Documenting Stockton’s Homeless

Documenting Stockton’s Homeless
Bay City News and Starling Lab pioneer cryptographic tools to authenticate images and expose the truth of homelessness in California.
Reading Time: 5min
Contents
Background
The homelessness crisis in California has escalated dramatically in recent years. Point-in-time counts from 2022 show a nearly 6% rise from 2020, and a 17% increase in homeless but sheltered populations. Against this backdrop, the Bay City News (BCN) series Documenting Stockton’s Homeless was reported over six months, telling diverse stories from the plight of an individual on the street to data analysis quantifying the issue’s growth. It looked into rising living costs, economic disparities, and inadequate mental health and addiction services – all factors in the statewide problem. The series also addressed concerns faced by local business owners, government expenditures, and the availability and challenges of providing housing.
San Francisco’s homelessness issues have been widely reported, but now are expanding to nearby communities like Stockton in San Joaquin County. With a population of over 320,000 as of 2020, it is the County’s largest city. The scenes on the ground there tell the story of an growing problem despite significant resources invested to address it.
Crucially, the issue of misinformation has made its way in the public debate about homelessness. Local authorities often provided optimistic assessments that did not match the reality observed, leading to public distrust. This project highlighted these discrepancies. Together with Starling, BCN captured and presented the story of Stockton using advanced photo authentication tools to ensure accuracy.

In May of 2023, before Generative AI became a household term, Fred Ritchin, Dean Emeritus at the International Center of Photography and founder of the Four Corners Project, wrote about the urgent need for photojournalism to provide audiences with more data about their images. This includes context, explanation of ethics, eyewitness statements, and other background. He cautioned, “There is enormous panic in the photojournalistic industry due to the emergence of photorealistic synthetic imagery generated by AI that confuses the public as to what is going on and makes their actual photographs increasingly irrelevant.”
Bay City News also had their eyes on the future, anticipating issues when photojournalism is called into question when covering contentious or high-stakes issues. “It is imperative that local publications like Bay City News reassure readers that facts are verified and images are real,” emphasized BCN Photo Editor Ray Saint Germain.
Contents
Context
This collaborative case study was a pioneering experiment for Bay City News and The Starling Lab for Data Integrity on a number of levels. Together, the organizations set out to cover the homelessness crisis in Stockton as it surged in 2022 and 2023, with meticulous documentation to reveal local funding disparities and the gap between reality and official statements.
Bay City News is a local San Francisco and Bay Area news agency that covers the region’s businesses, residents and government agencies. They publish a free, online newspaper called Local News Matters.
Under the direction of Ray Saint Germain, BCN photojournalists Harika Maddala and Victoria Franco, worked for six months in collaboration with Starling to develop and present cutting-edge authentication tools for photojournalism. Starling – which uses innovative approaches to integrate journalists, legal experts, and archivists into the decentralized web – helped the team enhance accuracy and combat misinformation and disinformation, reinforcing the critical role of trustworthy local news.
For this project, camera technologies were prototyped to capture and secure photo and contextual information at the point of capture. It was also the first large-scale, real-world deployment of Fred Ritchin’s brainchild—the Four Corners visual display of photographs alongside contextual information, which through this collaboration was further enhanced with C2PA technologies. Furthermore, with the newswire service, we explored the use of non-fungible tokens (NFTs) to publicly track the custody of digital photographs on a public ledger.
United with a vision to capture accurate representations of what the photographer witnessed, Starling Lab, BCN, and Four Corners began a collaboration that would create authenticated “time capsules” of images and contextual metadata, secured and presented as published articles available on LocalNewsMatter.org to document the Bay Area’s homelessness crisis and tracking data from relevant government agencies. These articles feature 35 authenticated photos, with six displayed using Four Corners. This first-of-its-kind initiative put together several in-development technologies and emerging standards over the long-running implementation, in hopes to show the art of the possible for authenticity in photojournalism in a world of manufactured images.
The sum of these technologies, along with the articles published on LocalNewsMatter.org, offer learnings for all stakeholders as we look forward to the future of trustworthy local news.

In addition to the BCN team and Starling Lab, collaborators on the project included Four Corners founder Fred Ritchin; Corey Tegeler, Engineering Lead at the Four Corners Project; and Newspack Automattic Manager Daniel Brown. BCN’s content management system is based on WordPress and supported by Newspack.
Contents
Framework
The Challenge
Bay City News is a for-profit news agency that serves other media organizations in the Bay Area. It sustains a nonprofit Foundation, which runs LocalNewsMatters.org–and provides free local news for readers. BCN strives to reassure readers that their facts are verified and images real. “Being able to prove the origin and authenticity of photos could be useful to professional newsrooms like ours,” said BCN Photo Editor Ray Saint Germain.
Ordinarily, BCN’s workflow kicks off with a photo assignment, where staff photojournalists shoot with DSLRs and mirrorless cameras. Most reporters use phones, and few of them use DSLR cameras. Breaking news happens fast, and photos need to be delivered to newsrooms quickly. Photos shot with a cell phone are directly sent to the photo editor, whereas photos shot from cameras are transferred to a laptop, then sent in. Non-daily assignments are filed by the end of shifts.
