Preserving Harvard Public Health on the Distributed Web

Capture
In late February 2025, Harvard Public Health magazine announced it was shutting down. Editor-in-chief Michael F. Fitzgerald delivered the news plainly: journalism is expensive and outside of a university’s core mission of teaching and research. The magazine, which had relaunched as a digital-first publication and tripled its readership in the final year, ran out of time to build sustainable revenue streams.
The closure is another casualty in the ongoing challenge of funding quality public health journalism. Harvard Public Health had covered topics ranging from the Flint water crisis to processed foods, mental health, and structural racism – work that won recognition and built an audience of nearly 15,000 newsletter subscribers, 90 percent of whom had no connection to Harvard.
Fitzgerald encouraged readers to download articles they found useful before the site eventually goes dark. But individual downloads are an imperfect solution for preserving a decade’s worth of public health journalism. The question became: how do we ensure this body of work remains accessible to researchers, public health professionals, and the public long after Harvard stops paying the hosting bills?
The Distributed Press Clone API
Distributed Press is an open-source publishing tool developed by Hypha Worker Co-operative and Sutty Coop that automates publishing and hosting content to both the traditional web and decentralized protocols like IPFS and Hypercore. Where traditional web hosting depends on a single provider, distributed networks allow anyone to help co-host content – making it resilient against the kind of institutional decisions that led to Harvard Public Health’s closure.
The recently launched Clone API makes this preservation process remarkably straightforward. Rather than manually downloading and re-uploading thousands of pages, the API can crawl an entire website and publish it directly to IPFS and Hypercore.
The entire preservation took three API calls and about an hour of automated crawling.
Technical Walkthrough
Here are the steps to preserve a website using the Distributed Press Clone API:
Step 1: Obtain API Access
Distributed Press requires an authorization token. Instructions for requesting access are available at distributed.press/2024/10/18/get-a-token/. Once obtained, the token is entered into the Distributed Press API Swagger interface.
Step 2: Create a Site Configuration
Using the API, create a new site with the target domain (harvardpublichealth.org) in the configuration bundle. This tells Distributed Press which domain to crawl and how to structure the resulting archive.
Step 3: Initiate the Clone
Call the Clone API endpoint to begin crawling. The system works in the background, following links and downloading assets. For a site the size of Harvard Public Health, this takes approximately one hour.
Step 4: Query Site Information
Once complete, query the site information to retrieve the archive’s addresses on both protocols. The API returns a JSON response containing the IPFS CID (Content Identifier), Hypercore key, and various gateway URLs.
Accessing the Archive
The preserved Harvard Public Health site is now available at two permanent addresses:
IPFS:
bafybeihg5mdtwrfa4ywm4orsloojvysuaurr36p57tlwshydv2rgbxws5a
Accessible via gateway:
https://bafybeihg5mdtwrfa4ywm4orsloojvysuaurr36p57tlwshydv2rgbxws5a.ipfs.ipfs.hypha.coop/
The IPFS CID is a cryptographic hash of the content itself. As long as anyone on the IPFS network continues to pin this CID, the content remains accessible – regardless of what happens to Harvard’s servers. The same principle applies to the Hypercore key. These addresses are permanent: they will always point to this exact version of the site.
Why This Matters
Web content is fragile. Studies have found that the average lifespan of a webpage is measured in years, not decades. Institutional priorities shift, budgets get cut, and valuable archives disappear without warning. The Harvard Public Health closure is a textbook case: the institution decided journalism wasn’t core to its mission, and a decade of public health reporting became an orphan.
Traditional archiving solutions like the Internet Archive’s Wayback Machine provide important preservation, but they operate as centralized services with their own resource constraints and priorities. Distributed protocols offer a complementary approach where preservation becomes a collective responsibility. Anyone who values this content can pin it to their own IPFS node, helping ensure it remains available.
For researchers and public health professionals, this archive preserves not just individual articles but the navigational structure of the original site – the way topics were organized, the relationships between pieces, and the editorial voice that connected them. That contextual integrity is often lost when content is scattered across individual downloads or incomplete archive snapshots.
Replicating This Process
Organizations with valuable web archives, whether facing shutdown or simply wanting redundant preservation, can use this same approach. The process requires:
- An account with Distributed Press (contact the team for access)
- A domain configuration for the target site
- Sufficient time for the crawl to complete
The resulting archives can be pinned by anyone with an IPFS node or Hypercore peer, distributing the preservation responsibility across multiple parties and jurisdictions.
For those interested in the technical implementation, the Distributed Press documentation is available at docs.distributed.press, and the Clone API is documented in the API reference.
Next Steps
This preservation effort was initiated independently by Hypha, but demonstrates a workflow that could be systematically applied to at-risk publications. As journalism continues to face financial pressures, having fast, reliable tools for distributed archiving becomes increasingly important.
We encourage institutions facing similar closures to consider distributed preservation as part of their wind-down planning. We also encourage researchers and archivists to pin this CID and contribute to the network of peers keeping Harvard Public Health’s journalism accessible.
If you have questions about applying these techniques to your own preservation needs, reach out to the Distributed Press team via their documentation site, or contact Starling Lab at info@starlinglab.org.
This project was documented by Hypha Worker Co-operative. The preservation was completed using the Distributed Press Clone API on March 4, 2025.
Pilot Project on Making Web Preservation Easy for Investigative Journalism
Capture
In the digital age, the “smoking gun” is often a fleeting URL, a social message that gets edited minutes later, or a listing on a grey-market website that vanishes once a sale is made.
