Timestamp Verification
2022
We utilize distributed ledgers to establish an immutable “proof of existence” for digital media and its metadata. By anchoring cryptographic fingerprints on public consensus networks, it creates a tamper-evident record of the absolute moment an asset was first observed.
This “birth certificate” for digital data shifts the verification model from reactive detection to affirmative proof, ensuring that the origin and integrity of critical information remain indisputable against the threats of revisionism and synthetic manipulation.
YEAR
2020-24
PARTNERS
Hedera
ProvenDB
OpenTimestamps
Numbers Protocol
Solana
LINKS
– Time for Trusted Timestamping
– Reuters collaboration, ProvenDB anchored on Hedera
– ‘Mom I See War’, a collection of drawings from Ukrainian children, anchored on the NEAR blockchain using the Numbers Protocol.
The Problem
Establishing the originality of a piece of content, and that a given piece of media is the first known version has been a conundrum since the invention of written communication. Whether one is looking to resolve disputes of which version comes first, or to prove media was created before the advent of certain AI technologies, a timestamp that can be verified with a trustworthy third-party can be a helpful solution. Verifiable timestamping can be used as a part of the digital media creation, preservation, and edit processes.
JOURNALISM
By anchoring field footage hashes on public ledgers, newsrooms can maintain an indisputable record of truth that survives both link rot and malicious denialism.
HISTORY
By registering high-fidelity fingerprints of historic records before the generative AI inflection point, institutions ensure that primary sources can be definitively distinguished from synthetic noise.
LAW
Third-party ledgers act as record holders from which to derive strong claims about integrity and point of origin of a digital item.
The Solution
Starling has used several Merkle tree-based technologies to efficiently create verifiable timestamps on public ledgers, and developed workflow using systems such as ProvenDB with Hedera Consensus Service anchors, OpenTimestamps proofs anchored on Bitcoin, as well as direct registration of media assets on many public blockchains. In all these cases, the block height is used to establish a verifiable timestamp for the registered digital media.
Adding an immutable proof of existence backed by distributed ledger consensus serves to establish a first known creation of digital media that is nearly impossible to refute.
READ FURTHER
Further to this work, we have created a reference implementation of timestamped databases in a project called ‘Authenticated Attributes’ that aims to integrate with digital media user interfaces and collaboration tools.
We have also created an offline, SMS-based silent registration prototype based on 5G technology, and integrating with the latest C2PA-capable cameras.
Four Corners Wordpress Plugin
2022
An embeddable display for photographs to show contextual and provenance information, such as photographer information, related images, and proof of existence on distributed ledgers.
YEAR
2022
PARTNERS
– Fred Ritchin
– The Four Corners Project
The Problem
Online platforms routinely strip metadata from images to protect user privacy – a necessary safeguard on the Web. However, this decontextualizes professional photojournalism, leaving viewers unable to verify a photo’s origin, time, or location. This creates a critical dilemma for photographers. They need a secure method to re-associate their work with this essential data, but require absolute control to do so.
They must be able to present this enriched, verifiable context only when they deem it safe, on platforms they trust – like their own website or a specific publication – to restore the full story behind the shot.
CASE STUDIES
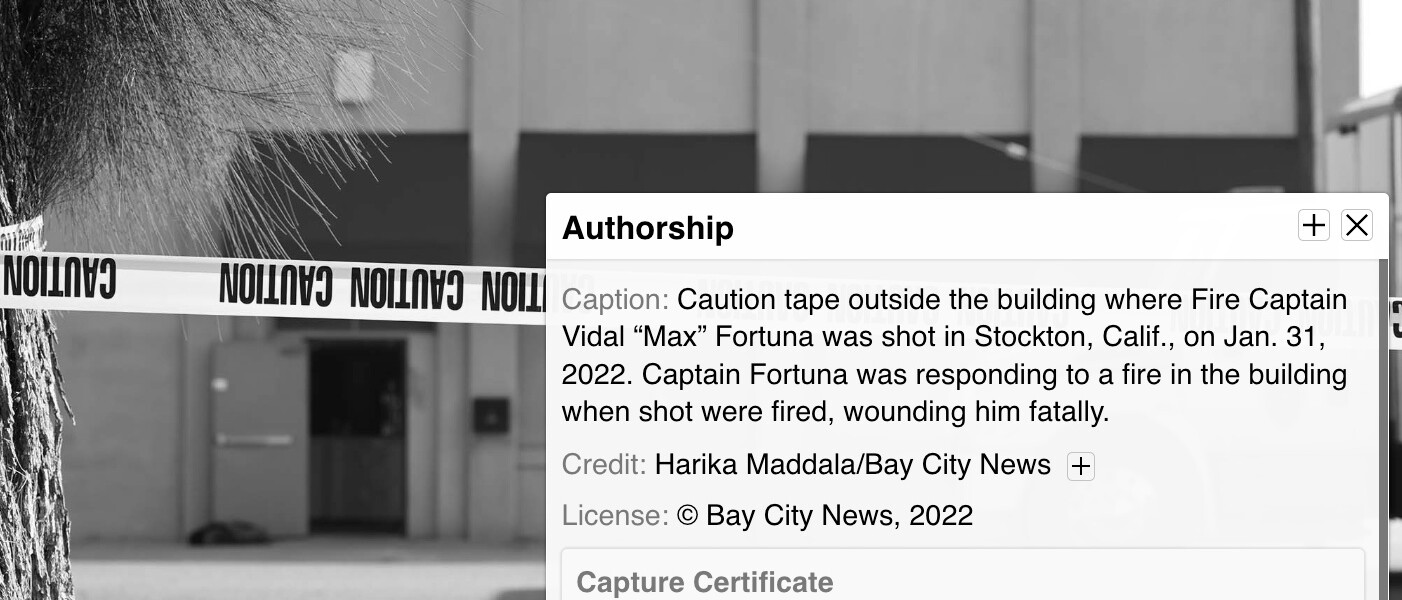
– Setting the Record Straight in Brazil’s Burning Wetlands (with Inside Climate News)
– Documenting Stockton’s Homelessness (with Bay City News)
The Solution
As often with Starling’s prototypes, the process begins at the moment of capture, where technical metadata like time and location are cryptographically signed, creating a tamper-evident record of rich, contextualizing metadata. This authenticated foundation still allows a photographer to later add richer contextual information – such as their byline, a narrative description, or related images.
Based on the Four Corners Project research and user interface, Starling Lab and Four Corners co-developed a WordPress plugin to bring this UI to the biggest blogging platform on the Web. This tool allows publishers to easily embed photos with an interactive layer, enabling viewers to explore the rich, attributable context and verify the circumstances of the photo’s origin.
As part of this work, Starling worked with the Four Corners team to develop a C2PA-compliant metadata schema for bundling rich contextual metadata in C2PA manifests. This schema contained all the metadata contained in each of the Four Corners toggles. This data is then included in a C2PA manifest, and parsed by the WordPress plugin, for presenting contextual and provenance information on each article.