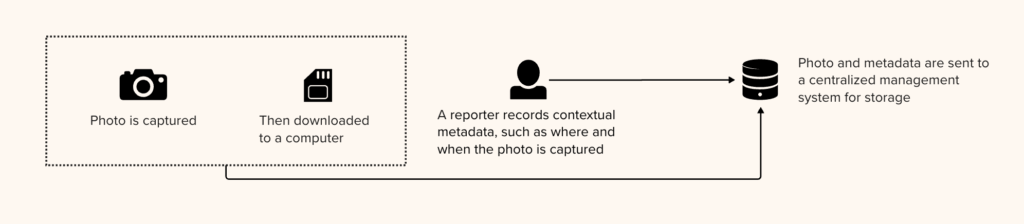
Contextual information recorded by the photographer is later associated with each captured photo, and included in the image file for storage and distribution. For example, on older cameras, the date and time are input manually and may be configured incorrectly at the time of capture (ex: due to Daylight Savings Time), so the correct times are put in afterwards. Captions are similarly added afterwards.
Once these files are published, their image pixels and embedded contextual information are vulnerable to manipulation. For example, anyone can simply update the timestamp and location recorded in image metadata and redistribute the file. A reputable outlet may even publish the altered photo, completely unaware that it contains tampered metadata, and the unsuspecting reader would receive incorrect contextual information about this photo. Even worse, the image may contain authorship information still showing the name of the BCN photographer, wrongly attributing the disinformation to BCN.
As a newswire service, BCN regularly uploads each photo three times: to a BCN server, WordPress server, and SmugMug. Any changes to captions have to be done on all three servers, adding to the risk of manual mistake. Without an audit log system, it may be hard to resolve disputes where two photos with conflicting metadata arise.
Lastly, the contextual metadata embedded in an image is very limited. And there is usually no available interface to showcase this limited set of contextual information to the readers, especially not in a way that adds value. It would be highly valuable if there are ways to embed rich contextual information, such as links to related photographs and the profile of the photojournalist, so the reader can get a richer experience with these same images.
Our hypothesis is that adding contextual information gives more value to the photo. However, the more information we add, the more there is to manipulate. What is the purpose of embedding a usage license if it can simply be edited by anyone without permission? Therefore, we must also secure all metadata alongside the image pixels. Starling’s approach is to do this via cryptographic methods.
Contents
The Prototype
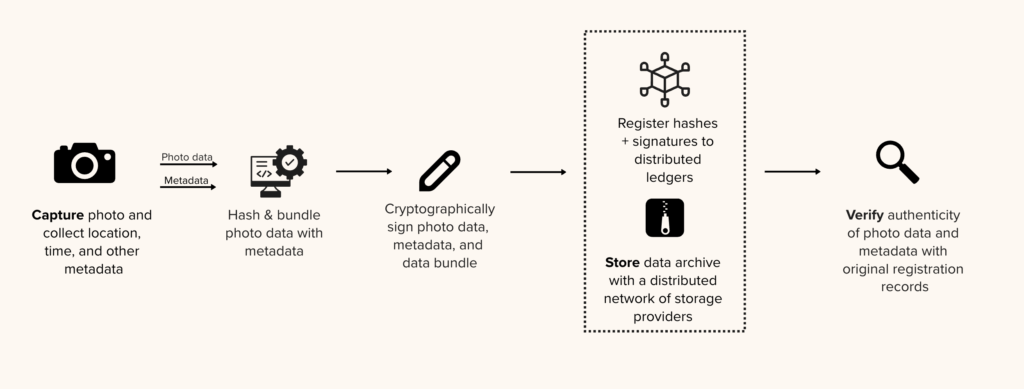
The team was eager to road-test new cryptographic tools that implement Starling’s three-part framework of Capture, Store, Verify.
Starling developed an altered workflow that allowed automated metadata capture and an audit trail of photo edits, but still fit with a standard photo assignment.
Aiming to minimize disruption for photojournalists, the BCN team was equipped with a Canon R5 camera tethered through Wi-Fi to an HTC smartphone loaded with specialized software.
Most importantly, the team focused on how to secure and surface rich contextual metadata for each photo to the reader at the point of publication. They partnered with the Four Corners Project to present these time capsules in such a fashion that readers could visually examine contextual information alongside photographs. This innovative graphical display allows readers to examine a photo’s backstory and metadata – including timestamps, GPS positions, and other provenance markers. This means readers can explore and verify the authenticity of images independently.
At a high level, these steps included:
- Capture: Using the Canon R5 camera and HTC Exodus 1S phone, photos and metadata were sent to a Starling-managed server, and were immediately secured through hashing and signing. The authenticity records were registered on blockchains, sealing their proof of existence such that future alterations on pixel of metadata would be evident.
- Store: Images were stored on several BCN and partner systems, both for preservation and distribution. This was least disruptive to BCN’s workflow and copyright policies. The authenticity of the files stored can be verified against blockchain registration records for data integrity (i.e. they were untampered originals).
- Verify: C2PA attestations were made throughout the photo edit chain. In particular, a C2PA schema was developed for Four Corners’ rich contextual metadata, and a WordPress plugin was developed and deployed on the Newspack-operated content management system so the metadata can be surfaced to readers. This allowed the team to test the hypothesis of providing rich metadata to readers through a polished user interface.
A total of 15 stories were published through the course of the Starling Lab project and are all presented on a LocalNewsMatter.org project page with 35 authenticated photos and six authenticated photos displayed using Four Corners.
Contents
Technology
Capture
The Capture Setup
In a standard photo assignment, DSLR-captured photos would be downloaded to a laptop and sent directly to photo editors. However, this does not allow for an opportunity to automatically capture GPS location (as most cameras do not have a GPS module) and other at-source metadata. On the authenticity front, neither the camera or the delivery endpoints use cryptographic techniques to secure the image and metadata. Therefore, we modified the standard workflow to add an HTC Exodus 1S mobile phone, which was loaded with an application called Starling Capture and pre-authorized to send image files – with their metadata – to a Starling-operated server.
