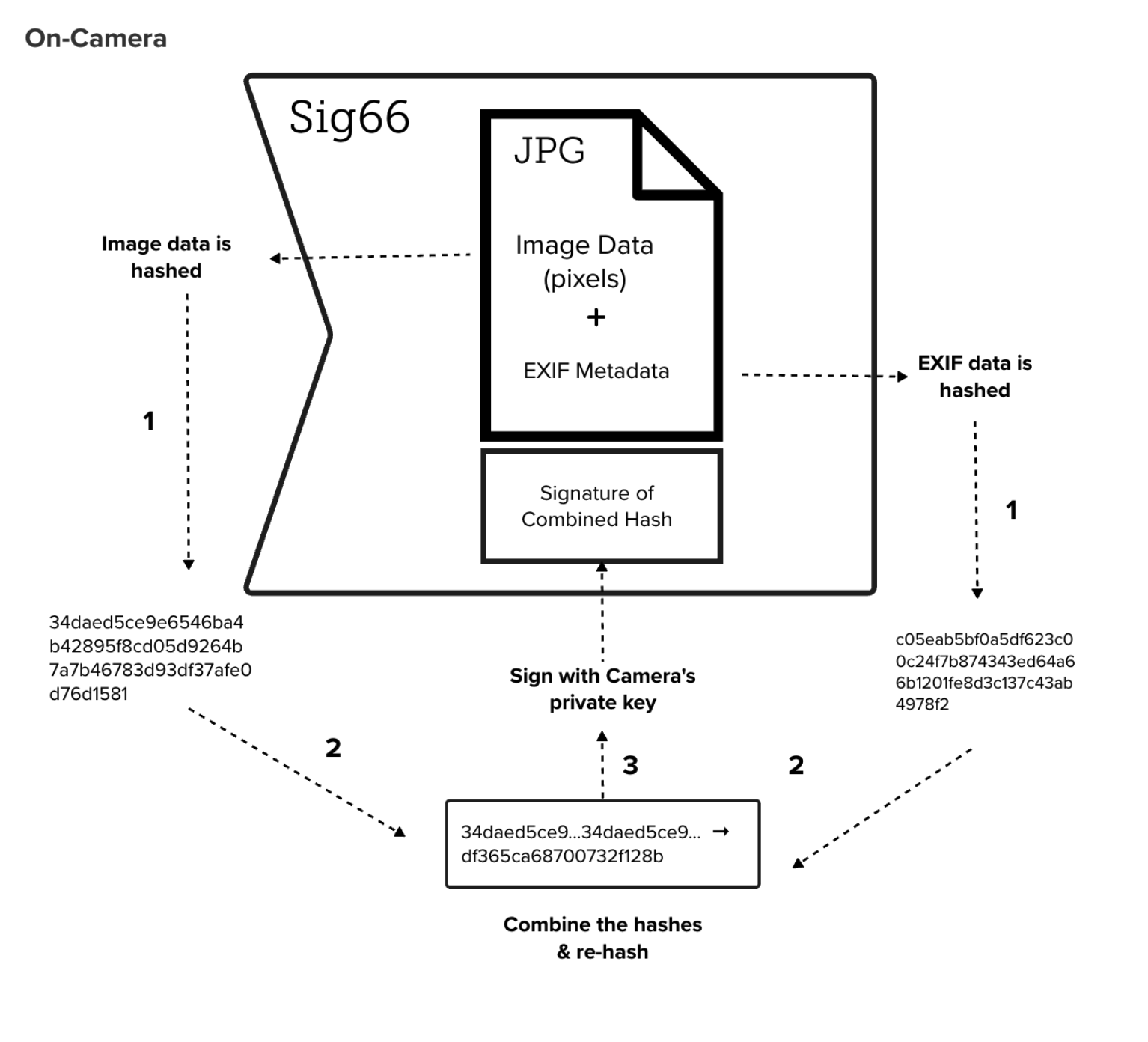
The on-camera process. The firmware computes a combination hash of image pixels and EXIF metadata, signs it with a unique factory-programmed private key, and appends the signature to the JPEG data.
To bridge the gap between capture and publication, the Starling Integrity backend tracks permissible modifications in the background. Using webhooks within the Fotoware CMS, every edit, from caption updates to Photoshop adjustments, is recorded as a new entry in a C2PA manifest and anchored to the Hedera public ledger. This creates a mathematically provable, immutable audit trail that survives the industrial scale processing of a global newsroom.
ProofMode Authentication
Journalism
Experimenting with the integration of lightweight, forensic-grade verification into secure messaging workflows.
YEAR
2022-23
PARTNERS
Guardian Project
Hala Systems
Signal Messenger
LINKS
– Case Study: The Proof’s in your Pocket
– From the Guardian Project team: Integrating libProofMode
The Problem
Citizen-captured photos and videos are becoming powerful reporting tools. But faked footage, or footage with missing crucial context, threatens to break the trust between a newsroom and its audience. Professional journalists thus need to be able to vet the footage captured by citizens to ensure that the files sent in by citizen journalists are authentic and accurate representations of the depicted event.
The Solution
ProofMode (developed by the Guardian Project) promotes trust by providing a means to strongly authenticate multimedia at the point of capture.
We were the first to experiment with its distribution as a software library, under the name libProofMode. Starling Lab developed a bespoke fork of Signal Messenger that embeds authentication as a native feature. Users of this custom app can snap photographs directly within the app, which automatically generates a unique OpenPGP key pair to sign the media and its surrounding sensor metadata, including location, time, and cell tower environment.
At capture, media hashes are automatically registered on OpenTimestamps to create a “proof of existence” on the Bitcoin ledger. To ensure secure transport, every file sent via Signal triggers an automated MobileCoin micro-transaction; the first 16 digits of the “proof hash” are embedded in the transaction memo, allowing the recipient to cryptographically verify that the file received exactly matches the file captured in the field.