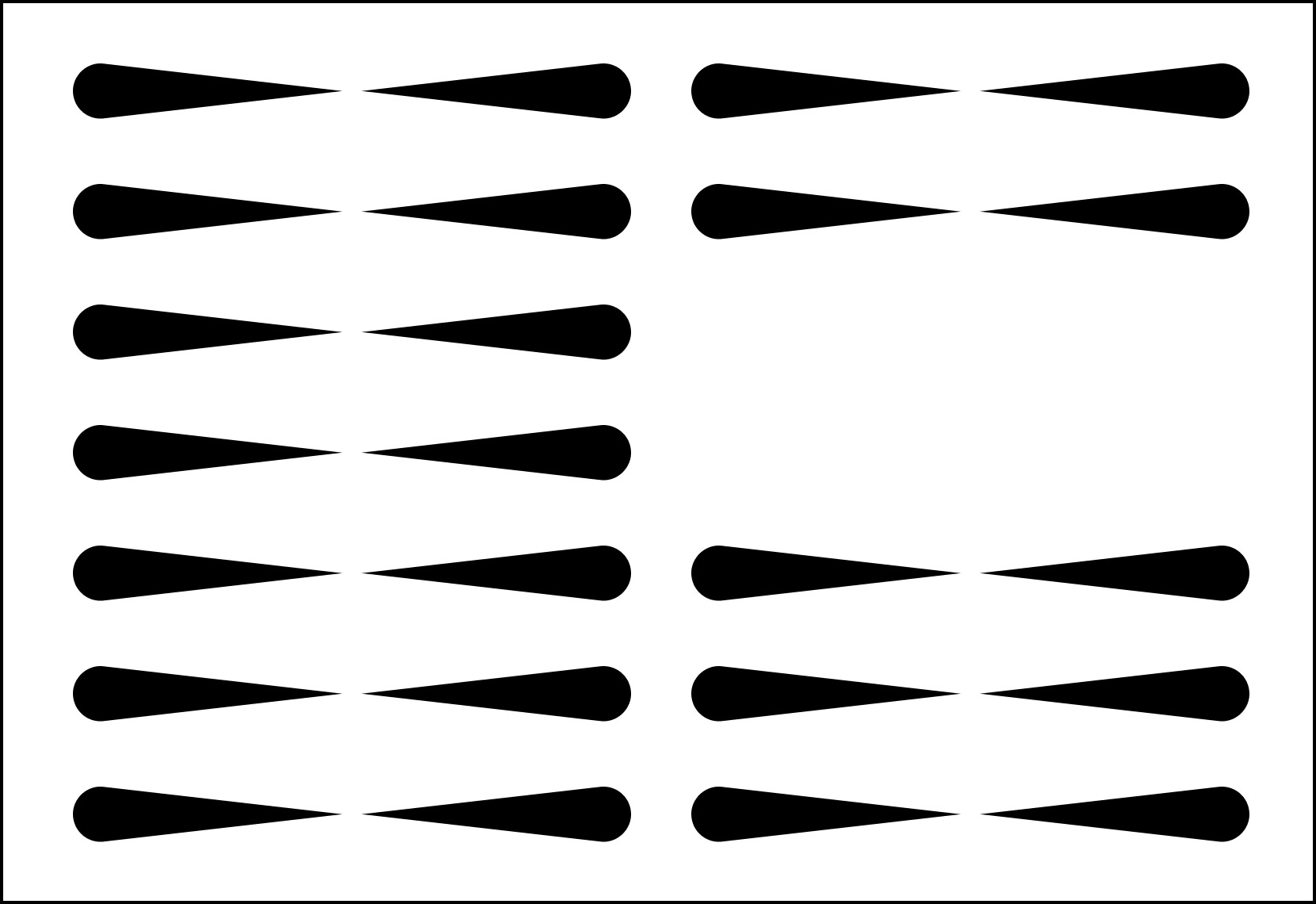
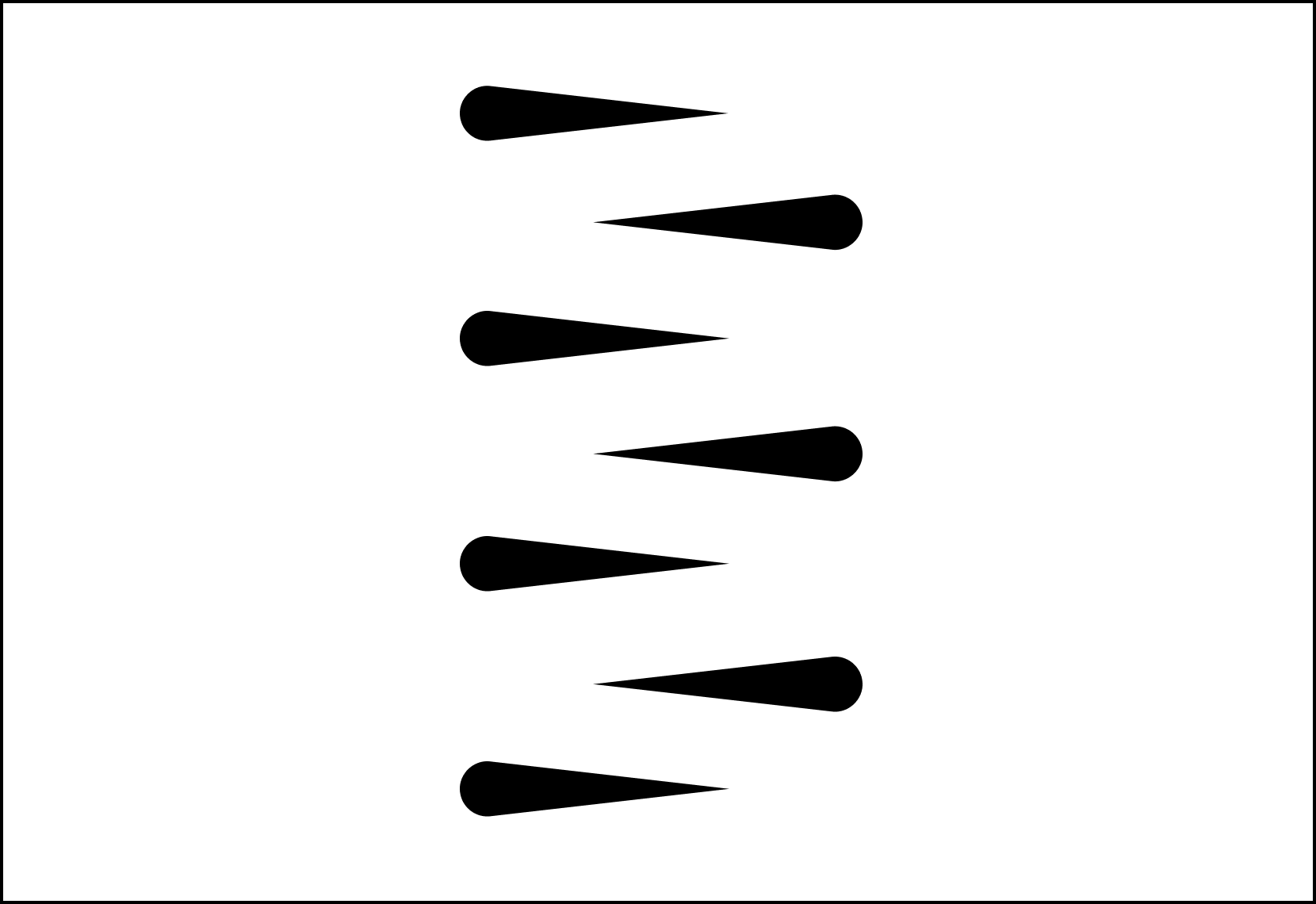
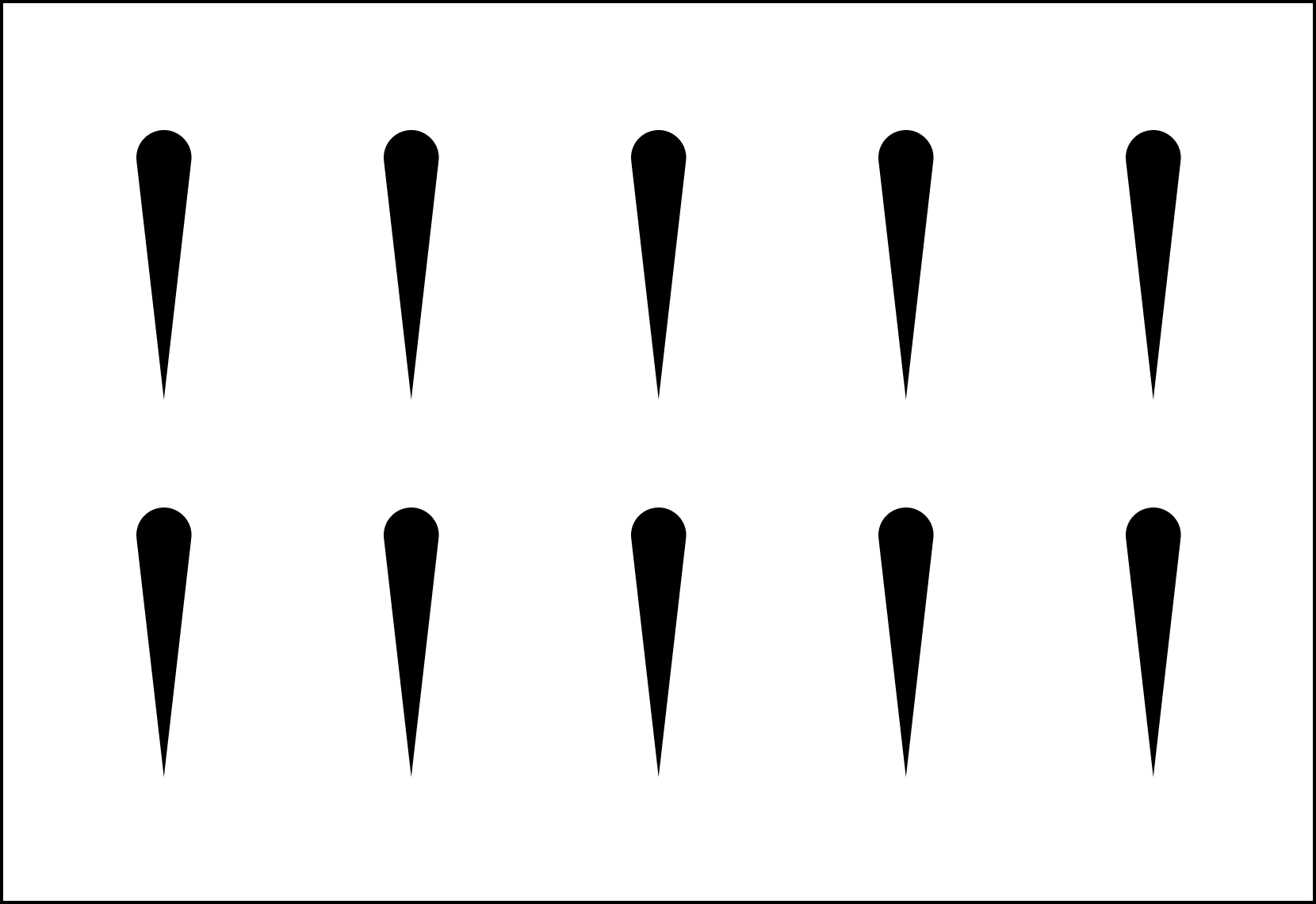
Overlaid on the photograph in each of the four corners are floating carets which, once clicked or hovered over, reveal additional data about the photograph.
Authenticated Change Tracking
2022
We integrate cryptographic provenance into the newsroom’s editorial lifecycle, ensuring that every modification – from photo edits to caption and metadata updates – is recorded in a verifiable, append-only log. By retrofitting existing Content Management Systems (CMS) with an authentication layer, newsrooms can provide an unalterable “audit trail” of their reporting process.
This shifts the trust model from static files to a dynamic, tamper-evident lineage, restoring transparency to the news-gathering and publishing workflow.
YEAR
2022-25
PARTNERS
Reuters
Hypha Coop
Fotoware
LINKS
– Case study: End-to-end authentication at Reuters from Canon cameras
– On displaying this metadata with Four Corners and Wordpress
The Problem
Modern newsroom Content Management Systems (CMS) are designed for efficiency, and can be improved to provide more evidentiary rigor. While they track changes internally, these records are stored in private, centralized databases that are vulnerable to tampering and opaque to the public. As stories evolve from raw field captures to published articles, critical metadata (like original capture time or source identity) is often lost or stripped during the editing process.
This creates a “black box” that prevents audiences from verifying the reporting’s journey and leaves journalists unable to defend their work against claims of post-capture manipulation.