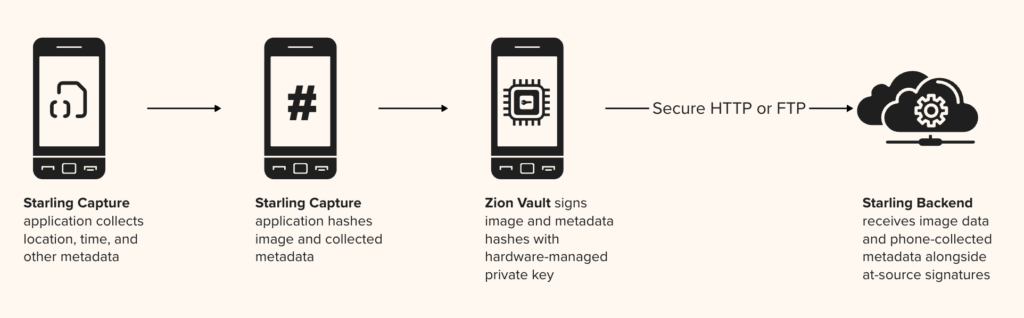
BCN Photojournalist Harika Maddala and Reporter Victoria Franco used a Canon EOS R5 camera. The Starling Capture mobile application, developed by Numbers Protocol, uses Canon’s Canon Capture API (CCAPI) to set up a Wi-Fi hotspot for the phone to connect with the camera. With each snap of a photo, the image file is automatically transmitted to the application, where GPS, time, and other metadata are gathered and associated with the photograph. An example of gathered metadata is available on GitHub.

Digital Signage on Device
Upon receiving an image, a cryptographic hash was immediately computed from the image file, serving as a secure and tamper-evident fingerprint to identify the file. Then signing keys pre-configured by Starling on that device were used to sign both the file hash and the metadata, sealing the data “at source” before any data was transmitted to a server.
This important step of digital signage secures all of the above, and protects against unnoticed tampering even during transmission. It is unfortunately not a capability that professional cameras had at the time of this project. However, in parallel, Starling has been working with camera vendors to add such capabilities, and recently vendors (including Leica, Sony, and Canon) started releasing digital signage features to a handful of models.
Uploading for Registration
After each photography session, the BCN team used a photo gallery within Starling Capture to inspect previews and select images to upload. Uploading to Starling servers requires an access token pre-configured on the phone. This gave assurance to Starling that the upload request was originating from a known source, and specifically that it came from the device provisioned to the BCN team. This also allows authorship information to be associated.
Once the server received an image, it was registered onto blockchains alongside contextual metadata and at-source signature information. These blockchains include Avalanche (a fast, decentralized, open-source blockchain that offers smart contract functionality) and LikeCoin (a chain specialized for decentralized publishing). These public ledgers use cryptography to ensure registration records are tamper evident and immutable. In the Verify section, we will explore how the registration information is presented to readers, so they can independently audit each photo against its registration records.
Store
Starling generally advocates storing data in multiple places to protect against various threats of data loss, and oftentimes employs decentralized storage systems as a preservation strategy. This comports with an industry standard 3-2-1 backup strategy, which encourages three copies in at least two different formats and one offsite location.
For this project, due to copyright concerns, the storage of this media and data remained on systems managed by BCN and Newspack, but the existing workflow at BCN already has file replication across a BCN server, a WordPress server, and SmugMug.
After Starling’s server received each photo for registration, we aimed to return authenticated versions of the photos to BCN as soon as possible to be minimally disruptive to their workflow. This was done via synchronization to a Dropbox folder with shared access. In this process, the server took the image pixels and metadata, then generated a C2PA manifest (signed by Starling), then bundled it with the image file according to the Content Authenticity Initiative’s specification, and finally returned it to BCN’s photo editors.
Verify
Upon receiving C2PA-authenticated images from the Starling server, the photo editorial process began.
Unlike traditional image files, these already contained metadata such as time, location, and author information that were automatically associated by the tethered phones and validated on the Starling server. From this point onward, Starling worked with BCN through the editorial process to track incremental edits and changes, so the published photo would retain an audit trail to the original photo. This can be referred to as glass-to-glass authentication, meaning from the moment light hits the lens of a camera to the moment it comes out of the audience’s device screen.