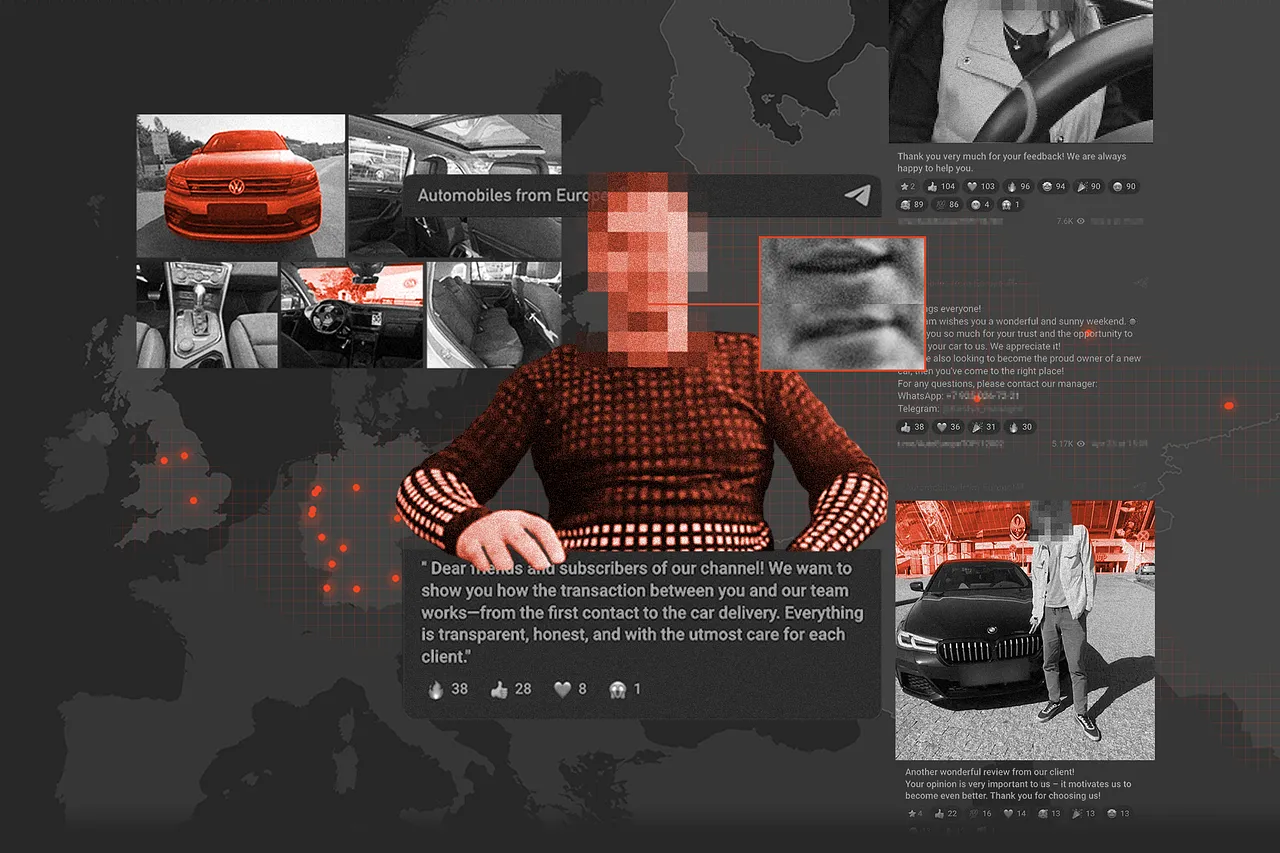
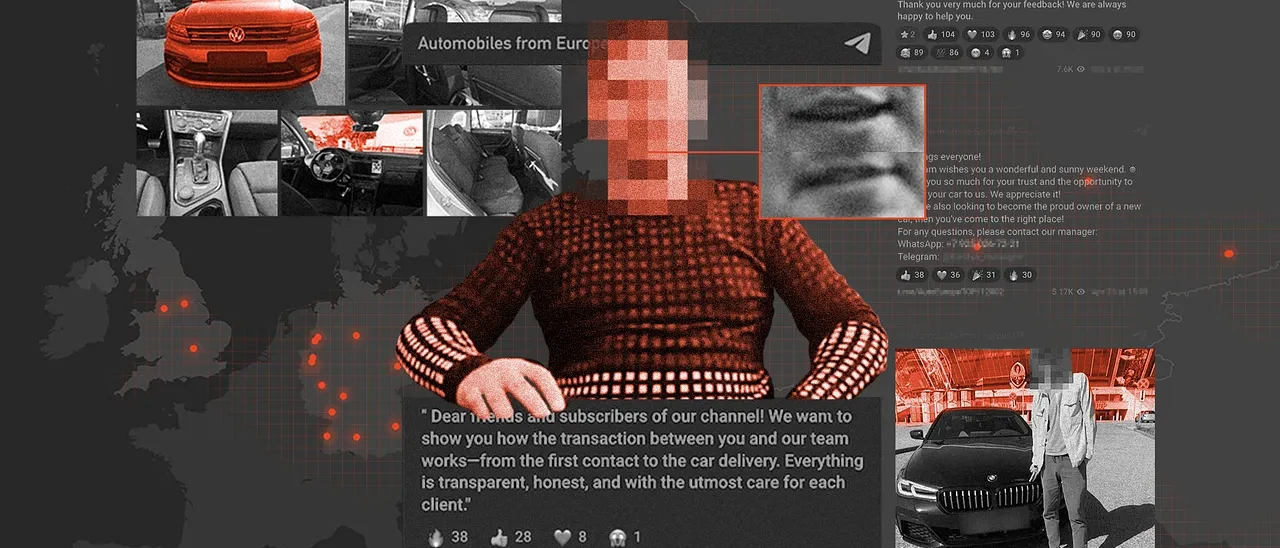
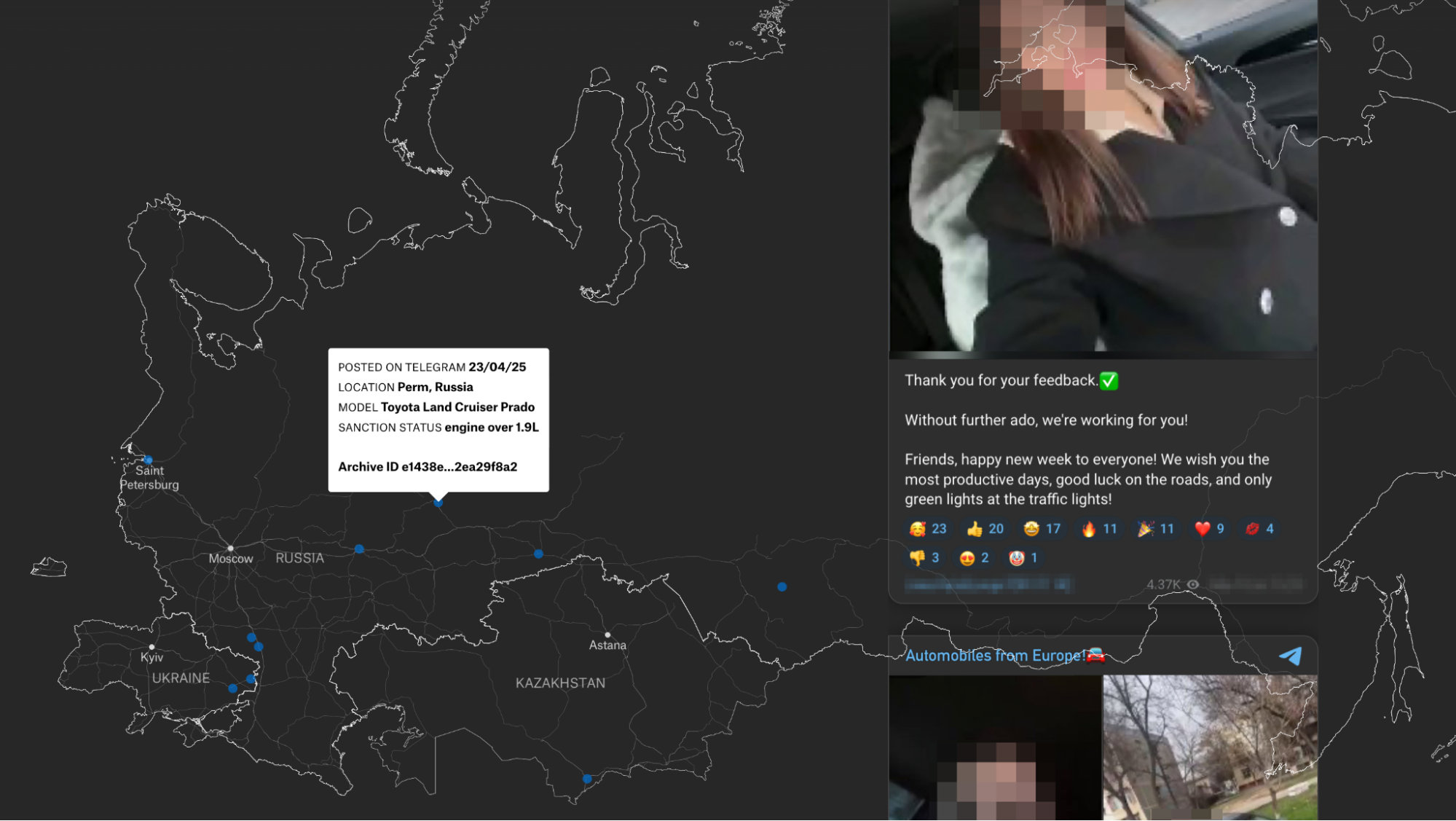
Today, we are proud to announce the publication of “Sanctions, Scams, and Deepfakes,” a major investigation by our partners at Airwars into the illicit flow of luxury cars from Europe to Russia. Starling Lab worked in support of the investigative team to preserve the digital evidence supporting their findings, while the reporters traced the physical movement of vehicles across borders.
At least, that’s what they originally set out to do.