The Solution
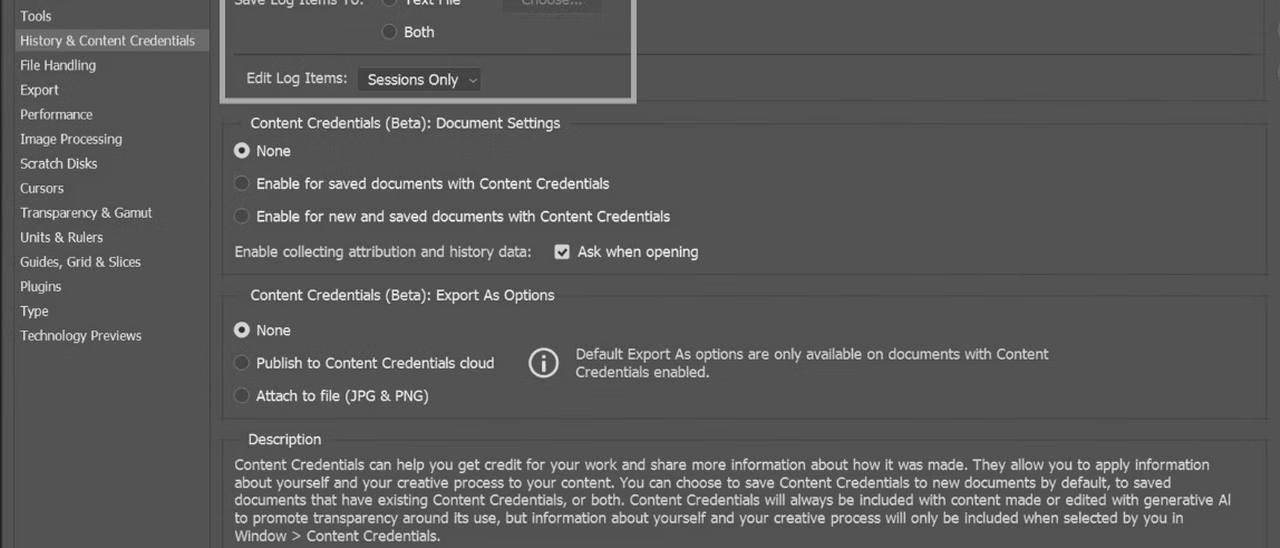
Starling is working to understand the existing tools that newsrooms use to ingest information and to write and edit their stories, and we are working to integrate the ability to better track and authenticate changelogs of images, text, and other documents. Our goal is to improve the ability of newsrooms to work on authenticated information, and add authentication to changes they make, within their existing content management systems.
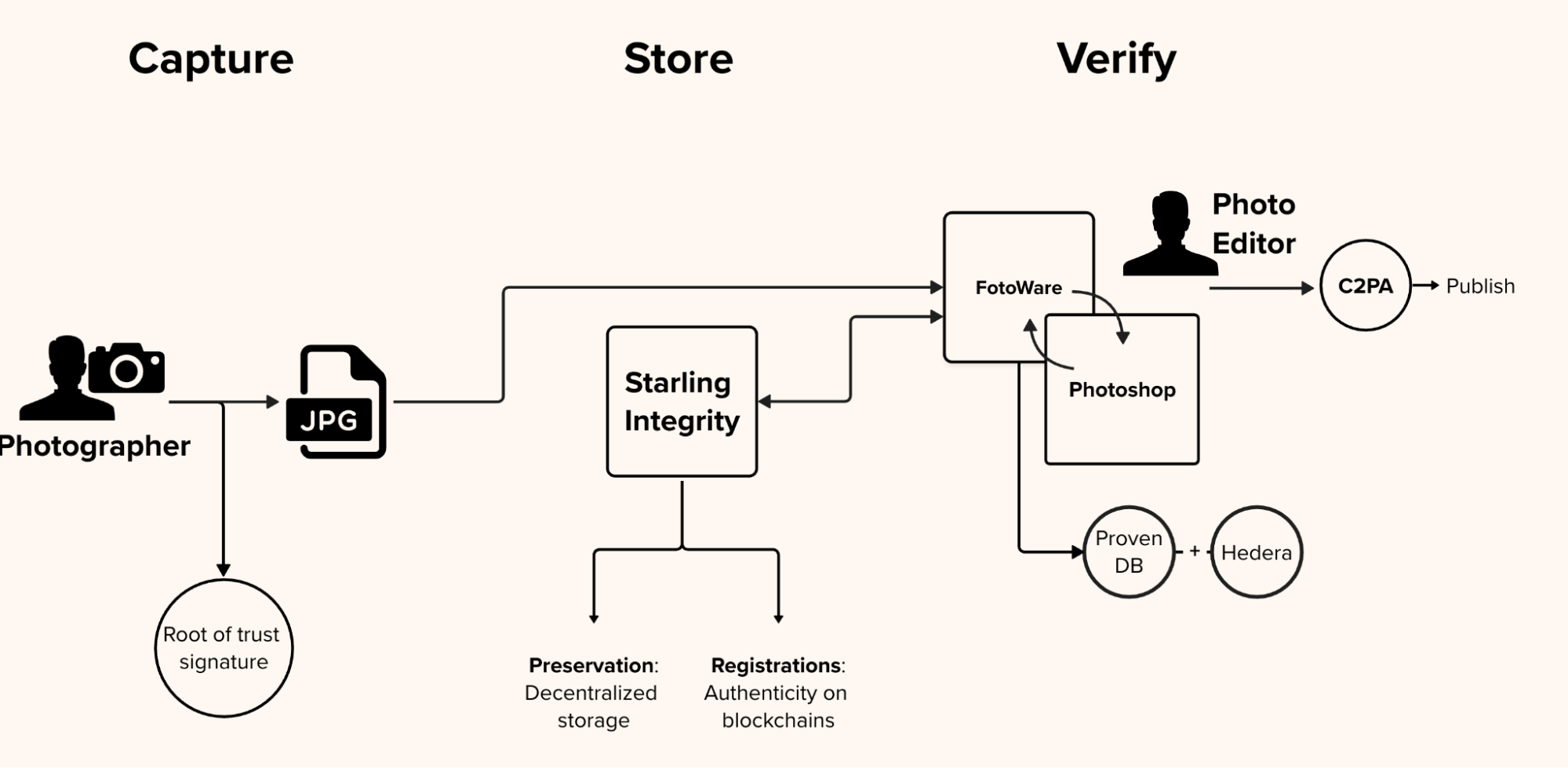
In the diagram above, CMS and Photoshop work in tandem so that the photographs’ edit history in Photoshop be reflected inside the CMS. In our milestone collaboration with Canon Camera and Reuters News, we designed a system that creates an immutable audit trail that works invisibly alongside standard newsroom tools. As the image is transmitted to the publisher’s asset management system and undergoes permissible edits by photo editors—such as cropping, color correction, or captioning—an automated background process tracks the file. Every single modification is recorded in a private, verifiable database that is anchored to a public distributed ledger, creating a mathematically provable edit log.
We are also prototyping how this information can be displayed to audiences, and looking for a greater understanding of what these metadata markers might mean to readers and the trust they place in stories and media. This final step focuses on empowering the end consumer: the reader. The prototype packages the initial hardware signature, the original metadata, and the complete, cryptographically secure edit history into a standardized, open-source manifest. This manifest is embedded directly into the final published image, allowing anyone—from researchers to everyday readers—to inspect the file and independently verify its authentic journey from the frontlines to their screen.