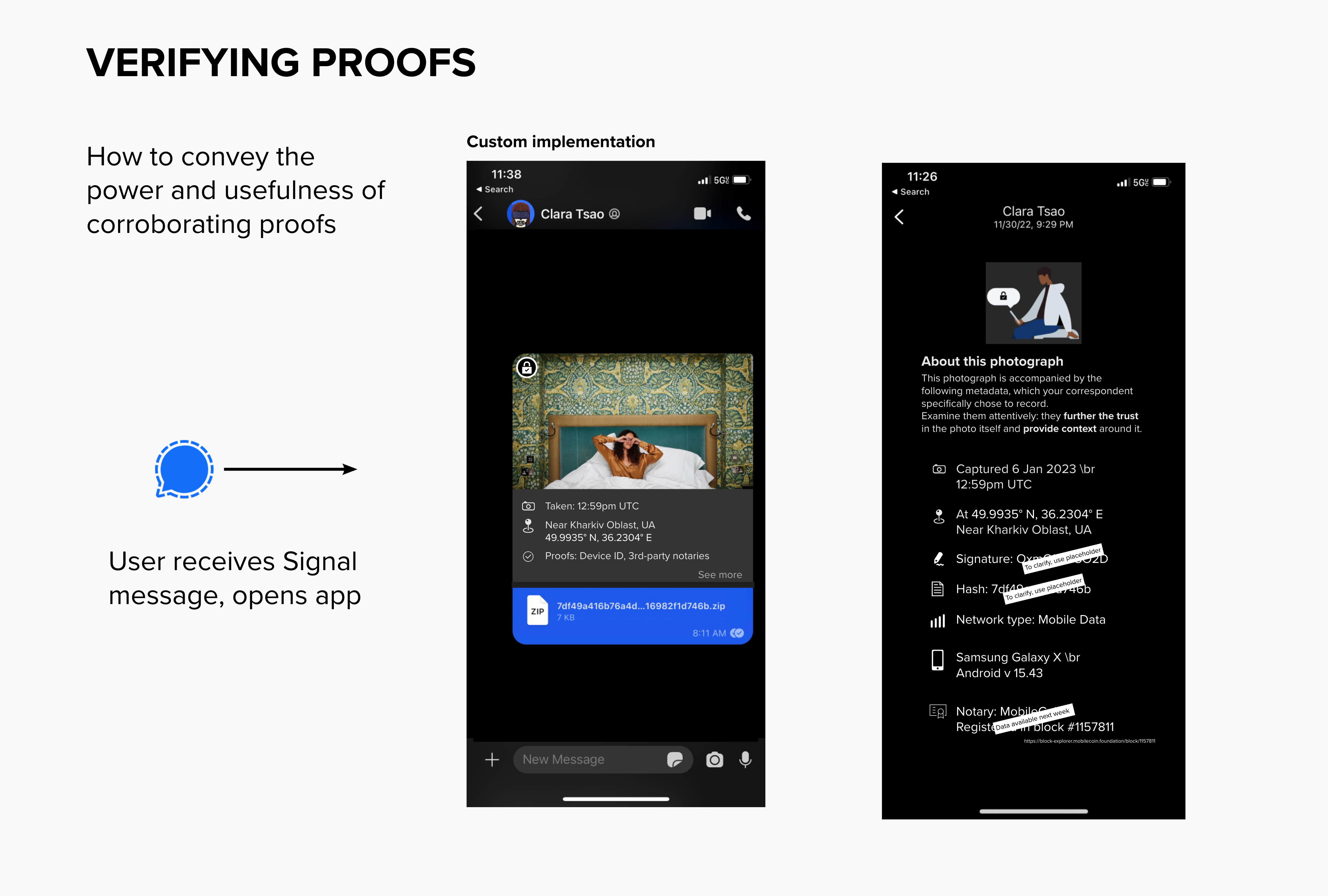
To reduce the burden on legal and journalistic investigators, the prototype features a visual layer of UI inside the Signal conversation view. Both sender and recipient can instantly surface contextual metadata snapshots and check them against immutable third-party record holders, such as the LikeCoin or Avalanche blockchains. This “glass-to-glass” approach ensures that technical authenticity markers are accessible and legible to the field practitioners who need them most.
HIGHLIGHT
In response to the shelling of Kharkiv’s schools, Starling Lab launched Project Dokaz (“Proof”). Local photographers were equipped with the custom Signal app to conduct “preventative documentation” in support of the Safe Schools Declaration. By capturing regular rounds of authenticated imagery, the team was able to verify the absence of military co-option at these sites, confirming their protected status under international law.
Read mode about Project Dokaz →
Companion Secure Enclave Authentication
Journalism
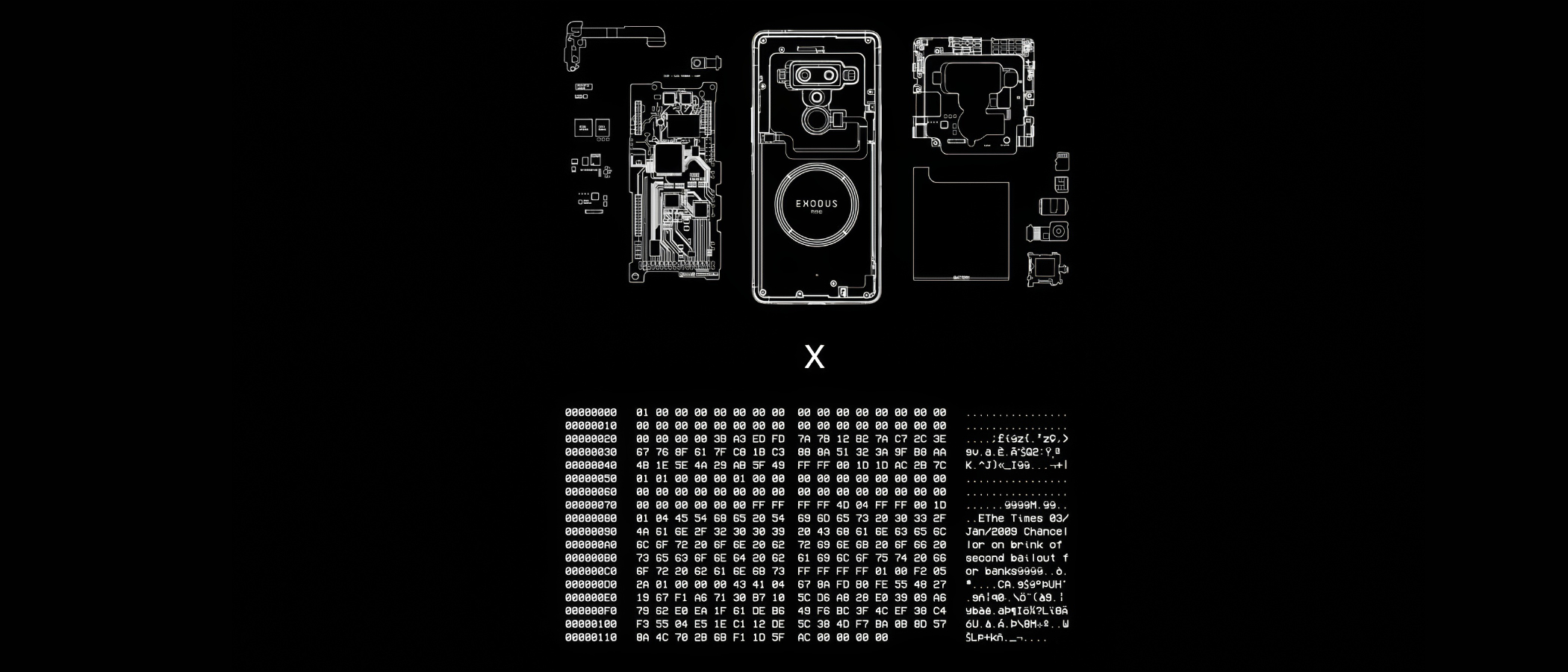
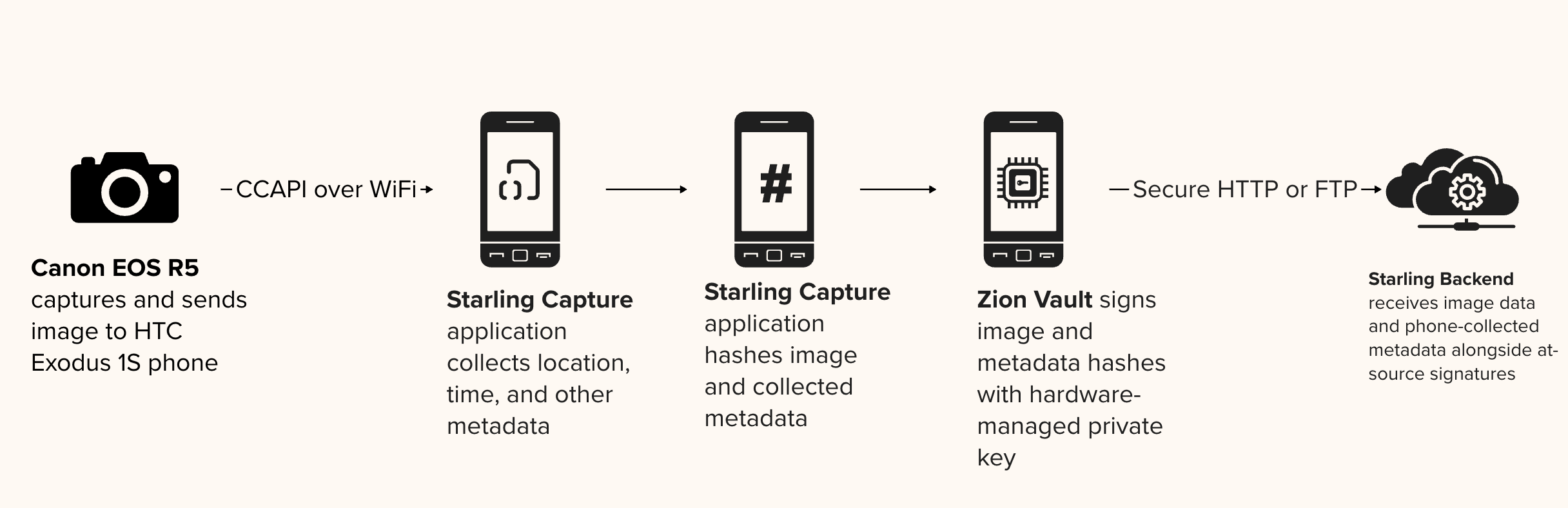
Companion Secure Enclave Authentication provides a “secure bridge” for professional photojournalism by tethering standalone cameras to mobile devices with hardware-level security. By pairing a professional camera with a smartphone’s secure enclave (such as the HTC Zion Vault), this prototype establishes a root-of-trust for images that traditional cameras cannot natively sign.