At the center of this investigation into the apparent smuggling operation of cars into Russia laid a red herring. The investigative team initially believed they were tracking real sanctions-evasion schemes bringing luxury cars from Germany to Russia, but instead discovered the operation was largely a scam targeting Russians themselves. The deepfaked video of a legitimate Russian car dealer explaining the smuggling process, the paid actors posing as satisfied customers, and the geolocated cars in Germany were all elaborate deceptions designed to make the fraud appear credible – with potential victims losing thousands of euros to scammers likely operating from Ukraine rather than to actual smugglers delivering sanctioned vehicles.
The investigation was supported by IJ4EU, a grant scheme for cross-border investigative journalism in Europe. The Starling Lab did not participate in the grant application, nor did it receive any funds. Our support of the investigation was purely pro bono and limited to that project.
Technical Stack Deployed
During the investigative phase, the research and investigative team needed to browse hundreds of online sources, from Belarusian border cam footage to social media and social messages.
The core technical challenge was clear: How do we allow investigators to move fast while maintaining a forensic chain of custody? A simple screenshot is insufficient for legal or historical proof. We needed a system where an investigator could claim, “at this time and date, I browsed this unique URL which contained precisely this content,” and be able to back it up with cryptographic proof.
Fortunately, we have been working with state-of-the-art web archiving tools for years – and have even produced a whitepaper on best practices for web archiving. The approach described in this project aims to ensure the collected material meets the high bar for authenticity and probative value required in legal proceedings. It directly addresses the belief that these tools and techniques can be cumbersome or slow down the investigative process.
This perception being a key barrier to adoption, we set out to build a bridge between consumer-friendly tools and forensic-grade archiving. We recommended the team use Raindrop.io, a lightweight browser extension, to bookmark relevant links and add annotations. This allowed the investigators to simply “click and save” without leaving their browser.
Behind the scenes, however, a preservation pipeline was built: on schedule, Github Actions would trigger Typescript scripts tasked with fetching new bookmarks that might have been added to Raindrop; and where appropriate, to schedule their individual crawling in the Starling Lab Browsertrix Cloud account.
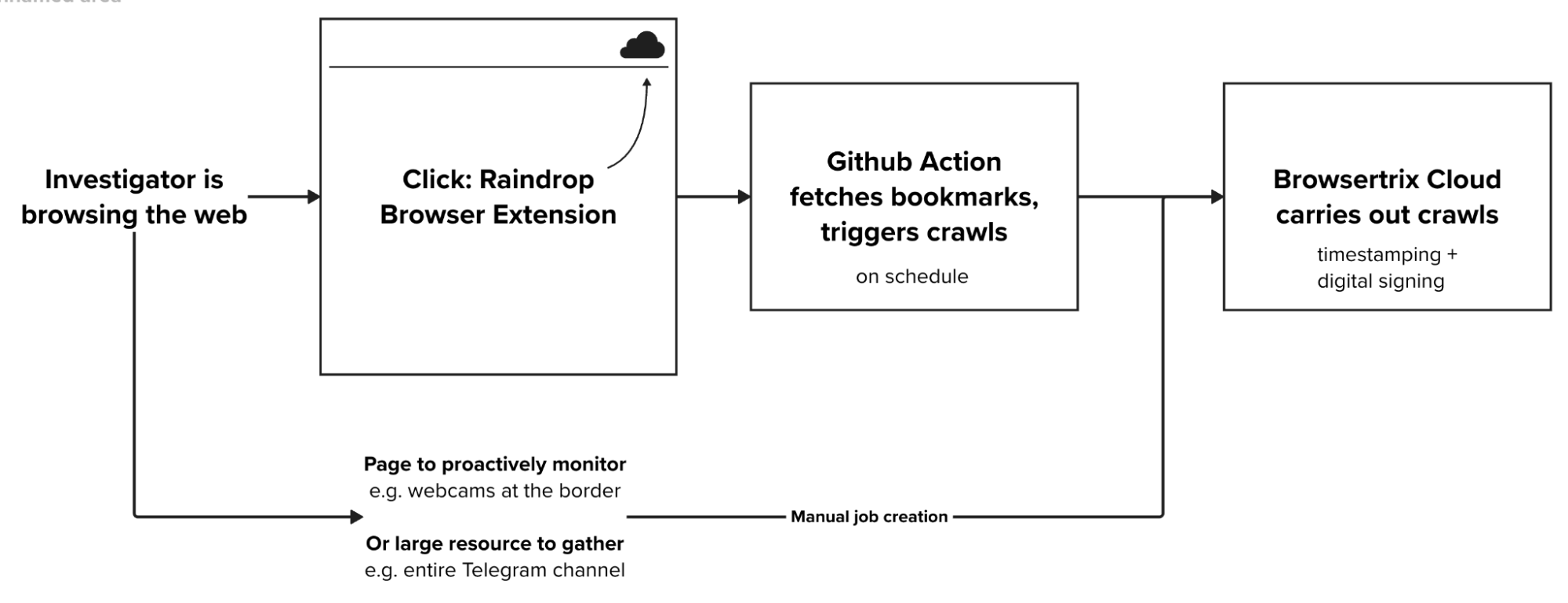
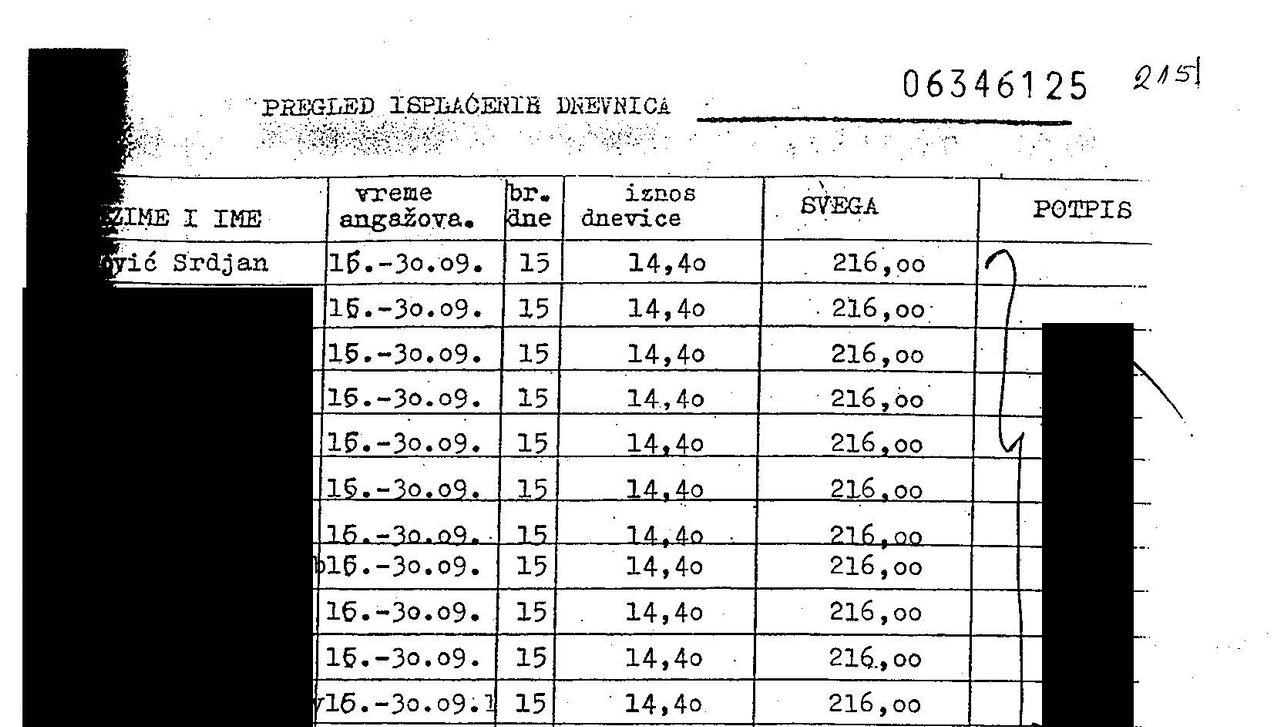
In total, we preserved more than 9,000 unique URLs, totalling 98 GiB in compressed form.