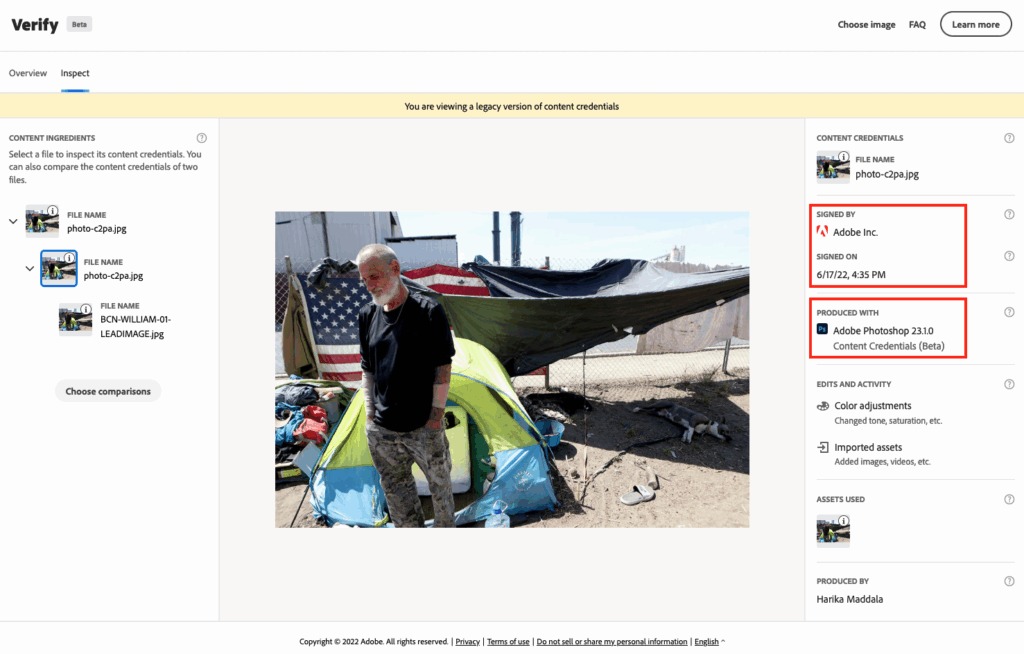
Image Edits with Adobe Photoshop Content Credentials
In order to resize photos, or to make other pixel or metadata changes, the BCN team used a beta feature in Adobe Photoshop called Content Credentials, which is an implementation of the C2PA Specifications. When the edited image is exported, a second C2PA manifest containing tracked changes is signed by Adobe Inc. attesting to that fact Photoshop was used to perform the changes listed under Edits and Activity in the Content Credentials Verifier.
Rich Contextual Metadata with Four Corners and C2PA
In addition to securing provenance information and establishing an audit trail through the photo editing process, the team also set out to prototype a better way to display rich contextual metadata to readers. The hypothesis was that by bundling more context with each photograph, we could provide a more valuable experience and accurate conceptual picture for readers.
The team elected to use the Four Corners interface, which allows specific information to be toggled upon an interaction in each of a photograph’s corners. With the Four Corners team, we created a WordPress plugin which augments the standard Four Corners with additional features:
- The ability to read and display contextual metadata from C2PA manifests bundled with an image file
- A Capture Certificate displaying authenticity information at the bottom right corner
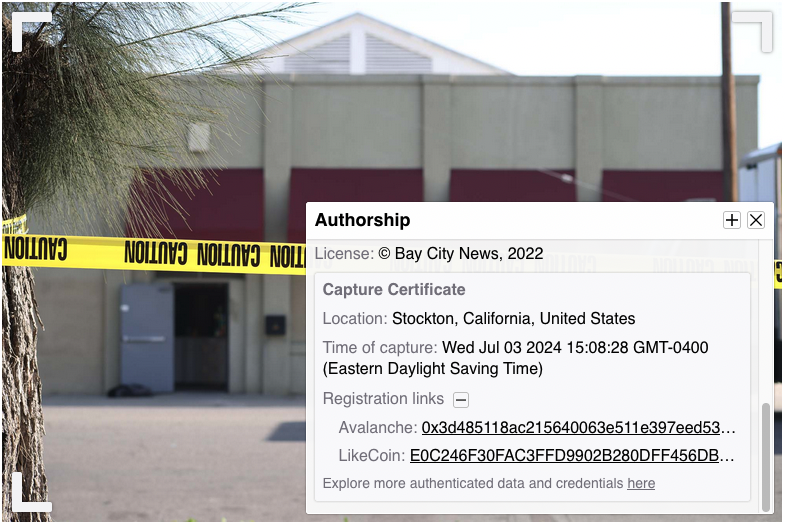
This added contextualization highlights the authorship by the photographer, the credibility of the image, and prevents misuse of photographs taken out of their original context.
- The lower right toggle shows authorship information as well as the Capture Certificate containing information about the photo’s authenticity.
- The lower left toggle shows the photojournalist’s backstory for shooting the image.
- The top left toggle shows other related photos.
- The top right toggle shows additional links related to the photo and story.
To introduce the new feature, the BCN team added a short editor’s note to accompany the stories. The Nuts and Bolts article summarized technical details about Four Corners and the technology used to create the metadata displayed with it.
As part of this work, Starling worked with the Four Corners team to develop a C2PA-compliant metadata schema for bundling rich contextual metadata in C2PA manifests. This schema contained all the metadata contained in each of the Four Corners toggles. This data is then included in a C2PA manifest, and parsed by the WordPress plugin, for presenting contextual and provenance information on each article.
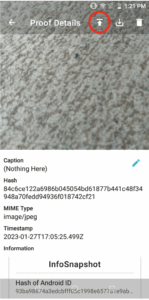
Capture Certificates & Blockchain Registrations
During the Capture step, at-source metadata was collected by the HTC Exodus 1S phone and sent to the Starling server. This data at capture time was registered to blockchains and bundled with the image for BCN photo editors to process with tracked changes. With the Four Corners interface, Starling added a Capture Certificate to surface this information to the reader. This could be compared to a “certificate of authenticity” and is a precursor to the subsequently introduced concept of Content Credentials.