This method ensures that every photo is cryptographically sealed with a unique digital signature and sensor-rich metadata at the exact location and time of capture, creating an unalterable record of reality.
YEAR
2020-24
PARTNERS
HTC
Inside Climate News
Bay City News
Numbers
The Problem
Most professional cameras used in the field lack the internal hardware necessary to cryptographically sign assets or protect signing keys. Without a tamper-evident seal, digital photographs and their metadata (such as GPS and timestamps) are vulnerable to manipulation by AI tools or bad actors.
As these unverified images circulate, they lose their essential context, making it nearly impossible to determine the original version or defend against cheap- or deepfake allegations that distort the facts reported by photojournalists.
The Solution
Starling Lab pioneered a workflow that utilizes the hardware secure enclave of a companion smartphone to sign media from high-end cameras.
By tethering a professional camera (such as a Canon R5) to an HTC Exodus 1S phone via WiFi or USB, the Starling Capture app (co-developed with Numbers) instantly receives captured media. The phone’s Zion Vault hardware-secured signer then generates a cryptographic hash of the image and its associated sensor data (barometer, gyroscope, and GPS), sealing it with a private key that never leaves the device’s protected silicon.
CASE STUDIES
Stockton Homelessness: In 2022, Bay City News photojournalists documented the homelessness crisis in Stockton, CA, using Canon R5 cameras paired with HTC devices. These “authenticated time capsules” provided a verifiable record that challenged official statements and misinformation surrounding local funding disparities.
Brazil Pantanal: Photographer Felipe Albarenga documented the 2020 wildfires in the world’s largest wetland. By using the companion secure enclave, Albarenga created a tamper-evident archive of the devastation that could withstand the propaganda and denialism prevalent during the Brazilian presidential election.
Authenticated Web Archives
Journalism
Accurate, reliable, simple to use, and secure workflows for archiving web content.
The Problem
Online content disappears rapidly, erasing critical evidence for investigative journalism, accountability, and cultural preservation. Social media platforms and hosting providers face pressure to implement stricter content moderation, with automated filters and human moderators making rapid decisions about what stays online. Records documenting potential crimes – especially those with violent imagery – risk being permanently deleted. Restoring content is often impossible: original posters may be arrested, lose device access, or no longer be alive when investigations begin.
Existing archiving methods face three challenges: platforms actively block automated crawlers, preserved content lacks the cryptographic verification and chain-of-custody documentation required for legal admissibility, and saved material becomes unsearchable across large collections.
JOURNALISM
Strong web archives provide a tamper-evident way to capture online evidence, safeguarding reporting against censorship and the erosion of digital sources.
HISTORY
These archives create a trustworthy and resilient collection of digital primary sources, ensuring that the ephemeral nature of the web does not erase our collective memory.
LAW
This technology establishes an unbreakable digital chain of custody, transforming fleeting web content into verifiable, court-admissible evidence.
The Solution
Starling is developing workflows using open source software for archiving web content to ensure the preserved archives are accurate and reliable, taking into consideration the sensitivity of the data. We draw from the considerable expertise deployed by national libraries and legal deposits from around the world.