A major early lead was the case of the border crossing between Lithuania and Belarus, which the team understood as a key milestone in the supply of cars into Russia. The border crossing is monitored by webcams that refresh every 10 minutes or so. By running our crawls on schedule, we were able to provide the team once a day with a collage of captures – in the hope of substantiating that one of the known delivery lorries was doing the journey, as the Telegram channel seemed to claim e.g. below:

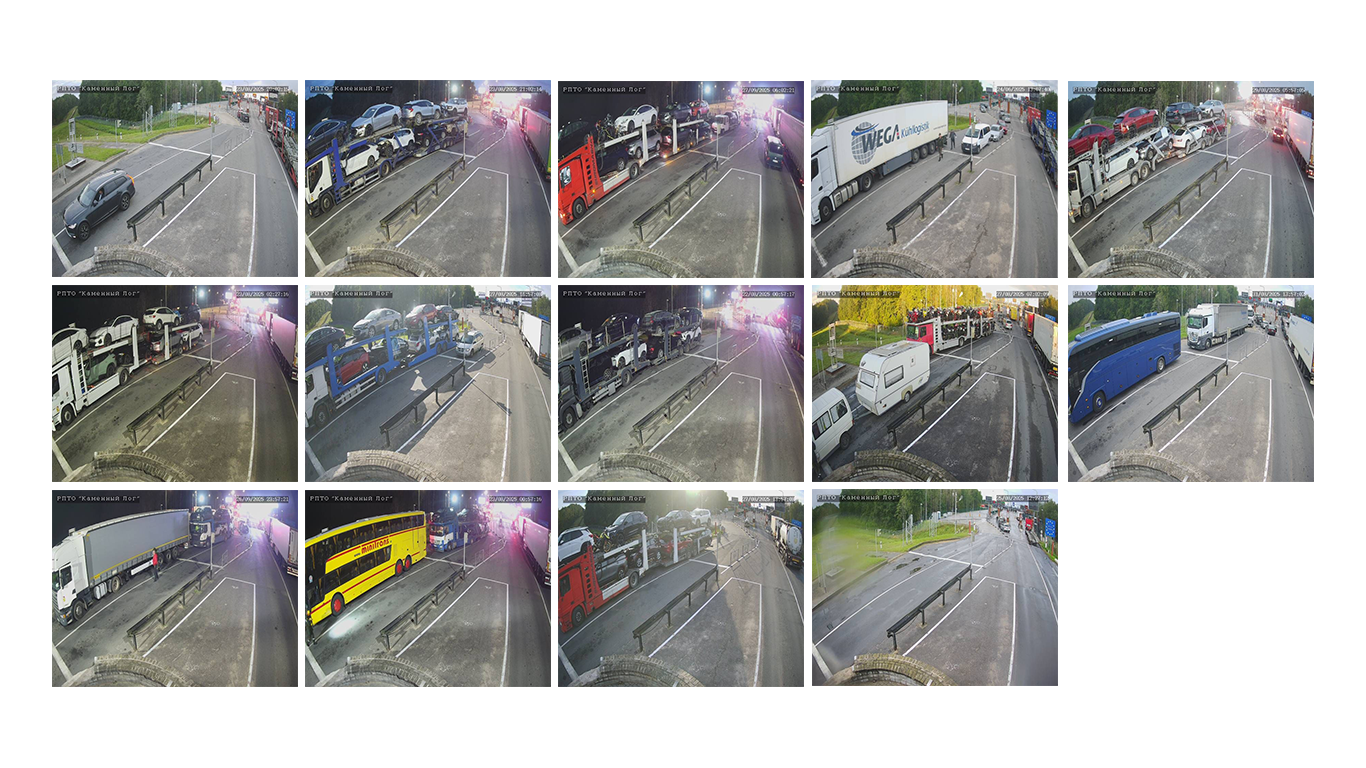
Despite monitoring the webcams for a month and a half, reviewing about 3,800 photographs (two shots every 10 minutes most hours of the daytime), we were not able to find one of the known trucks.
We, however, witnessed the spectacle of political opposition Mikalai Statkevich sitting in this no-man’s land after having been freed from Belarus, reportedly refusing to walk to Lithuania and go into exile.

Learnings
Proactive engagement
The earlier and the more closely we are involved, the better our chances to do good work. This oft-repeated canon of collaboration is worth its salt for a reason.
In the context of this investigation, we think we were able to support the collection of web content to a fair extent. Frequent touchpoints with a team helped identify developing parts of their workflow – for example the need to monitor the webcam photographs, which were being overwritten relatively frequently.
Time and opportunity to engage
As the story pivoted from tracking the supply chain to the realisation that key elements had been fabricated and were deepfakes or shallowfakes, the pressure to make a looming deadline led to a tightening of the loop on the investigative team’s side. The result of that was material received by investigators in the last days, prior to publication, was not shared with us for authentication and preservation.
Furthermore, we had prepared for a planned field trip to dealerships in Lithuania, and ran a short training for reporters on using the Proofmode app to take photographs, cryptographically seal them, and share them on – this trip however never materialized as the story pivoted away.
Seeing as the investigation relates to both forgeries and inauthentic material, we regard these omissions as missed opportunities.
The need for redactions
The pre-publication legal review sought by Airwars led to a cautious treatment of the evidence collected. The story was complex, with a good deal of uncertainty about what was real, and which of the persons and organisations involved were in full possession of the facts.
While technically well within reach, we opted to not publish full embeds of the Telegram posts and messages, as well as to redact some metadata from them. We are also not making the archive publicly accessible. These measures aim to protect car sellers, dealerships, clients, and anyone else whose photographs might have been used against their will and in support of the scam.