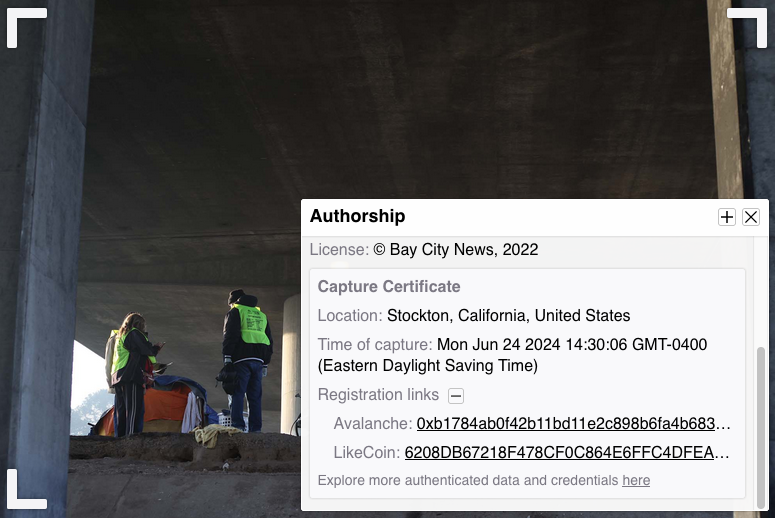
Exploring Blockchain Registrations
Starling used immutable ledgers to register digital content in this project. This assists experts wanting to audit the provenance and authenticity of the content. The unique digital fingerprint and provenance information of each photo recorded on blockchains serves as a proof of existence, while the digital signature helps establish the identity of who took the picture. All of this is indexed on a publicly-explorable blockchain to provide a public facing record of what exactly was created, and when.
Readers explore the blockchain registration information in these BCN stories by hovering over an image and clicking on the bottom right corner. Expanding the Registration Links in the Capture Certificate would display blockchain transaction IDs that can be found on public explorers for the Avalanche and LikeCoin blockchains.
Verifying Content Credentials
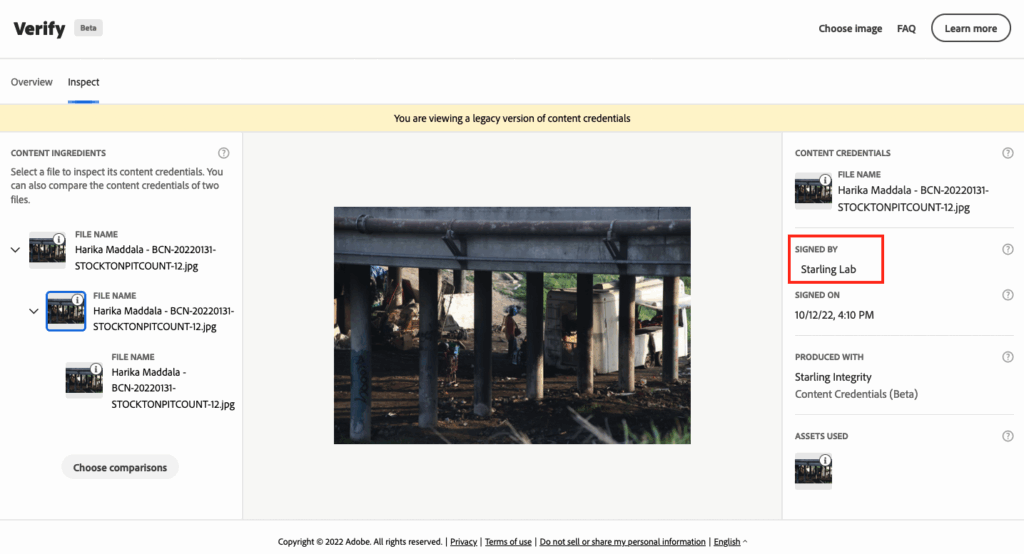
Clicking a link in the bottom right text of the Capture Certificate opens up the authenticated image on a browser-based verification interface called Verify.
Verify is a tool created by the Content Authenticity Initiative (CAI) to help make content transparency a standard across the internet, and to make Content Credentials accessible to everyone. Any of the authenticated photos from the published articles can be downloaded and viewed in this tool. As this project was done before the first production version of this tool was released, you need to use the Verify Beta tool to view the images and metadata from this case study.
This interface displays the thumbnail and metadata contained in the C2PA manifests, protected by a cryptographic signature at each of the three steps, detailing the original capture by Harika, followed by photo edits (with Photoshop), and lastly the addition of Four Corners rich contextual metadata. Versions of edited photos can be compared side-by-side or in an overlay with a slider feature.
Custody Tokens
As an additional experiment, we minted a non-fungible token (NFT) for each of the 48 original images selected for authentication to publicly track custody of each image asset. The purpose of this experiment was to explore using the transferability of a digital representation of an asset to signal the custodian of the asset.
At the moment, producers of a digital asset, whether it be a photograph or an article, are oftentime expected to be the long-term stewards of the content they produced. But this is not always what happens in practice. Just as notable works often become preserved by museums and estates, it is also possible for photojournalistic work to transfer from one custodian to another. The non-fungibility aspect of an NFT allows for authentic representation of a digital asset, and the token features allow for transferability based on a set of rules.
Note that transfer of the token does not imply moving of the digital asset from one storage system to another, nor any change with respect to the terms of use or distribution strategies. It simply announces to the public who is the primary custodian of the digital asset, empowered to make the decisions listed above.
Readers can explore the collection, where each SPCT token represents an archive containing an authenticated image and metadata.