Our case studies have experimented with forensically-sound web archiving, focusing on capturing broad contextual snapshots of web material.
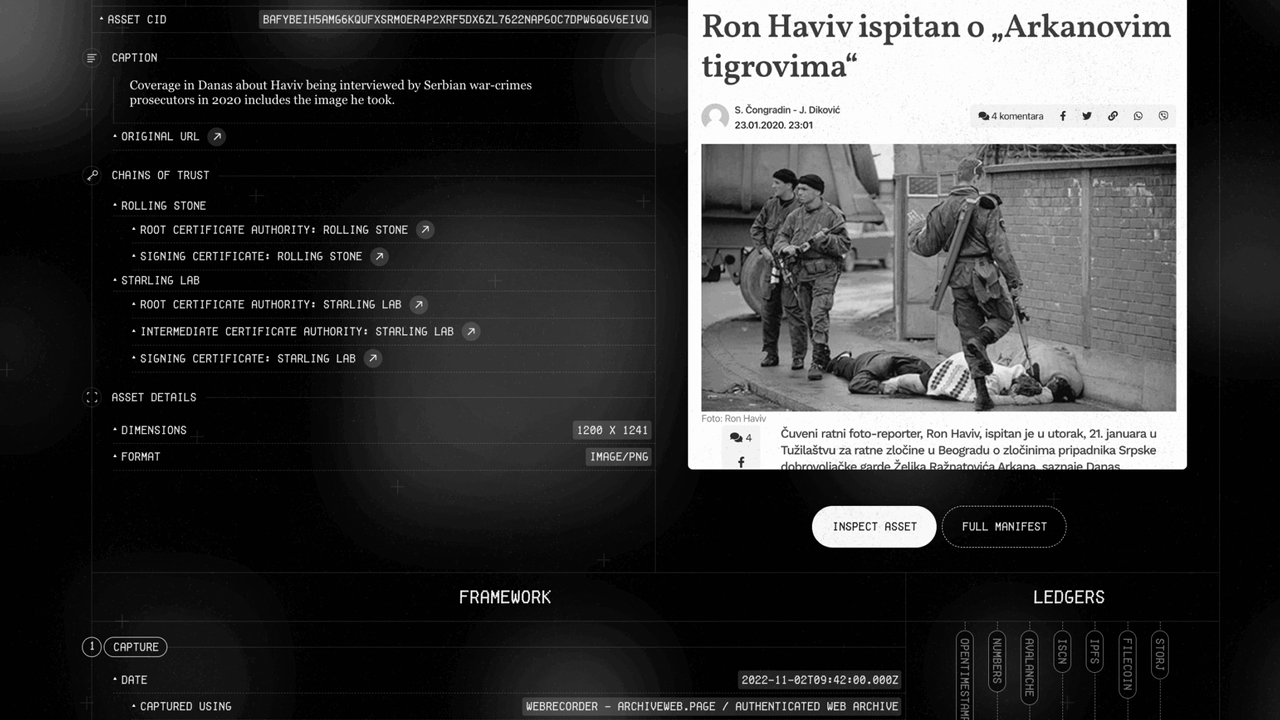
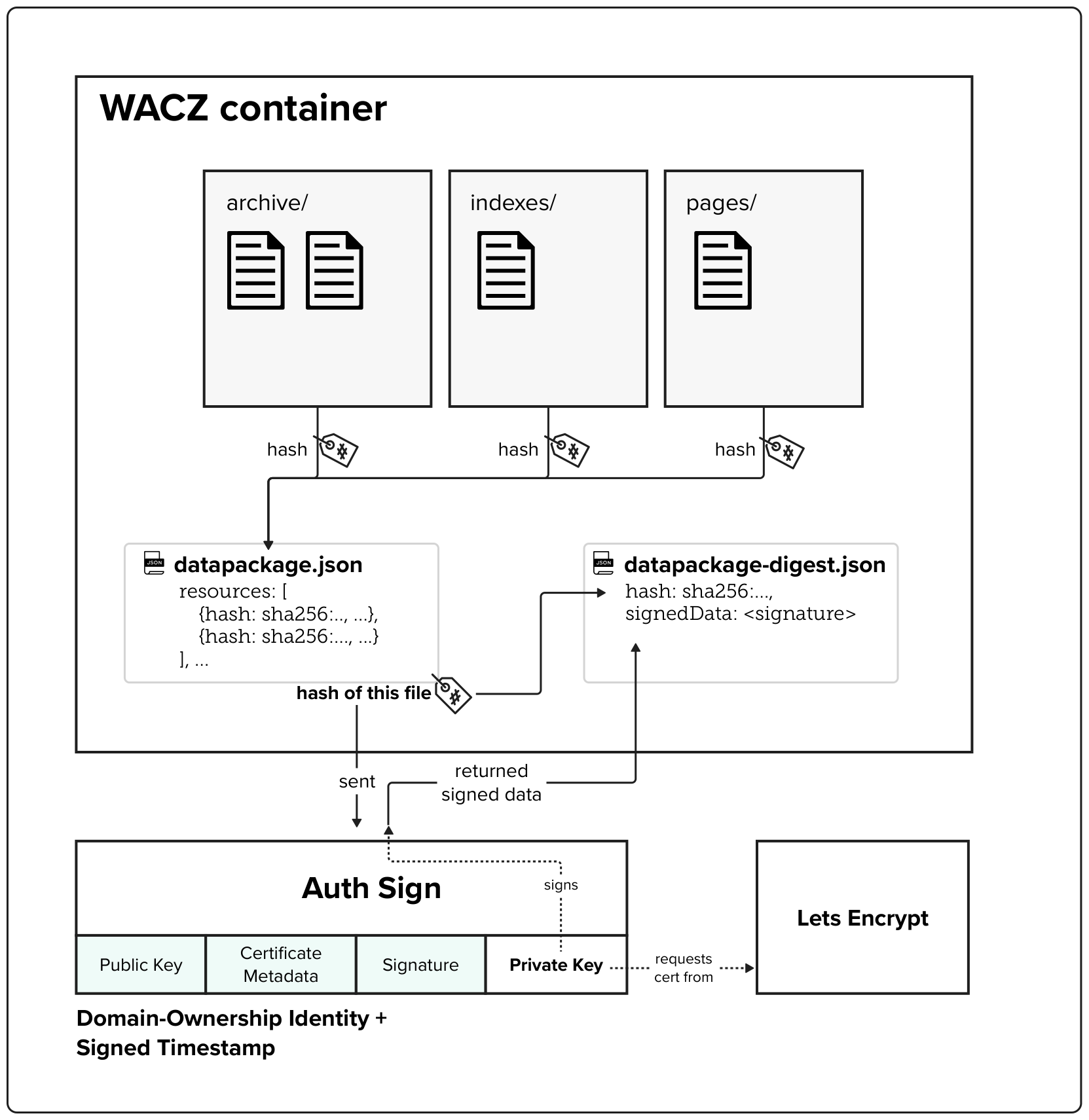
The WACZ standard and file format
The Web Archive Collection Zipped (WACZ) standard provides a portable packaging format for web archives that bundles WARC data, indexes, metadata, and verification information into a single ZIP file. Unlike traditional WARC files that lack contextual information and require complex server infrastructure for viewing, WACZ enables efficient browser-based rendering by organizing content with indexes that allow random access to only the data needed for each page.
Built-in Integrity Through Cryptographic Hashing
Every WACZ file includes a datapackage.json manifest that contains cryptographic hashes of all resources within the archive, providing a verifiable fingerprint to detect any unauthorized modifications. This hash-based integrity checking ensures that archived content remains tamper-evident throughout its lifecycle.
Authentication Through Digital Signatures
The specification adds optional authentication capabilities by allowing creators to digitally sign archives – notably using TLS certificates. These signatures validate both the identity of the entity creating the archive (using X.509 SSL certificates) and establish a trusted timestamp for when the capture occurred.
Ann Grimes
CONTACT
Ann Grimes
Director, Journalism Fellowships
Ann is a veteran journalist, she has held senior editorial positions at The Wall Street Journal and The Washington Post. Earlier, she served as Director of Stanford University’s Graduate Program in Journalism, co-directed the bi-coastal Brown Institute for Media Innovation, anchored at Stanford’s School of Engineering and Columbia University’s Graduate School of Journalism. She also served as interim director of Columbia’s Knight-Bagehot Fellowship in Economics and Business Journalism. She earned her MA from the University of Chicago, BA from Georgetown, and was a John S. Knight Fellow at Stanford.
Ann Grimes currently serves as Director, Journalism Fellowships at the Starling Lab for Data Integrity at Stanford and USC. She works with journalists and students at Stanford University tearching classes at the intersection of media and technology in Stanford’s Department of Computer Science, Graduate School of Business, the Hasso Plattner School of Design (the d.school), and Department of Communication. She is the establishes and guides the journalism projects and fellowships through Starling Labs’ Capture, Store, Verify Framework and serves as an advisor, editor, and mentor for the journalism fellows.
Work at Starling Lab
We encourage practitioners, academics and technologists to work together to address complex problems and find opportunities at the intersections of media technology
Jonathan Dotan
CONTACT
Jonathan Dotan
Founding Director
Jonathan Dotan is the founding director of The Starling Lab where he leads applied research on AI, cryptography, and human rights. He is a fellow at the Stanford Compression Forum and Stanford’s Center for Blockchain Research, as well as an innovation fellow at the USC Shoah Foundation. He brings to Starling over 25 years of experience navigating the intersections of media, tech, and policy as a c-level tech executive, producer, and investor.

Work at Starling Lab
We encourage practitioners, academics and technologists to work together to address complex problems and find opportunities at the intersections of media technology
Preserving History in the Age of AI: The Christopher Morris Panama Archive

Preserving History in the Age of AI: The Christopher Morris Panama Archive
How the Authenticated Attributes protocol creates an immutable 'web of context' to save a generation of photojournalism from being lost to AI or the archive.