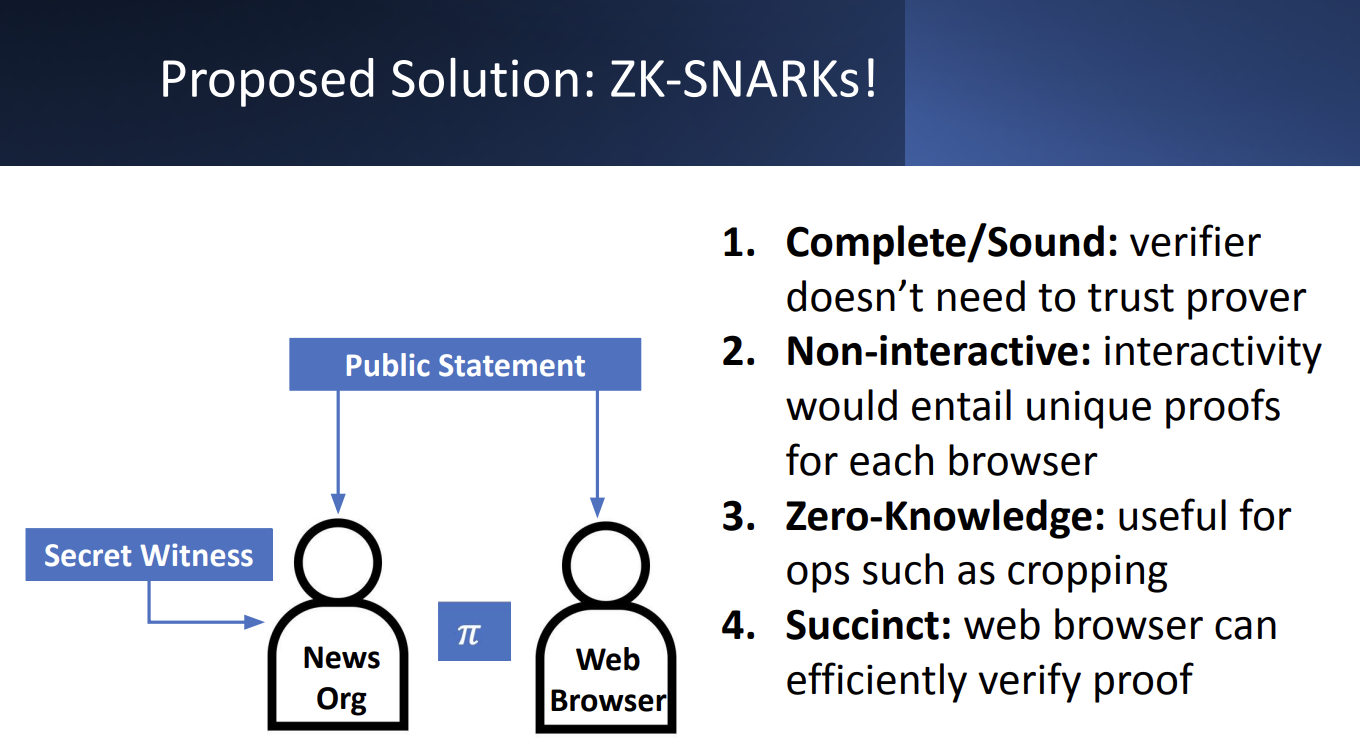
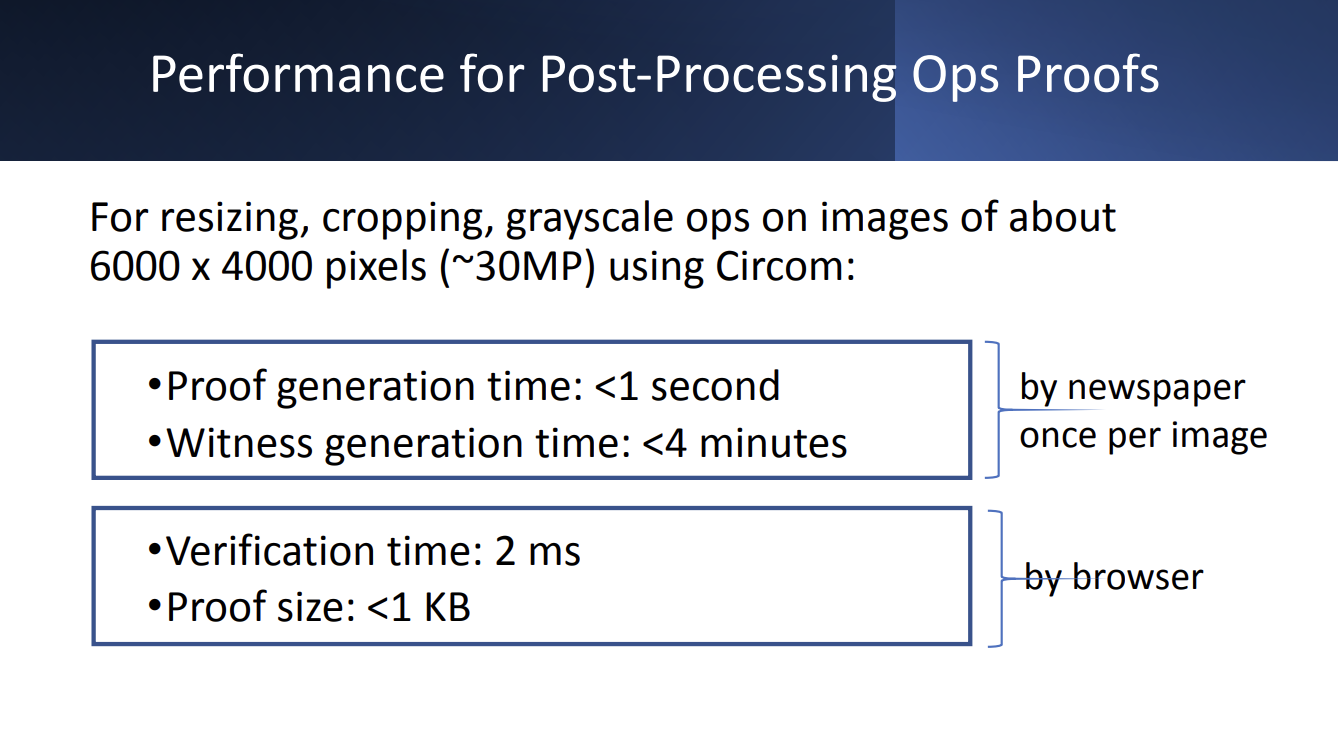
This case study further underscores the need for verifiable redaction technology to be part of the feature set of web archiving tools for journalists. In service of this requirement, we have deployed techniques from the field of Zero-Knowledge Proofs in our Rolling Stone investigation into war crimes in Bosnia. This technology allows publishers to redact sensitive information (such as names in documents or metadata in digital files) while generating a mathematical proof that certifies only specific pixels or data fields were obscured.
Scaleable
This pilot project allowed us to test and refine a preservation mechanism that is both robust and non-intrusive to the investigative workflow. We are eager to further deploy the processes developed during this collaboration, and this model more broadly, for future investigations and other partnerships with journalistic organizations.
Submission to the UN Special Rapporteur on Human Rights Defenders from our Brazil Coverage

Capture
We are honored to see our work featured in Mary Lawlor‘s UN Special Rapporteur report to the Human Rights Council: “Out of Sight: Human Rights Defenders in Rural, Remote and Isolated Contexts.”
UPDATE: Since this was published, the UN Human Rights Council adopted a resolution on protecting human rights defenders in the digital age. It addresses several important issues that our Lab has been focused on. Scroll to the end of this page for more details.
The report notes how Starling Lab supported efforts in Brazil’s Pantanal wetlands with tools that work even in low-connectivity environments, which is needed where the “digital divide hits many human rights defenders very hard.”

In a speech this month presenting her findings, Lawlor observed how some of those most at-risk include “journalists covering human rights issues at the local level.” Starling’s methodology was used by journalists to document environmental destruction – and confront climate change denialism. Our submission to Lawlor’s office focused on data authentication, decentralized storage, and cryptographic verification. Together, these ensure documentation remains tamper-evident and accessible, even when governments seek to dismiss the truth.
Her report includes several valuable recommendations to governments and other international actors, two of which resonate with our work:
- “Expand access to the Internet and secure communication tools, including by increasing funding for such digital security resources as encrypted communication applications and secure reporting channels.”
- “Support efforts to enable human rights defenders to store and safeguard their information securely, without fear of unlawful surveillance or data breaches, including putting in place robust legal safeguards to prevent the misuse of digital tools to suppress dissent or target defenders and ensure that their digital rights are protected.”
We appreciate being included among so many other human rights defenders, and remain grateful to Pablo Albarenga for his photojournalism in Brazil, as well as to Inside Climate News for publishing this important coverage.
And we hope this underscores the vital role of trusted digital evidence in defending human rights and environmental justice.
🔗 Read the Special Rapporteur’s remarks;
📄 Read the full UN report;
📕 Don’t miss our own case study;
📰 And the Inside Climate News article
Starling Lab was previously referenced in a report to the UNHRC in 2023 by the Rapporteur on the right to education, who acknowledged similar methods used by the lab as emerging “good practices” for documenting war crimes against civilian objects like schools.
Update (April 16, 2025): Our submission is also echoed in a new resolution from the UN Human Rights Council, which addresses the protection of human rights defenders in the digital age (full text: A/HRC/58/L.27/Rev.1).