Document Redaction
2022
Establishing a cryptographic seal of transparency for sensitive digital records, moving beyond traditional “black-box” redaction.
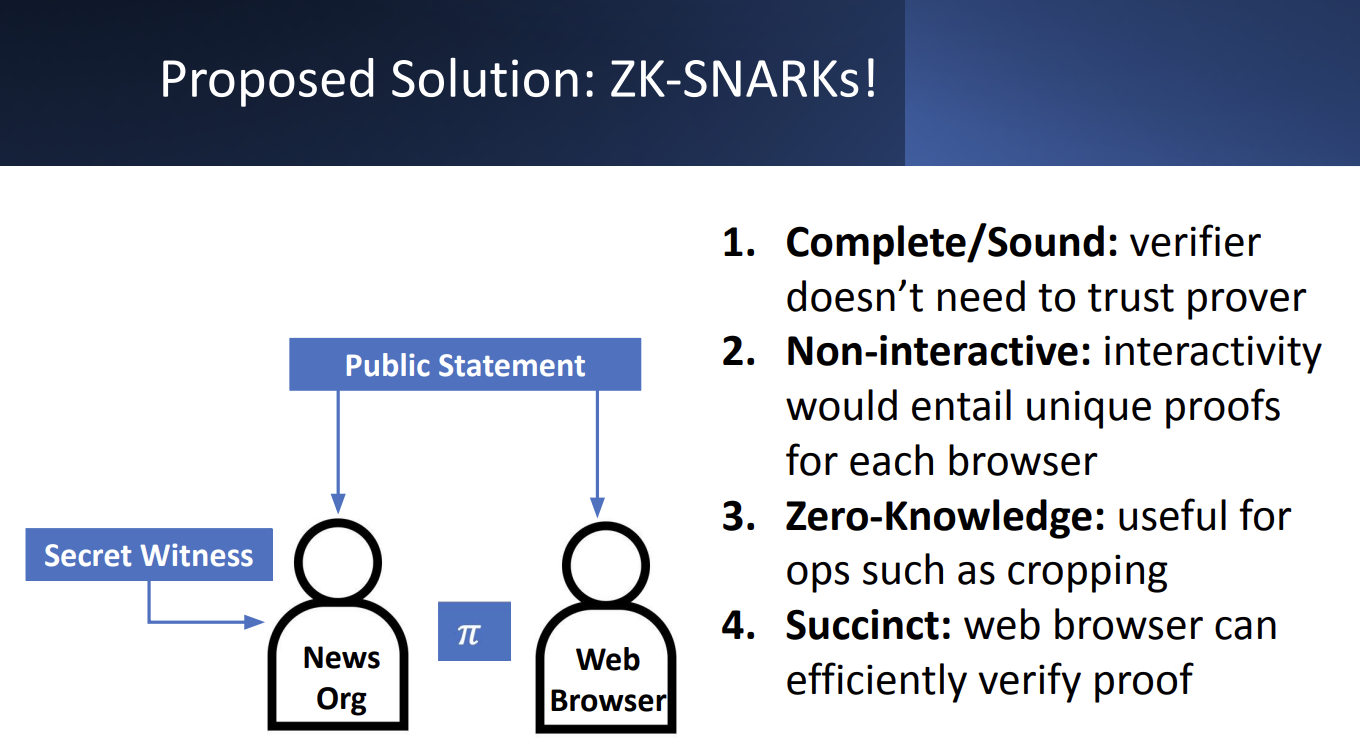
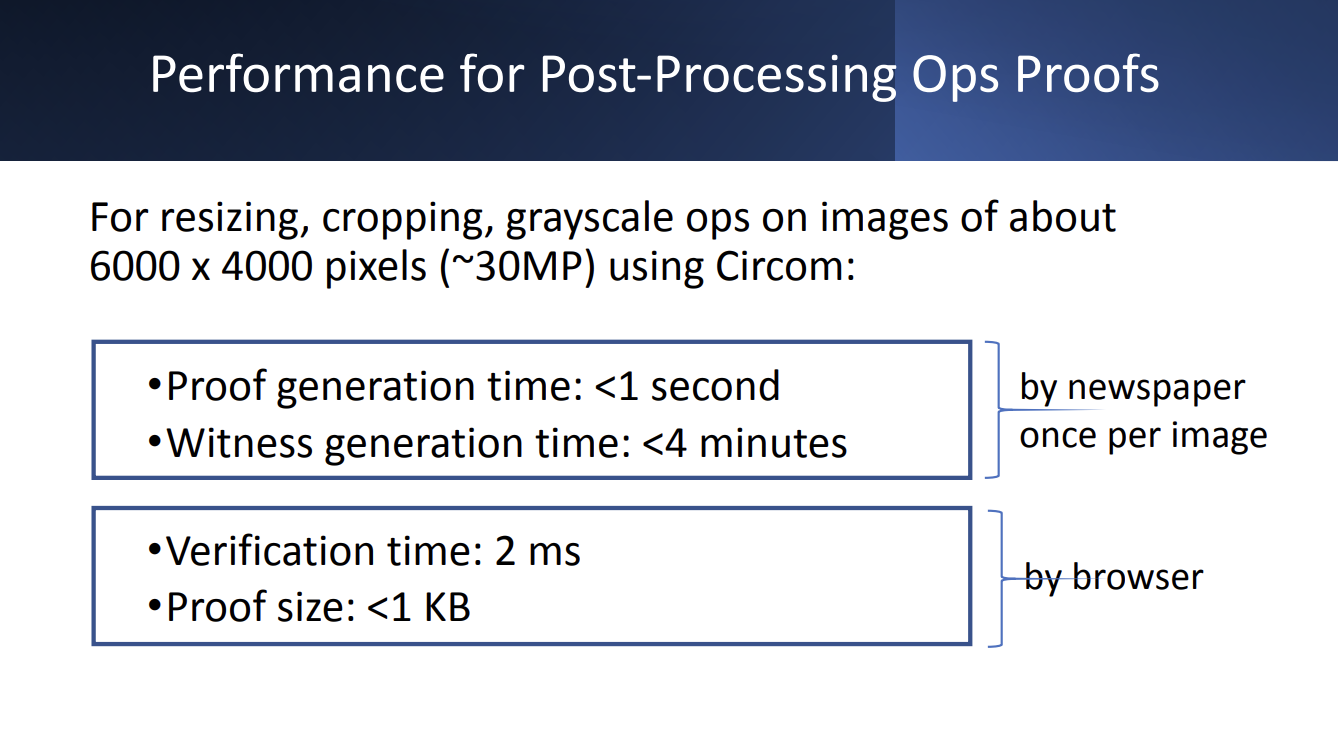
Zero-Knowledge Proofs (ZKP) allow investigators to obscure personally identifiable information (PII) while providing a mathematical guarantee that no other part of the document has been altered.