Starling LabReading Time: 5min

Prototypes
Share
Contents
Background
Fellowship Projects and Awards
Background
We live in an age of digital excess but are losing the records of our past. Photojournalists amass millions of images, but without the support of repositories or preservation systems, this institutional memory is at risk of being lost or dismissed as AI-generated – a phenomenon known as "the Liar's Dividend". Over a lifetime, a photojournalist can amass thousands and thousands of images. This volume creates a massive preservation challenge; Adam Silvia, a photography curator at the Library of Congress, notes they are approached by at least one photojournalist offering an archive every week, but the Library can only acquire just one archive every five years, creating a critical bottleneck.
The rise of generative AI further complicates this reality. As Dr. Manny Ahmed, CEO of OpenOrigins, writes: “If you cannot prove that a piece of media existed before the AI inflection point, you can never again prove that it is real. This effectively drives the value of any archive to zero. Without trust in content, an archive holds no value as a documentation of history”.
To confront this challenge, Starling Lab is moving beyond the industry standard of verifying single image files. We are experimenting with a Web of Context – a shift from asset integrity to relational integrity. By cryptographically linking an image not just to its own metadata, but to the historical documents, assignment cables, and peer testimonies surrounding it, we create a defensive layer of proof. All assets present corroborate and support each other.

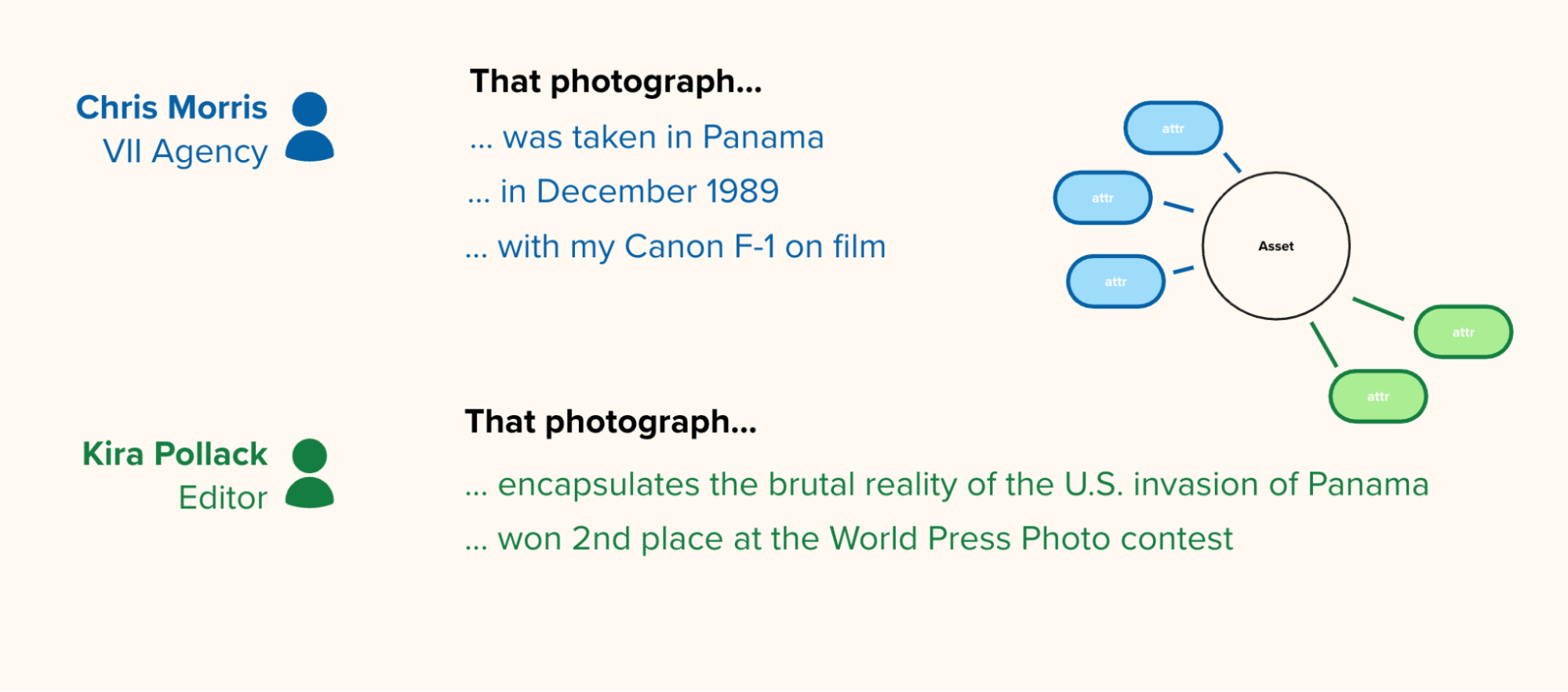
We partnered with two key figures:
- Kira Pollack: Starling Distinguished Fellow and former photo director at Time and Vanity Fair.
- Christopher Morris: An acclaimed conflict photographer whose nearly 700,000 images, taken over a 40-year career, are currently stored in filing cabinets "prepped to be loaded into a U-Haul truck very quickly, within one hour" due to environmental threats like hurricanes.
Below is a short documentary film, narrated by Chris Morris recollecting his experience photographing the scenes, and placing the images in context. Warning: it contains graphic and violent images.
http://starlinglab.org/wp-content/uploads/2026/04/CHRISTOPHER_MORRIS_ROUGH_CUT_v2-993021578.webm
Contents
Context
FrameworkTechnologyLearningsArchive
Context
The project focuses on a specific historical event: the 1989 U.S. invasion of Panama. The investigation centers on Morris's iconic image, "Soldier Screaming", which captures Sergeant Raymond D. Cabacar of the U.S. Army and the 1/250th of a second it took to capture.
To prove the image's authenticity, the scope of the project included digitizing and connecting a vast inventory of assets. Supporting documents for the image detail Sergeant Cabacar's heroic actions on the day of the firefight (Dec. 22, 1989), where he saved a woman and two children while under heavy enemy fire – actions for which he was approved for a Bronze Star with Valor.