The resolution emphasizes “universal connectivity” and “meaningful connectivity” as essential for defenders’ work, calls for “technical solutions for strong encryption and anonymity,” and advocates for secure information storage “without fear of unlawful surveillance.” It specifically recognizes the “growing number of digital attacks” on defenders and acknowledges the “protection gap” caused by lack of accountability.
These address key points from our submission on data integrity and authentication technologies for remote areas.
We’re particularly encouraged by the HRC’s recognition that “new and emerging digital technologies can hold great potential for strengthening democratic institutions and the resilience of civil society, empowering civic engagement and enabling the work of human rights defenders, public participation and the open and free exchange of ideas, and for the exercise of all human rights.” This aligns perfectly with our mission at Starling Lab to harness technology to establish trust in digital records.
Our earlier submission outlined innovative approaches to produce documentary evidence and combat digital denialism. This includes cryptographic methods that authenticate evidence from the point of capture, enabling defenders in remote areas to establish credibility despite connectivity challenges. The submission also referenced ongoing work on telecommunication technologies, including 5G, to further enhance these capabilities.
Secure Enclave Signing
Capture
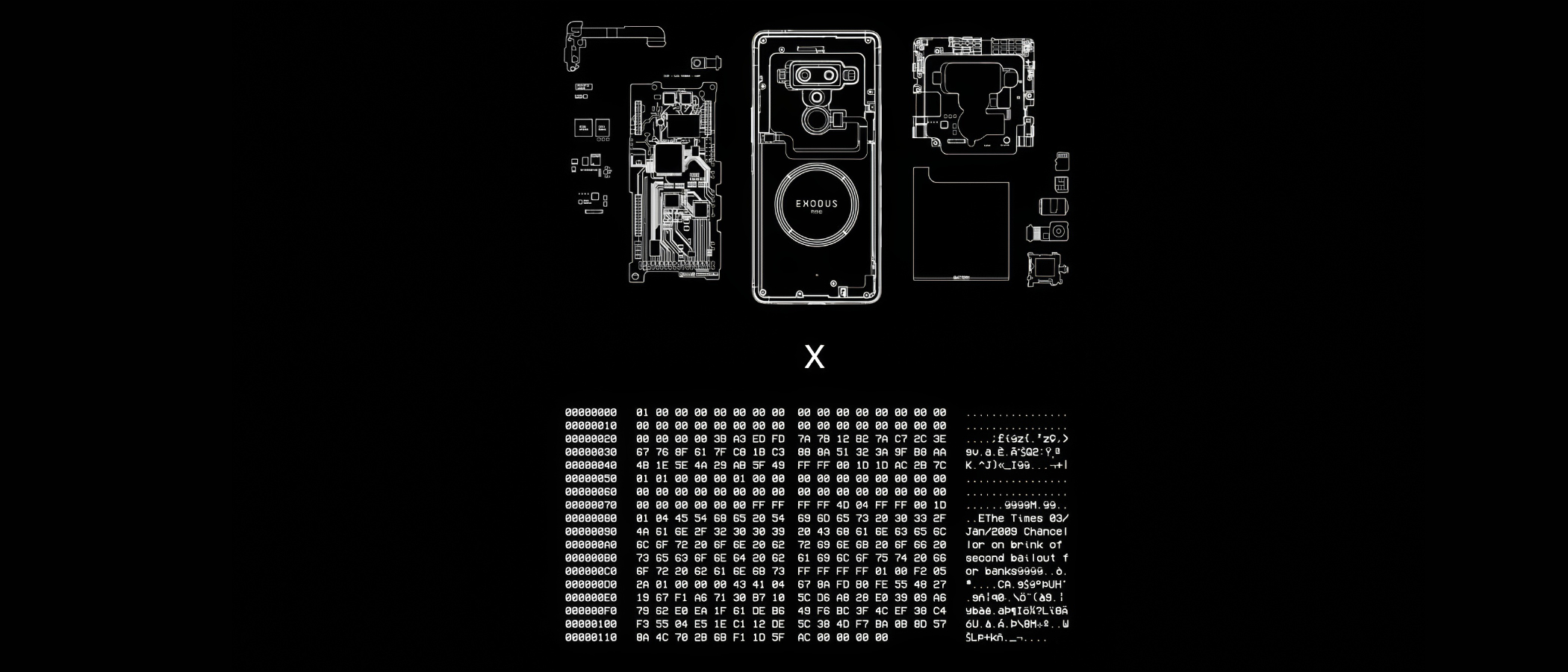
This prototype establishes a hardware-based root of trust for digital media by cryptographically sealing assets inside a device’s protected silicon environment. It shifts the security boundary from vulnerable software to dedicated cryptographic processors, ensuring that signing keys remain inaccessible to external threats and that every asset is tied to an immutable hardware identity.
By anchoring provenance at the absolute point of capture, it creates a foundational “proof of origin” that is resilient against both digital manipulation and systemic distrust.
YEAR
2022
PARTNERS
HTC
Numbers and the Numbers Protocol
LINKS
– HTX Exodus 1S Phone
– The Starling Framework
The Problem
The ideal environment to manage digital signing is a cryptographic processor within the capture device, where the keys are never revealed and the system will only sign data within a predefined pathway. This ensures all authenticated data carrying a signature by those keys are unambiguously originating from the capture device. Unfortunately, hardware secure enclaves and similar technology, are not widely included in professional capture devices, or implemented with sufficient firmware that supports these digital signing use cases.
JOURNALISM
Anchors in hardware rather than software support shielding reporters from deepfakes accusations, and gives them a digital “negative” as an origin record of their work.
HISTORY
By binding historical records to the unique physical identity of the capture device, it creates a resilient, verifiable archive that ensures the “first draft of history” cannot be silently altered by future actors.
LAW
Hardware-level signing establishes an airtight digital chain of custody and ensures cryptographic keys are physically isolated and never exposed, aiming to meet the most rigorous standards for legal admissibility.
The Solution
Starling Lab’s prototype utilizes Secure Enclaves (isolated cryptographic processors) to generate and store signing keys where they can never be revealed. This implementation creates a tethered workflow, pairing a digital camera with a secure-element-equipped device (such as the HTC Exodus 1S).
As media is captured, the system generates a cryptographic hash that is signed within the hardware’s protected environment, creating a tamper-evident record from the first millisecond of the asset’s existence.
This prototype serves as a technical blueprint for hardware vendors, advocating for a decentralized framework where privacy-respecting key management and data authentication are baked into the physical design of professional tools.
Timestamp Verification
Capture
We utilize distributed ledgers to establish an immutable “proof of existence” for digital media and its metadata. By anchoring cryptographic fingerprints on public consensus networks, it creates a tamper-evident record of the absolute moment an asset was first observed.
This “birth certificate” for digital data shifts the verification model from reactive detection to affirmative proof, ensuring that the origin and integrity of critical information remain indisputable against the threats of revisionism and synthetic manipulation.
YEAR
2020-24
PARTNERS
Hedera
ProvenDB
OpenTimestamps
Numbers Protocol
Solana
LINKS
– Time for Trusted Timestamping
– Reuters collaboration, ProvenDB anchored on Hedera
– ‘Mom I See War’, a collection of drawings from Ukrainian children, anchored on the NEAR blockchain using the Numbers Protocol.
The Problem
Establishing the originality of a piece of content, and that a given piece of media is the first known version has been a conundrum since the invention of written communication. Whether one is looking to resolve disputes of which version comes first, or to prove media was created before the advent of certain AI technologies, a timestamp that can be verified with a trustworthy third-party can be a helpful solution. Verifiable timestamping can be used as a part of the digital media creation, preservation, and edit processes.
JOURNALISM
By anchoring field footage hashes on public ledgers, newsrooms can maintain an indisputable record of truth that survives both link rot and malicious denialism.