This concept shifts the trust model from requiring blind faith in a publisher’s edits to providing affirmative proof of a document’s integrity, ensuring that critical primary sources remain both ethically protected and legally robust
YEAR
2022
PARTNERS
Stanford Applied Cryptography Group
LINKS
– Case Study: The DJ and the War Crimes
– Presentation from Trisha Datta and Dan Boneh
The Problem
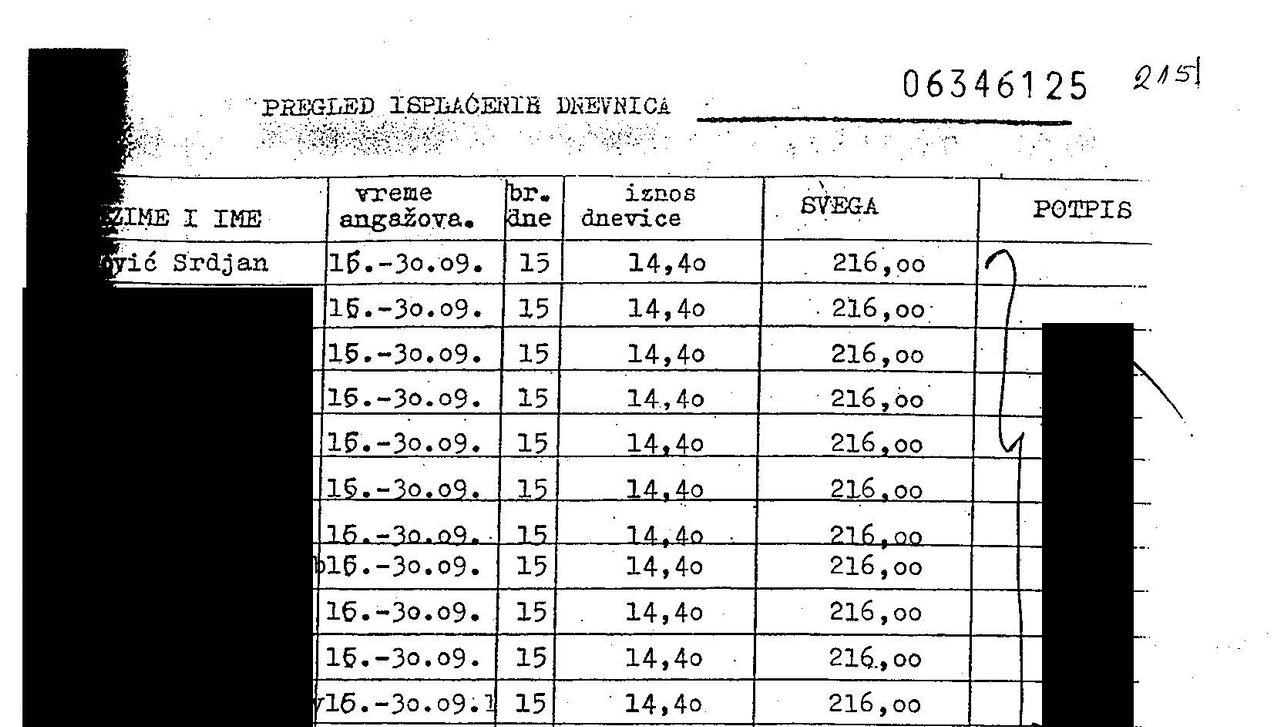
Accountability investigations often rely on digitized primary sources – such as the UN payroll records unearthed in our Bosnia war crimes probe – that contain sensitive PII of individuals not central to the investigation. While redacting this information is a journalistic and ethical necessity, it creates a “trust gap”. In an era of widespread denialism and “cheapfakes,” any manual modification to a source document can be weaponized by bad actors to claim the entire record is a forgery, undermining the evidentiary weight of critical testimonies.
The Solution
In partnership with our principal investigator’s Professor Dan Boneh’s students from the Stanford Applied Cryptography Group, Starling developed a workflow that integrates forensic ingestion with cryptographic proof systems, and managed redactions.
It relies on a Zero-Knowledge Proof that certifies the relationship between the original and the redacted file. This technology generates a mathematical proof that the only changes made to the published PDF were the addition of black boxes over specific pixels. This allows third parties, such as expert witnesses, to “check the math” and verify that no text was altered or deleted, maintaining the document’s integrity while fulfilling privacy obligations
JOURNALISM
Verifiable Redaction allows newsrooms to protect the privacy of vulnerable bystanders without sacrificing the credibility of their reporting. By providing a cryptographic guarantee that only specific PII was obscured, journalists can defend their primary sources against bad-faith accusations of manipulation.
HISTORY
This technology safeguards the sanctity of historical records by ensuring that “anonymized” archives remain verifiable links to the past.
LAW
Verifiable Redaction establishes a court-admissible chain of custody for documents containing sensitive material. ZKPs benefit can facilitate the verification of proprietary forensic software, complex discovery datasets, and sensitive testimonial claims without compromising the underlying trade secrets or personal privacy that often create insurmountable disclosure dilemmas.
ProofMode Authentication
2022
Experimenting with the integration of lightweight, forensic-grade verification into secure messaging workflows.
YEAR
2022-23
PARTNERS
Guardian Project
Hala Systems
Signal Messenger
LINKS
– Case Study: The Proof’s in your Pocket
– From the Guardian Project team: Integrating libProofMode
The Problem
Citizen-captured photos and videos are becoming powerful reporting tools. But faked footage, or footage with missing crucial context, threatens to break the trust between a newsroom and its audience. Professional journalists thus need to be able to vet the footage captured by citizens to ensure that the files sent in by citizen journalists are authentic and accurate representations of the depicted event.
The Solution
ProofMode (developed by the Guardian Project) promotes trust by providing a means to strongly authenticate multimedia at the point of capture.
We were the first to experiment with its distribution as a software library, under the name libProofMode. Starling Lab developed a bespoke fork of Signal Messenger that embeds authentication as a native feature. Users of this custom app can snap photographs directly within the app, which automatically generates a unique OpenPGP key pair to sign the media and its surrounding sensor metadata, including location, time, and cell tower environment.
At capture, media hashes are automatically registered on OpenTimestamps to create a “proof of existence” on the Bitcoin ledger. To ensure secure transport, every file sent via Signal triggers an automated MobileCoin micro-transaction; the first 16 digits of the “proof hash” are embedded in the transaction memo, allowing the recipient to cryptographically verify that the file received exactly matches the file captured in the field.