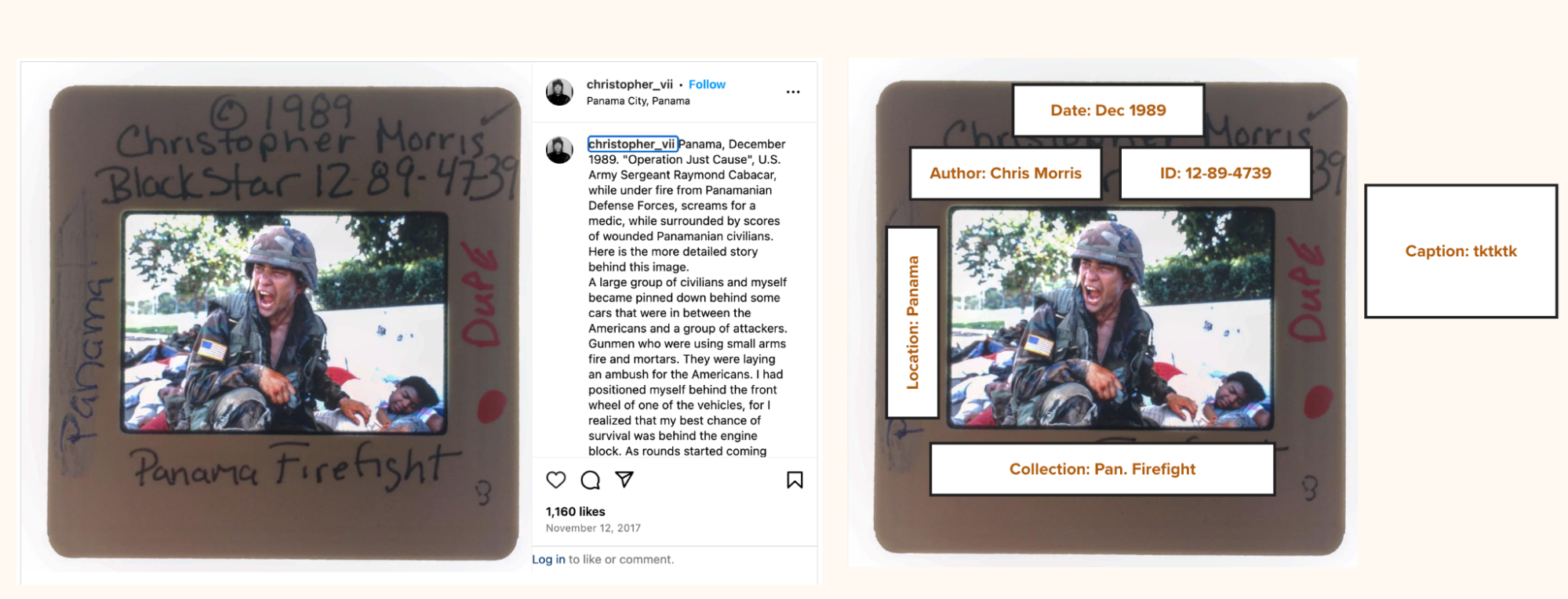
By moving beyond the single frame, the project captures the broader narrative. Specifically, the archive connects 131 Ektachrome stills, audio testimony of Morris describing sequences, related articles like Time magazine scans, and photos of the tools of his trade, such as his camera, passport stamps, and radio scanners.
Contents
Framework
Framework
The Challenge
In the realm of digital provenance, the industry has largely focused on verifying single assets: proving that a specific photograph was captured by a specific device at a specific time. While this is a critical first step, historical archives present a much more complex challenge: the problem of context.
An isolated photograph, even if cryptographically signed, is vulnerable to misattribution. If a bad actor strips a photo's caption or falsely claims an image of the 1989 Panama invasion actually depicts a different conflict entirely, a simple digital signature on the pixels cannot defend the narrative. The truth of a photograph relies on the "web of context" surrounding it: the contact sheets showing the frames before and after, the press passes proving the photographer’s access, and the audio testimony of the photographer themselves.
The challenge for Starling Lab was twofold:
- Preservation: How do we transition a highly vulnerable, analog archive (currently sitting in filing cabinets susceptible to natural disasters) into a decentralized, immutable digital format before it is lost?
- Contextual Verification: How might we cryptographically bind a hero image (like "Soldier Screaming") to its supporting evidence, ensuring that the relationships between these assets cannot be severed or manipulated by malicious actors or generative AI in the future?
We needed to build a system that didn't just store files, but securely preserved the complex, relational truth of the photographer's experience.
Contents
Framework
The Prototype
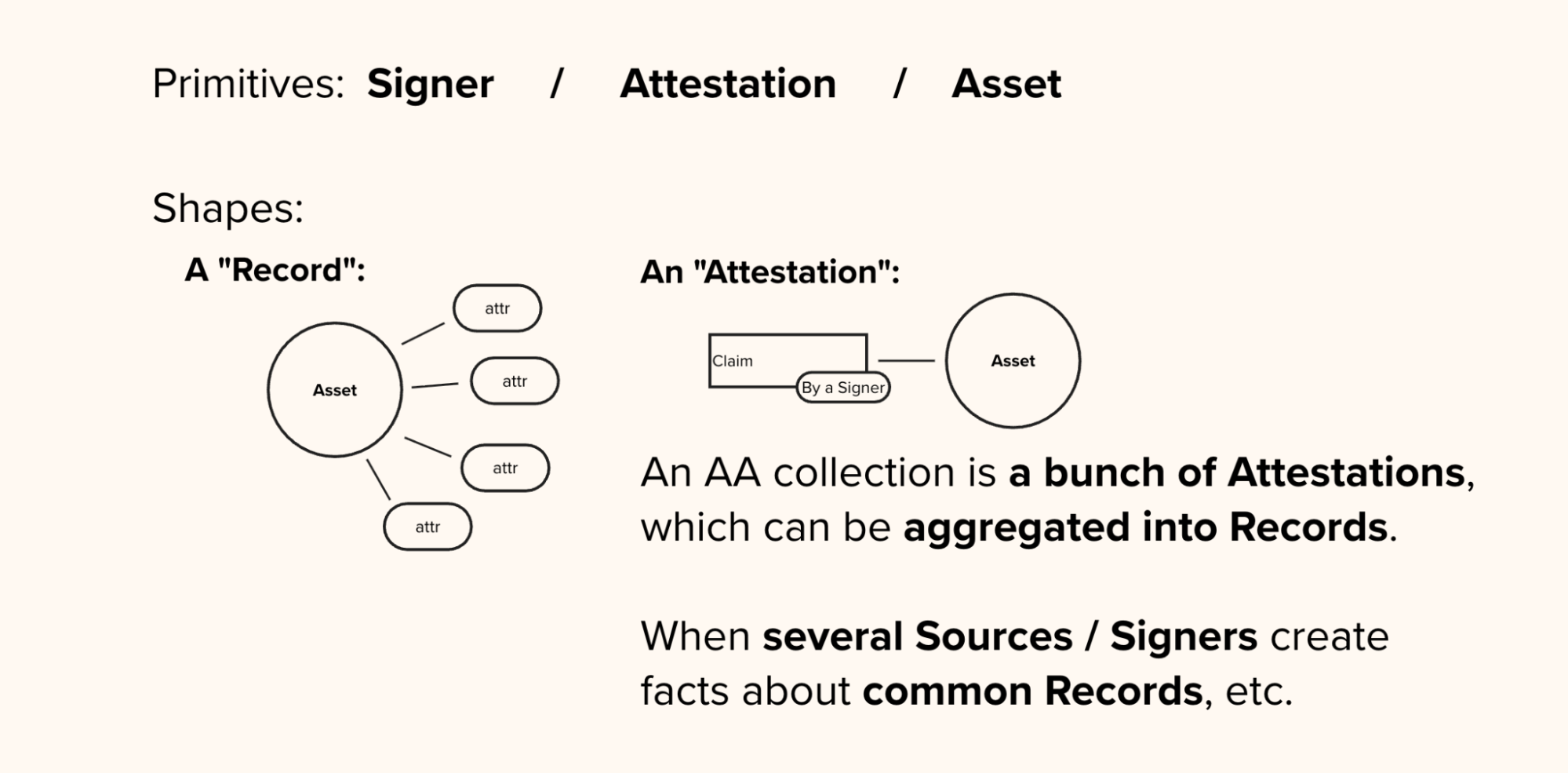
To solve the challenge of contextual verification, Starling Lab moved beyond single-file authentication to develop the Authenticated Attributes (AA) protocol and an accompanying web interface.