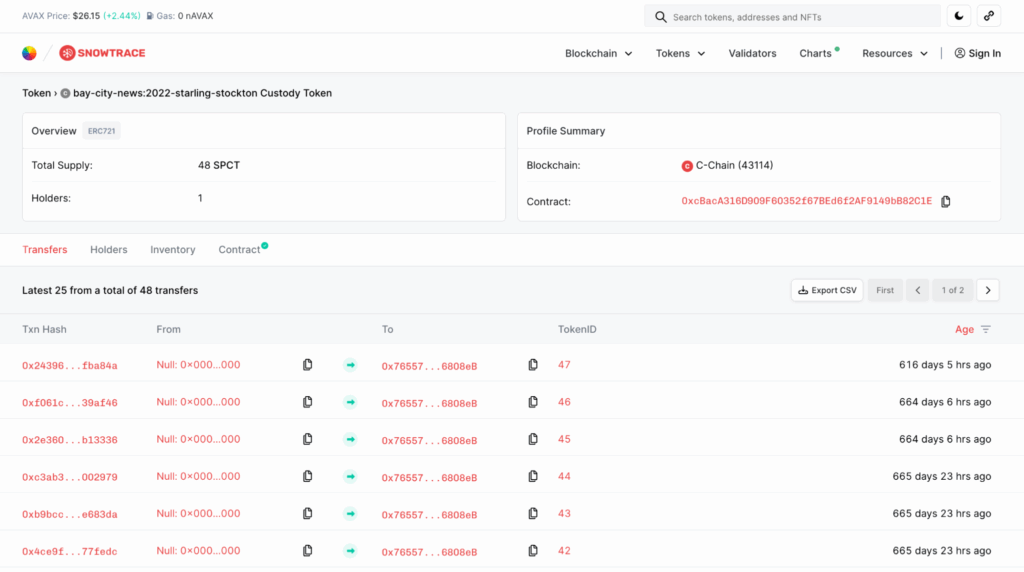
At the moment, the archives of this project are under the custody of the project team. But if the stewards of the original assets were to change, the tokens can be transferred to another institution for continued stewardship. The transfer history allows the public tracking of the chain of custody, as important assets are not necessarily maintained by a single institution forever. This provides an indication to the public of who to reach out to for access to specific assets.
Contents
Learnings
The Capture Setup in the Field
Several difficulties were encountered using the newly developed camera and phone setup in the field. Having both a camera and phone increased the number of devices a photojournalist needed to carry and interact with. The Starling Capture application allowed only one camera to be connected at a time, limiting the photographer to use the lens that is connected to the camera, as switching lenses would require reestablishing the WiFi connection. In some assignments, BCN’s team carried two cameras with different lenses, each tethered to a different HTC Exodus 1S.That increased the number of devices carried by the photojournalists to four. Management of these devices got overwhelming.
The photo shooting experience also became more challenging. First, the photojournalist needs to ensure an active WiFi connection exists between the camera and phone. Then there are limitations to continuous “burst” shots, a common practice where tens of photos get captured in a matter of seconds. Not all images were received by the phone when shooting in burst mode, with an average of 3 of 5 photos successfully transmitted while others were skipped. The skipped shots still existed on the camera SD card, but never made their way to the HTC phone.
Another issue was battery life. The WiFi connection drained the battery on both devices. While camera batteries can easily be swapped out, the HTC phone took a long time to recharge.
Several of these issues could be addressed by integrating similar technologies directly onto cameras, or designing products and systems to address them prior to manufacturing.
Digital Signage with Secure Enclaves
In this project, alongside standard software at-source signatures, the Starling Capture application prototyped a combination signature scheme that leverages the Zion hardware-secured signing key available on the HTC Exodus 1S. This key was generated by the phone hardware while configuring the Starling Capture application, and it served as a unique identifier tied to the secure enclave on that phone. This is the optimal standard for digital signing key management on a field device. The expected signer is known to the servers ahead of time, and signed data received can be verified to be originating from the particular device, with very little risk of key compromise.
The straightforward approach would have been to use that hardware key to sign every image and metadata bundle.
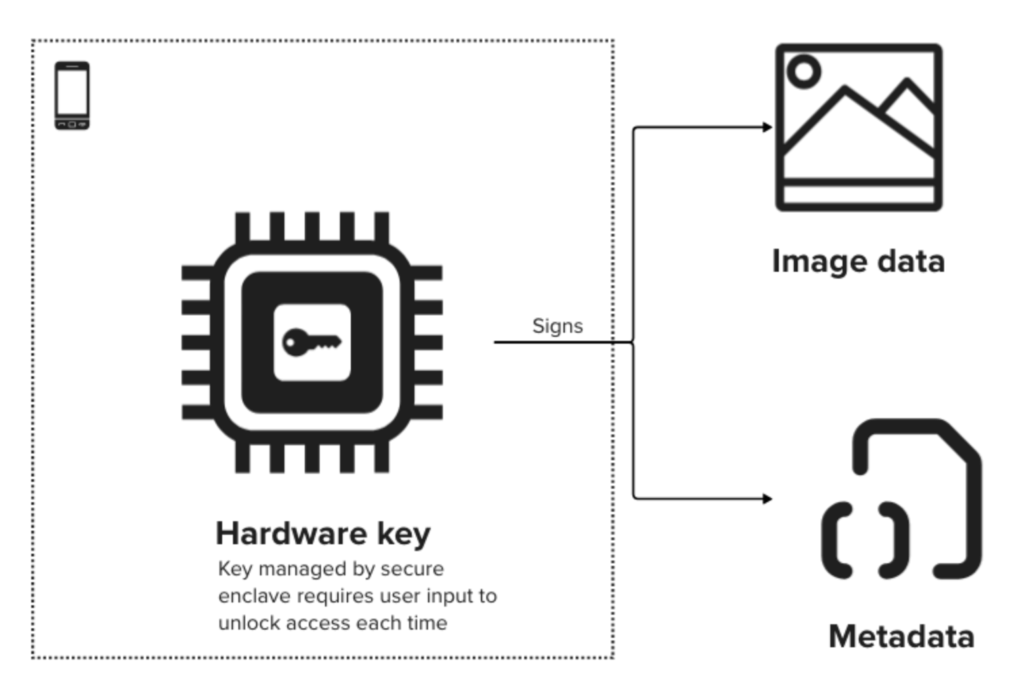
This is impractical, however, as Zion requires the user to type in a password every time the key is used to sign data. A photographer rapidly shoots many photos, sometimes triggering tens of signing events every few seconds. As a result, a temporary session key, not secured in specialized hardware, is used as the signing key.