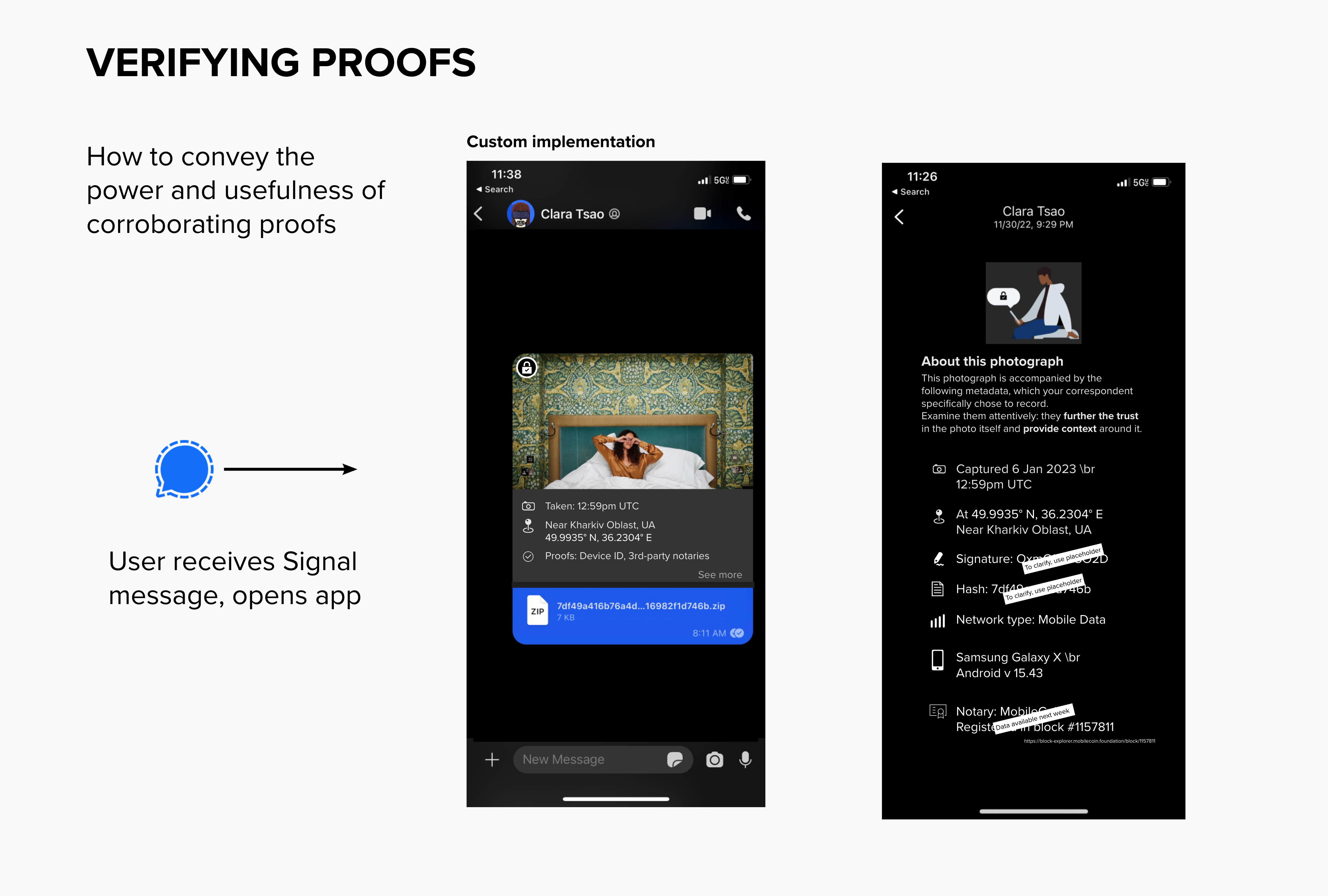
To reduce the burden on legal and journalistic investigators, the prototype features a visual layer of UI inside the Signal conversation view. Both sender and recipient can instantly surface contextual metadata snapshots and check them against immutable third-party record holders, such as the LikeCoin or Avalanche blockchains. This “glass-to-glass” approach ensures that technical authenticity markers are accessible and legible to the field practitioners who need them most.
HIGHLIGHT
In response to the shelling of Kharkiv’s schools, Starling Lab launched Project Dokaz (“Proof”). Local photographers were equipped with the custom Signal app to conduct “preventative documentation” in support of the Safe Schools Declaration. By capturing regular rounds of authenticated imagery, the team was able to verify the absence of military co-option at these sites, confirming their protected status under international law.
Read mode about Project Dokaz →
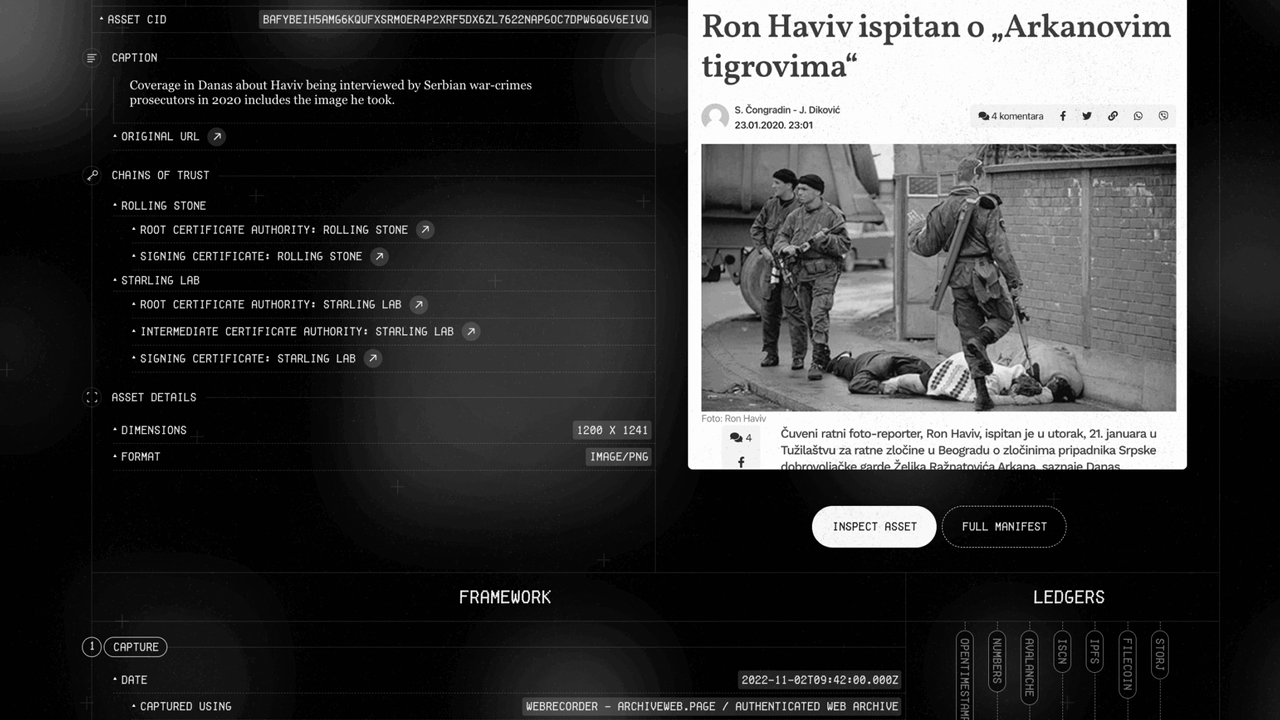
Authenticated Web Archives
2022
Accurate, reliable, simple to use, and secure workflows for archiving web content.