HISTORY
By registering high-fidelity fingerprints of historic records before the generative AI inflection point, institutions ensure that primary sources can be definitively distinguished from synthetic noise.
LAW
Third-party ledgers act as record holders from which to derive strong claims about integrity and point of origin of a digital item.
The Solution
Starling has used several Merkle tree-based technologies to efficiently create verifiable timestamps on public ledgers, and developed workflow using systems such as ProvenDB with Hedera Consensus Service anchors, OpenTimestamps proofs anchored on Bitcoin, as well as direct registration of media assets on many public blockchains. In all these cases, the block height is used to establish a verifiable timestamp for the registered digital media.
Adding an immutable proof of existence backed by distributed ledger consensus serves to establish a first known creation of digital media that is nearly impossible to refute.
READ FURTHER
Further to this work, we have created a reference implementation of timestamped databases in a project called ‘Authenticated Attributes’ that aims to integrate with digital media user interfaces and collaboration tools.
We have also created an offline, SMS-based silent registration prototype based on 5G technology, and integrating with the latest C2PA-capable cameras.
Document Redaction
Capture
Establishing a cryptographic seal of transparency for sensitive digital records, moving beyond traditional “black-box” redaction.
Zero-Knowledge Proofs (ZKP) allow investigators to obscure personally identifiable information (PII) while providing a mathematical guarantee that no other part of the document has been altered.
This concept shifts the trust model from requiring blind faith in a publisher’s edits to providing affirmative proof of a document’s integrity, ensuring that critical primary sources remain both ethically protected and legally robust
YEAR
2022
PARTNERS
Stanford Applied Cryptography Group
LINKS
– Case Study: The DJ and the War Crimes
– Presentation from Trisha Datta and Dan Boneh
The Problem
Accountability investigations often rely on digitized primary sources – such as the UN payroll records unearthed in our Bosnia war crimes probe – that contain sensitive PII of individuals not central to the investigation. While redacting this information is a journalistic and ethical necessity, it creates a “trust gap”. In an era of widespread denialism and “cheapfakes,” any manual modification to a source document can be weaponized by bad actors to claim the entire record is a forgery, undermining the evidentiary weight of critical testimonies.
The Solution
In partnership with our principal investigator’s Professor Dan Boneh’s students from the Stanford Applied Cryptography Group, Starling developed a workflow that integrates forensic ingestion with cryptographic proof systems, and managed redactions.
It relies on a Zero-Knowledge Proof that certifies the relationship between the original and the redacted file. This technology generates a mathematical proof that the only changes made to the published PDF were the addition of black boxes over specific pixels. This allows third parties, such as expert witnesses, to “check the math” and verify that no text was altered or deleted, maintaining the document’s integrity while fulfilling privacy obligations
JOURNALISM
Verifiable Redaction allows newsrooms to protect the privacy of vulnerable bystanders without sacrificing the credibility of their reporting. By providing a cryptographic guarantee that only specific PII was obscured, journalists can defend their primary sources against bad-faith accusations of manipulation.
HISTORY
This technology safeguards the sanctity of historical records by ensuring that “anonymized” archives remain verifiable links to the past.
LAW
Verifiable Redaction establishes a court-admissible chain of custody for documents containing sensitive material. ZKPs benefit can facilitate the verification of proprietary forensic software, complex discovery datasets, and sensitive testimonial claims without compromising the underlying trade secrets or personal privacy that often create insurmountable disclosure dilemmas.
Witness Servers
Capture
Establishing institutional trust and technical corroboration for web evidence through decentralized, simultaneous crawling and cryptographic signatures.
YEAR
2024
PARTNERS
Webrecorder
FFDW
Harvard Library Innovation Lab
LINKS
– Concept note and Call for Contributions
– Our whitepaper on best practices in web archiving
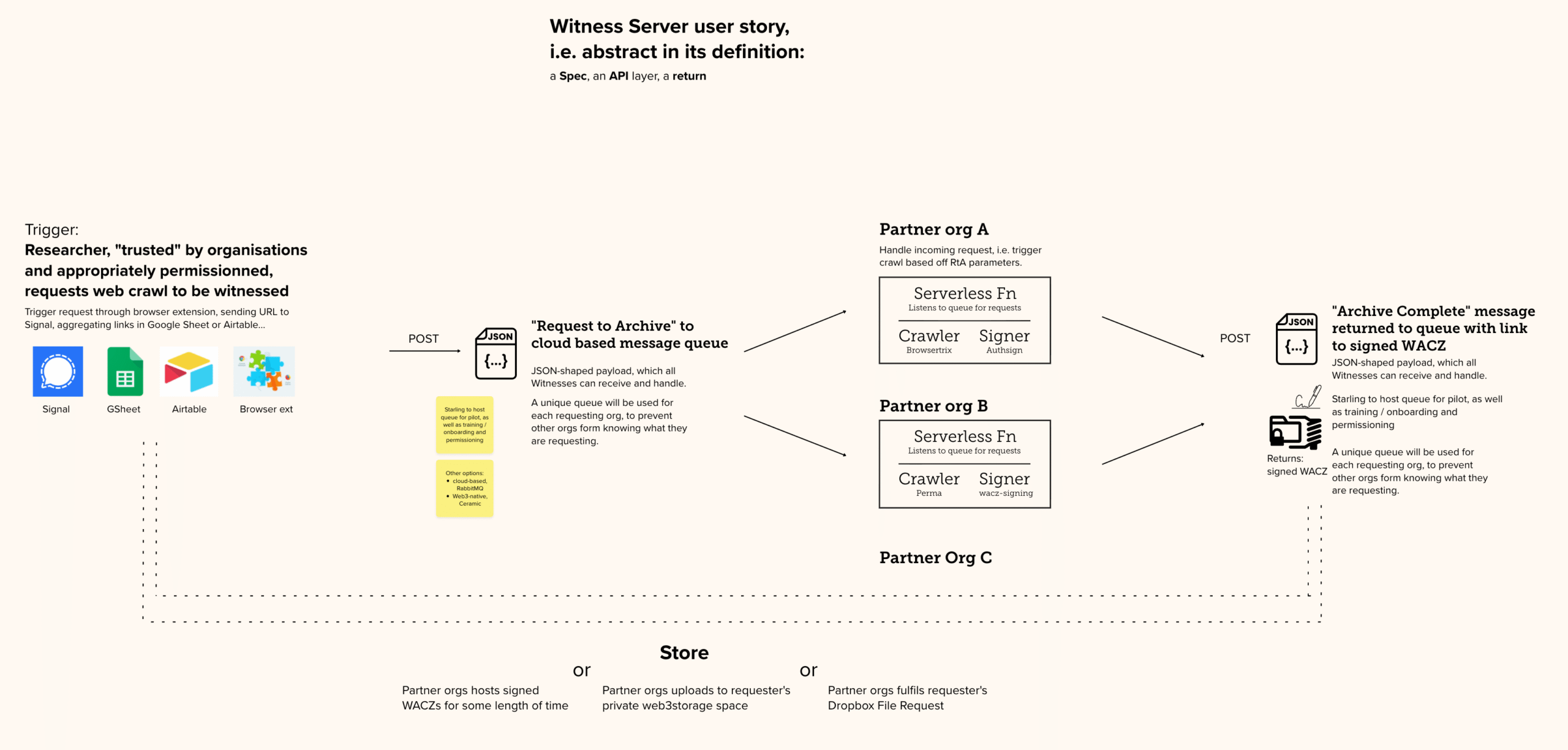
The Problem
Minute, technical, cosmetic errors plague efforts of open source monitors who scour the Web and archive its content. In the context of legal investigations, these minor defects are considerable challenges to the reliability of the artifacts, and thus to the facts they aim to prove. Moreover, small organizations and individual investigators face a greater burden in arguing the probative weight of the material they collect than large, reputable, and established institutions.