This presents an opportunity for design of future phones and cameras with a secure enclave. When designing devices with hardware-based secure enclaves, it is important to consider use cases where requiring user authentication for every signature may be impractical
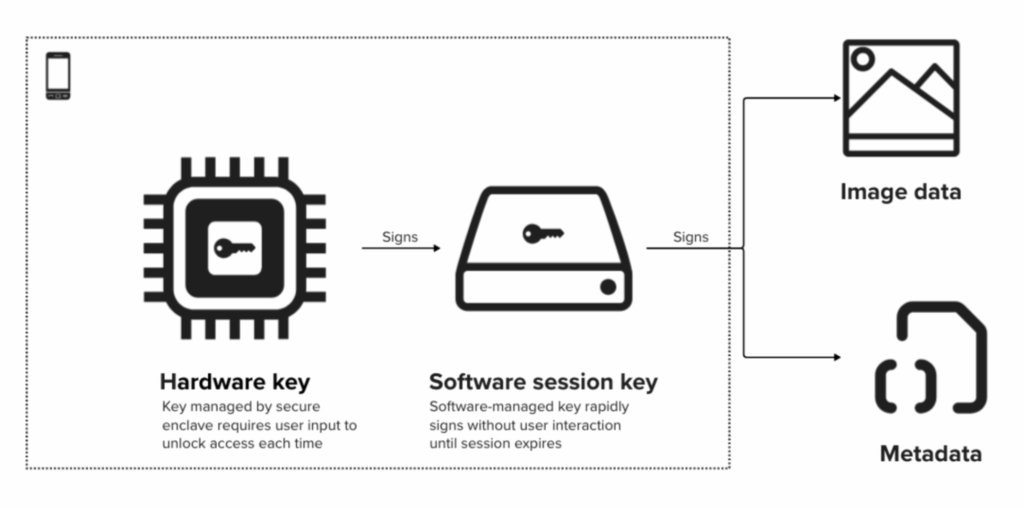
For this case study, we worked around these issues by generating a software session key for signing assets quickly for the duration of a single user session. This key itself is signed when it was generated with the hardware key, giving it a high standard of trust but improved speed and ease of use for a limited period of time.
For future device design, we recommend natively supporting authenticated sessions that have expiry triggers, thus allowing multiple signatures to occur without separate user authentication. Otherwise these features will be implemented in application software, rendering the overall solution less secure and verification more complex.
To verify the hardware root of trust, both signatures in the two-signature chain must be verified. In other words, one must verify the image and metadata signature by the software session key, then verify the signature of the software session key by the hardware key. Unfortunately in this deployment, due to a bug in the particular version of Starling Capture, the hardware key signature was not preserved with each photo. Therefore we cannot verify each photo against the hardware-secured root of trust.
In parallel, another software key based on AndroidOpenSSL was used to produce signatures that gave us a redundant at-source signature for the same data, and these signatures were intact across all versions of the app. This static software key was not session based, and was used to sign the data directly.
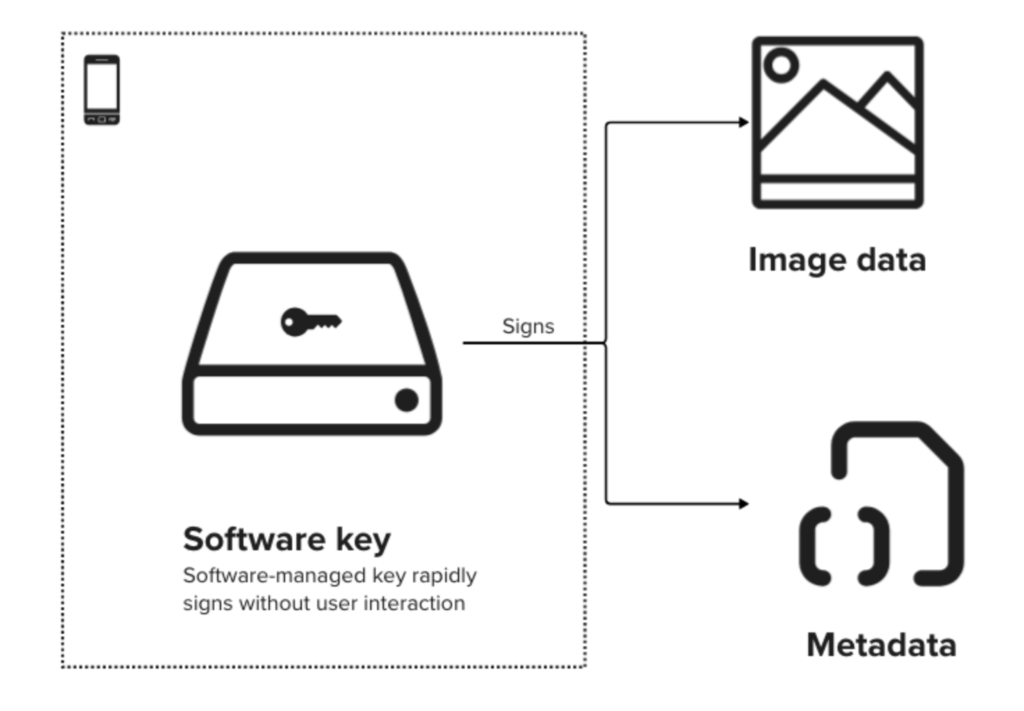
Since this key was not hardware-managed in a secure enclave, it would be more vulnerable to key compromise on a field device. However, in our controlled deployments with trusted fellows and Starling-provisioned hardware, we have high confidence that the software key is untampered, and we can rely on the digital signatures produced.