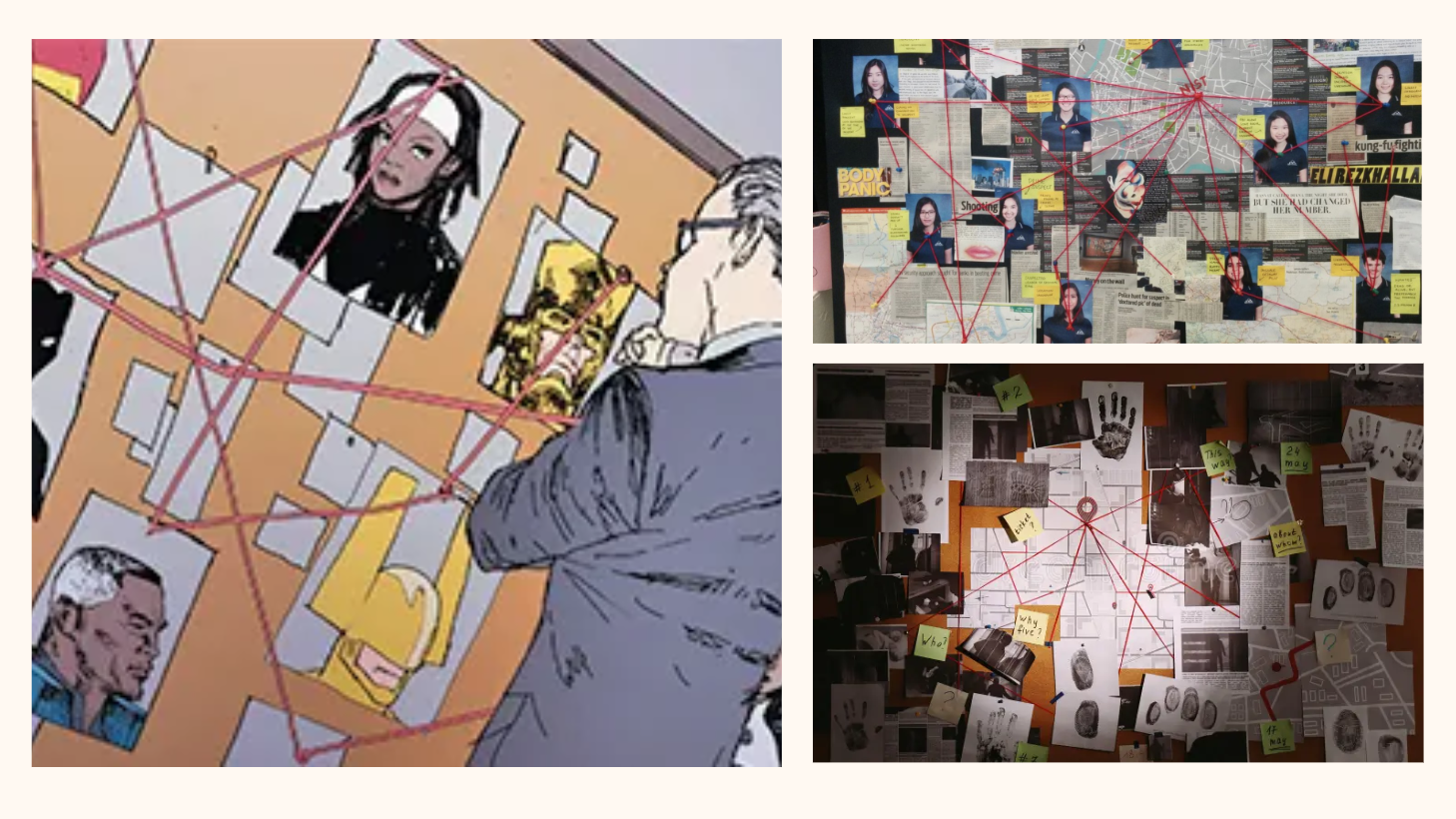
A "Web of Context" Concept
Instead of a linear article or a traditional folder of files, the prototype is a dynamic, "guided graph" explorer. It addresses the "Liar's Dividend" by proving not just that a photo was taken, but how it relates to a supporting body of evidence.
Using the AA protocol, we cryptographically bound the hero image "Soldier Screaming" to its "parent" contact sheet, Christopher Morris’s audio testimony, and his scanned press credentials. If a bad actor attempts to strip the metadata or isolate the image to change its narrative, the cryptographic bond is broken, immediately signaling that the context has been tampered with.
Behind the scenes, the prototype is powered by a custom ingestion pipeline that moves away from traditional, editable databases. Instead, every piece of metadata (an "attribute"), such as "is a contact sheet of" or "was captured by", is individually signed and recorded on an append-only cryptographic ledger. This creates an immutable, verifiable history of the archive's creation. (A detailed breakdown of the cryptographic and storage infrastructure is available in the Technology section below).
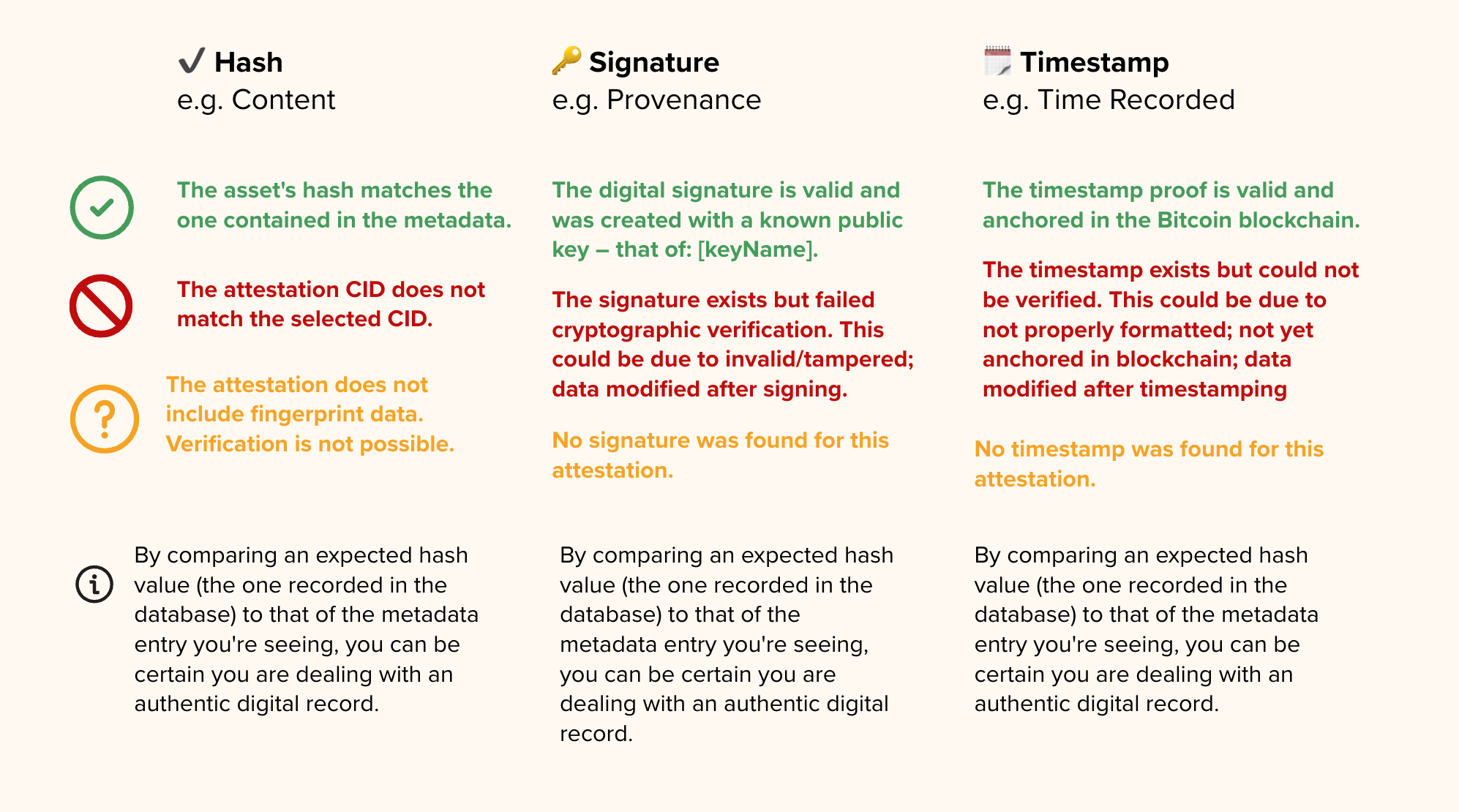
A "Traffic Light" System for Trust
The front end of the prototype renders this complex data graph for a non-technical audience. It balances open exploration with a guided narrative.