The Problem
Online content disappears rapidly, erasing critical evidence for investigative journalism, accountability, and cultural preservation. Social media platforms and hosting providers face pressure to implement stricter content moderation, with automated filters and human moderators making rapid decisions about what stays online. Records documenting potential crimes – especially those with violent imagery – risk being permanently deleted. Restoring content is often impossible: original posters may be arrested, lose device access, or no longer be alive when investigations begin.
Existing archiving methods face three challenges: platforms actively block automated crawlers, preserved content lacks the cryptographic verification and chain-of-custody documentation required for legal admissibility, and saved material becomes unsearchable across large collections.
JOURNALISM
Strong web archives provide a tamper-evident way to capture online evidence, safeguarding reporting against censorship and the erosion of digital sources.
HISTORY
These archives create a trustworthy and resilient collection of digital primary sources, ensuring that the ephemeral nature of the web does not erase our collective memory.
LAW
This technology establishes an unbreakable digital chain of custody, transforming fleeting web content into verifiable, court-admissible evidence.
The Solution
Starling is developing workflows using open source software for archiving web content to ensure the preserved archives are accurate and reliable, taking into consideration the sensitivity of the data. We draw from the considerable expertise deployed by national libraries and legal deposits from around the world.
Our case studies have experimented with forensically-sound web archiving, focusing on capturing broad contextual snapshots of web material.
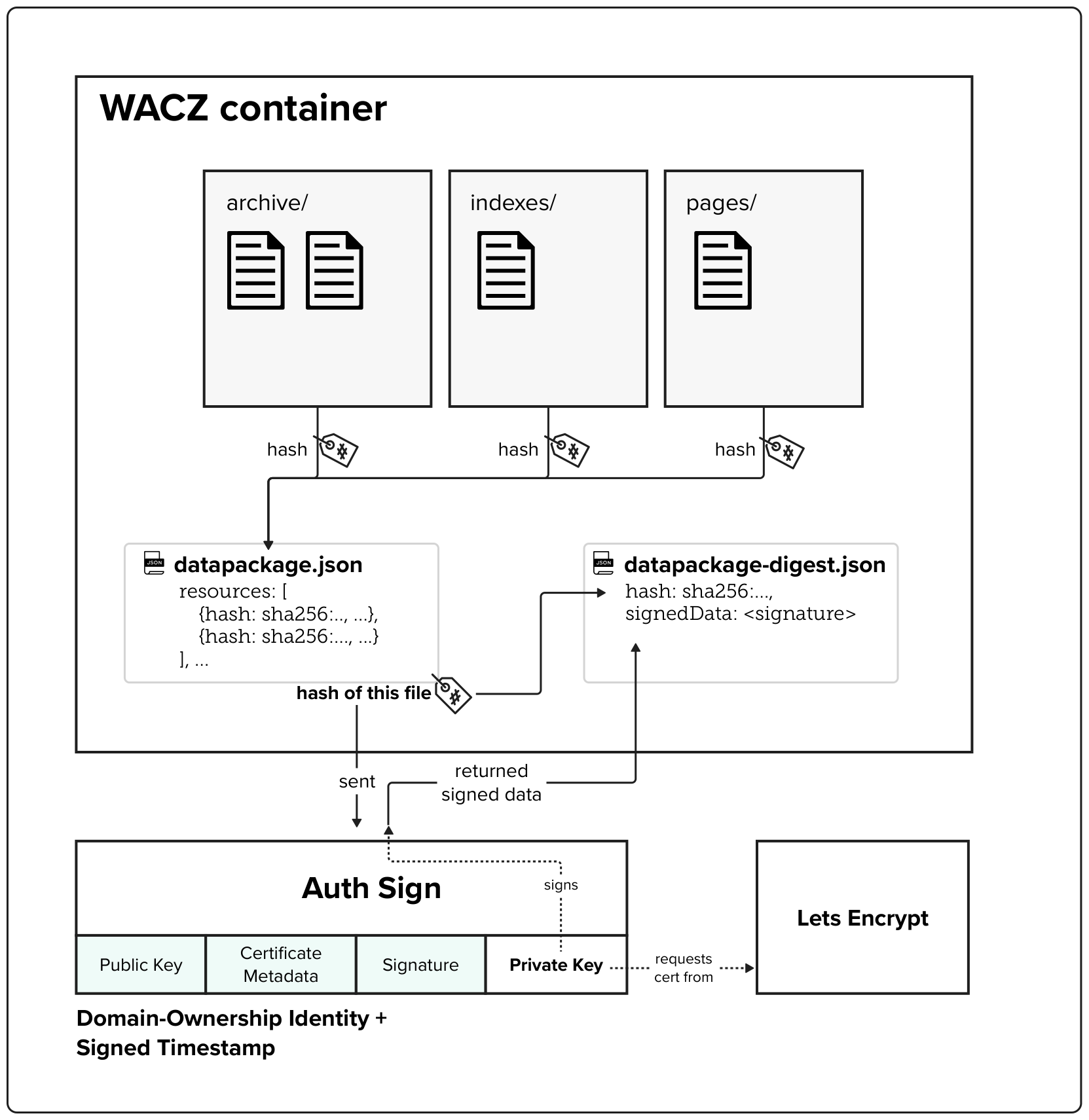
The WACZ standard and file format
The Web Archive Collection Zipped (WACZ) standard provides a portable packaging format for web archives that bundles WARC data, indexes, metadata, and verification information into a single ZIP file. Unlike traditional WARC files that lack contextual information and require complex server infrastructure for viewing, WACZ enables efficient browser-based rendering by organizing content with indexes that allow random access to only the data needed for each page.
Built-in Integrity Through Cryptographic Hashing
Every WACZ file includes a datapackage.json manifest that contains cryptographic hashes of all resources within the archive, providing a verifiable fingerprint to detect any unauthorized modifications. This hash-based integrity checking ensures that archived content remains tamper-evident throughout its lifecycle.
Authentication Through Digital Signatures
The specification adds optional authentication capabilities by allowing creators to digitally sign archives – notably using TLS certificates. These signatures validate both the identity of the entity creating the archive (using X.509 SSL certificates) and establish a trusted timestamp for when the capture occurred.