This experiment highlights the importance of automated verification of all signatures at every opportunity, and especially as data crosses system trust boundaries. For example, when the backend server receives a signed message, it should first discover what set of signatures are contained in the message, and then proceed to verify all of them. This assures all information required for verification is provided.
Another place where errors may occur is during preservation of these signatures. An incident occurred in another implementation where metadata was signed and transmitted as JSON payloads. The backend system proceeds to parse the JSON data, then writes the data back to disk. However, when it is read back again for verification, the ordering of the JSON content is altered. The two JSON documents are semantically equivalent but bit-by-bit different, and therefore no longer verify with the original signature. The original ordering transmitted was essentially lost in this process, making retroactive verification impossible.
The method to combat this type of error has evolved from first applying a round of binary-to-text encoding (e.g., Base64) to original data before signage and storage. Later implementations stored canonical representations such as JCS and CBOR with deterministic ordering of data. Similar challenges exist when data is “chunked” for hashing under certain implementations, and methods that standardize on this process such as BLAKE3 are adopted to provide determinism at verification.
Editing with Adobe Content Credentials
The C2PA specification, along with its tooling, were in early beta during this project. Updates that are not backward-compatible in the Content Credentials beta feature in Photoshop v23.1.0 occurred after some of the photos were captured and before the editorial team had an opportunity to edit them, leading to incompatibility in the C2PA tracking features during the edit phase.
Additionally, tracking of edits in Photoshop were limited. According to BCN Photo Editor Ray Saint Germain, “We wanted to see more from Adobe’s Content Credentials tool: to record detailed changes to photos including details of what was done with color adjustments – such as curves, hue/saturation, levels, etc. – and list of filters used.”
In other words, the version of Photoshop Content Credentials used at the time could be improved with more robust recording of editing changes showing the values of tonal changes, saturation, and any composition adds or removals.
Adding captions to photos with tracked changes proved to be challenging. Software like Photo Mechanic and Adobe Bridge could not be used because they didn’t have C2PA features to track changes, so captions must be entered using Photoshop, which did not offer a batch captioning feature and instead required toggling through multiple fields in the program’s interface. We also discovered that when exporting photos (rather than save), which was required for using the Content Credentials feature, Photoshop did not include captions with the exported images.
Due to these challenges, the team decided to sign photo edits with our own signing certificate for some of the files rather than to use Photoshop’s built-in Content Credentials. Therefore, for some photos in the project, readers will find edits that are signed by Starling Lab rather than Adobe.
This project used a very early pre-1.0 version of the C2PA Specification. Subsequently, versions 1.0 and 2.0 have been released. Content Credentials as a feature in Adobe Photoshop has also been improved, adding more granular change tracking, the ability to add information about the producer (Adobe account owner), among other updates.
Integrating Four Corners with C2PA
This was the first implementation of the Four Corners project with C2PA support. The process of formatting and adding the data that would appear in each of the Four Corners displays was mostly done manually. These displays allowed users to dig deeper to examine metadata and related assets.
Though this manual entry could be easily done for a small set of images, any newsrooms that wanted to do this on a larger scale would need to have a system for easily ingesting and formatting data to correctly display in the Four Corners WordPress plugin.
Authentication Ecosystem & Business Model
In the world of deep fakes and generative AI, BCN Photo Editor Ray Saint Germain expresses the importance for Bay City News to authenticate all images made available to its clients.
“We source photos from subjects, agencies and public sites for many of our stories and each photo is vetted for authentication and copyright. Our clients, knowing the photos made available to them have been vetted, is a value we are working on monetizing by subscription and a la carte purchases.”
– Ray Saint Germain, BCN Photo Editor
Saint Germain points out how signed contextual and integrity metadata “could help us monetize our photos if other news organizations, viewers and even commercial clients who care about the integrity of the images are willing to pay a premium for them, knowing that the content is authentic.”
This remains to be tested, however. Saint Germain also states, “as it stands, most of our newswire clients, SF Bay Area print, radio and TV stations, China Press, New York Times and others, say they want photos but few would voluntarily pay for them because they are not concerned about high-quality images. Instead, they rely on user generated content submissions, stock photos, their own archives, or one master source like the Associated Press. So to charge even more for the authenticated photos might be a high bar.”
Importantly, with the related costs of equipment, software developers, blockchain registrations, and staff time, BCN Foundation and other similar-sized newsrooms can’t accomplish this without adequate financial and technical support, or an ecosystem of affordable tooling. The development of cameras, content management, sharing, and editing tools, along with interfaces that allow inspection and exploration by verifiers are all part of an ecosystem that continues to be built.

Contents
Archive
- Lodi shelter participates in local homeless count
- Stockton mourns killing of fire captain as he responded to emergency call
- A look at the day-to-day life of an unsheltered Stockton man and how he copes with regular displacement
- Stockton’s new Respite Center helps addicts get clean and sober on their path to recovery
- A matter of trust: Inside Stockton’s Police Department and the residents they serve