To make the cryptography intuitive, we implemented a "traffic light" verification system that evaluates Integrity (has the file changed?), Identity (who signed it?), and Time (when was it secured?).
Contents
Technology
Technology
To establish a resilient and verifiable digital archive, the project relied on a custom technology stack that moves away from centralized, easily manipulated systems in favor of cryptography and decentralized networks. We organize this pipeline into three distinct phases: Capture, Store, and Verify.
Capture: Digitizing the Analog Record
The first step was to bridge the gap between Christopher Morris’s physical archive and the digital realm without losing the chain of custody.
The first step in preserving Christopher Morris’s physical archive involved bridging the gap to the digital realm without losing the chain of custody. The team digitized 131 Ektachrome still images, along with supporting analog assets like contact sheets, passport stamps, and newly recorded audio testimony.
As these analog records were digitized, they were immediately processed through a custom command-line tool known as the starling-integrity-cli. At the exact moment of ingestion, this interface generated a SHA-256 cryptographic hash for each file. This hash acts as a unique digital fingerprint, ensuring that if even a single pixel or audio byte is altered in the future, the hash will completely change and instantly flag the file as tampered.
The output of a successful ingestion captures this fingerprint alongside the file's essential provenance metadata in a single atomic record:
{
"file_name": "panama_001.tif",
"media_type": "image/tiff",
"file_size": 47382016,
"sha256": "a3f4e1...c9d2b8",
"blake3": "9e2c47...f1a034",
"md5": "d41d8c...98f00b",
"time_created": "1989-12-22T06:14:00Z",
"last_modified": "1989-12-22T06:14:00Z",
"asset_origin_id": "/panama-archive/ektachrome/panama_001.tif",
"asset_origin_type": ["folder"],
"project_id": "christopher-morris-panama"
}
Store: Decentralized Preservation
Historical archives are highly susceptible to "link rot" (when a web page or file simply disappears) and single points of failure (like a centralized server crashing or being hacked). To guarantee the archive's longevity, we utilized decentralized storage networks.
Because historical archives are highly susceptible to "link rot" and the single points of failure inherent in centralized servers, the project utilized decentralized storage networks to guarantee the archive's longevity. Instead of storing files at a specific location or URL, which can easily be broken, the assets are sharded and stored on the InterPlanetary File System (IPFS) using Pinata. IPFS uses content addressing, which means files are located based on their cryptographic hash rather than where they are hosted.
For resilient, long-term archiving, this data is backed up on Filecoin, a decentralized network that uses cryptographic proofs to guarantee that storage providers are securely holding the data over time.
Finally, the root hash of each asset is registered on public, energy-efficient blockchains, such as Avalanche and Near, via the Numbers Protocol to create a permanent, public receipt of the file's existence.
Each successful registration is itself logged back into the Authenticated Attributes database as a signed registrations entry, closing the loop between the file, its metadata, and its public receipt:
{
"chain": "numbers",
"attrs": ["media_type", "sha256", "time_created"],
"data": {
"txHash": "0x78d30a...8f968d625",
"assetCid": "bafybeibqzv26nf3i5lz...",
"assetTreeCid": "bafkreigeszf54jrgvlt...",
"order_id": "4dd7cd58-94f6-4aaa-8f24-b10bd41235d5"
}
}
Verify: Establishing the Chain of Trust
The verification phase is where the "Web of Context" is cryptographically sealed, allowing anyone to independently audit the archive's integrity. The archive’s metadata (which provides the critical context defining how the photos, audio, and documents relate to each other) is stored using Hyperbee. Unlike traditional SQL databases, Hyperbee is a peer-to-peer, append-only B-tree database where historical entries cannot be overwritten; any change is added as a new, visible entry to create a transparent audit trail. Every attribute added to this database is signed using Ed25519 digital signatures via the Noble Crypto library, firmly binding the metadata to the recognized identity of the photographer or archiving institution.
Each piece of metadata – called an attribute – is stored not as a simple key-value pair in a traditional database, but as a full attestation record. Below is a simplified example of what the time_created attribute looks like for a digitized Ektachrome still:
{
"attestation": {
"CID": "bafkrei...hxfq",
"attribute": "time_created",
"value": "1989-12-22T06:14:00Z",
"timestamp": "2024-11-03T09:22:14Z",
"encrypted": false
},
"signature": {
"pubKey": <ed25519 public key bytes>,
"sig": <signature over the attestation>,
"msg": <CID of the signed content>
},
"timestamp": {
"ots": {
"proof": <OpenTimestamps proof bytes>,
"upgraded": true,
"msg": "Bitcoin block #868241 anchors this data"
}
}
}
To prove exactly when the files and their context were secured, the system uses OpenTimestamps. This protocol bundles the cryptographic hashes and anchors them to the Bitcoin blockchain, providing mathematical proof that the data existed at a specific point in time and has not been backdated. Finally, to ensure this verification data travels with the files beyond a dedicated visualizer, the pipeline injects Coalition for Content Provenance and Authenticity (C2PA) manifests directly into the media files. This embeds the cryptographic history into the file itself, allowing it to be verified by external platforms and tools like Adobe's Content Credentials viewer.
Contents
LearningsArchive
Learnings
-
UX is the Bridge to Trust: Cryptographic proofs are only as effective as they are legible. The success of the Panama Archive relied on the "Traffic Light" visualization, which translates complex hashes into intuitive trust signals for non-technical researchers and historians.
-
The Power of Relational Knowledge: Standard flat databases fail to capture the nuance of journalistic context. We found that representing "historical truth" requires graph-like knowledge structures to map the complex relationships between photos, telegrams, and witness testimonies.
-
Solving for Computational Scale: While the prototype successfully secured a curated selection, the next milestone is automation. Future work must focus on anchoring millions of legacy assets to the blockchain without compromising the manual oversight required for historical accuracy.
-
Standardizing Metadata: The project highlighted a critical need for flexible, interoperable metadata schemas. For an archive to be truly "future-proof," its technical structure must remain compatible with evolving web standards and emerging AI-detection tools.
Contents
LearningsArchive
Archive
- "Photo are disappearing, one archive at a time" opinion essay from Kira Pollack in the Washington Post
- Kira Pollack's profile by World Press Photo
- VII Foundation's interview with Kira Pollack and Chris Morris: "Expanding the Archive"