The Solution
We are developing the Witness Server prototype To replicate social trust in digital capture by involving reputable institutions as simultaneous observers of the web.
In short: a Witness Server is a service hosted by an institution that conducts on-demand web crawls. When a researcher initiates a local capture, a request is simultaneously dispatched to several partner Witness Servers (such as Harvard LIL or the Atlantic Council). Each institution performs its own crawl independently using its own infrastructure, creating a multi-perspective record of the same web content at that exact moment.
The prototypes follow all our learnings about web archives, Including the use of the WACZ open source format which bundles signed and hashed files.
By comparing multiple institutional archives, investigators can explain away non-material “cosmetic” defects (like pop-up banners) and provide overwhelming proof of the core content’s authenticity.
REFERENCE IMPLEMENTATION
On Github →
Still Photogrammetry
Capture
Still Photogrammetry integrates authenticated metadata with 3D spatial reconstruction to provide a verifiable record of physical environments and historical sites.
By utilizing a decentralized framework where every source image is treated as an independently verifiable “atom” of fact, this prototype allows investigators to build unalterable, three-dimensional timelines of evidence. It anchors complex digital twins to a cryptographic “proof of existence,” proving that the spatial data has not been tampered with since the moment of capture and restoring trust in digital primary sources for law and journalism.
YEAR
2022-26
PARTNERS
Mike Caronna
Pixelrace
Artem Ivanenko
LINKS
The New Horizon Lab
Starling Lab’s Spatial Digest
The Problem
Techniques such as photogrammetry (and more recently, NeRF and Gaussian Splatting) permit the reconstruction of a space in 3D, from stitching together 2D photographs. These tools are key to both extended reality environments and to investigations driven by architectural practices. However, integrity and provenance data is lost in the computing that renders the 3D models.
The Solution
Starling experiments with capture techniques supportive of 3D reconstruction while including provenance and integrity markers. From using smartphones to professional DSLRs, we test the technical constraints against the needs of photogrammetry workflows, which require a large amount of photographs of the scanned location.
Furthermore, we are also prototyping virtual UIs in virtual reality aiming to bridge the gap between what the viewer can see (the 3D model) and the original location (as per the 2D photographs). The viewer can navigate the space and select these authenticated “anchors” to interrogate the model, furthering their trust in the reconstruction.
SELECTED WRITING
Our 2025 paper: Verifiable Reality: Contrasting Approaches to Photorealistic VR Using NeRF Streaming and Gaussian Splatting Technologies

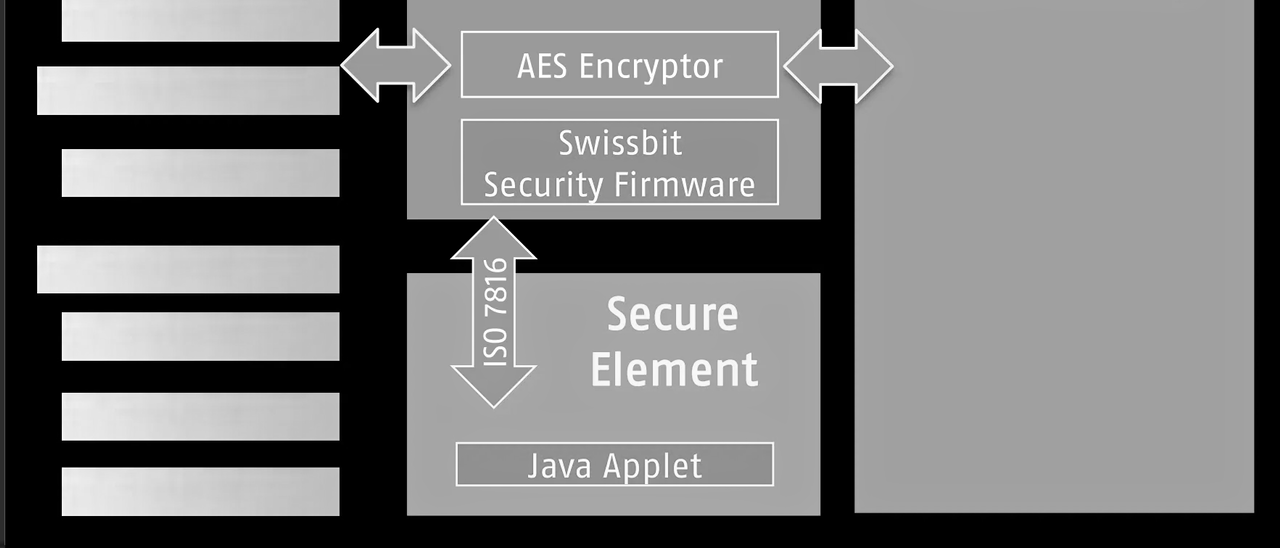
SD Card Encryption
The Problem
Losing control of data can happen when journalists, historians, or legal experts least expect it. SD cards can be seized during border crossings, left behind in a taxi, or stolen from a hotel room. Evidence that has been captured on an SD card, and which has not yet been anonymized, might carry geolocation or identity information that can lead authorities or militants to vulnerable people being photographed or interviewed. Another risk to unencrypted data on an SD card is that it could be manipulated undetected when not in one’s possession, with files erased or modified.
Prototypes are being tested by Starling Lab that both encrypt and hide important data captured by those in the field.
The Solution
Starling Lab is collaborating with industry partners including Swissbit, a leader in secure storage, to deploy hardware-encrypted SD cards that protect media the moment it is written to disk. This prototype ensures that digital assets are secured independently of the camera’s software vulnerabilities.
The solution creates an “encrypted tunnel” between the camera lens and the storage medium. Swissbit’s hardware-based encryption automatically protects image and video data without requiring additional software on the capturing device, ensuring that media cannot be manipulated or viewed in transit.
To protect the safety of practitioners in the field, the prototype relies on hidden partitions on the SD card. Sensitive files are stored in a manner that makes them impossible for unauthorized parties to discover or decrypt (even if the physical card is seized and inspected), while providing a critical layer of plausible deniability.
5G Network Attestation
Capture
Validating device metadata through fixed network infrastructure and reputable independent observers to establish trust in captured data.
YEAR
2024
PARTNERS
T-Mobile
Deutsche Telekom
Vonage
LINKS
– UN submission: Authenticity for human rights defenders in remote areas
The Problem
Mobile phones allow journalists to capture and transmit digital media with contextual information. However, since mobile phones are controlled by the end users, they permit manipulation of all forms of metadata, like GPS spoofers to fake location data. It is not enough for the location data collected by the Starling Capture app to be derived from metadata recorded solely by that mobile phone; it must be cross-referenced against the data signals transmitted and received by GPS, WiFi, cell towers, and/or beacons so that there is third-party attestations that the mobile phone is reporting location data correctly.
The Solution
Starling Lab is moving the “trust anchor” from the individual handset to the fixed infrastructure of the 5G network. By utilizing the C1 Mini framework, we enable a new class of “Network Attestations” that treat the mobile carrier as a reputable, independent witness to the capture of digital evidence.
The core of this prototype is the C1 Mini application, which leverages the standardized CAMARA APIs (exposed via Vonage and Deutsche Telekom). Instead of relying on easily phished 2FA codes, the system uses Silent Network Authentication (SNA). This process cryptographically verifies the unique identity of the subscriber’s SIM card directly with the carrier’s core network in the background. This ensures that the data registration request is coming from a legitimate, physical device authenticated by the network operator, not a spoofed virtual instance.
To support practitioners in remote or high-risk areas, the C1 Mini facilitates the “expedited registration” of asset fingerprints. Users can transmit the cryptographic hash of a photo or video via a secure SMS tunnel to a Starling registration server. This allows for a “proof of existence” to be anchored on a decentralized ledger (such as Solana or Hedera) even in low-bandwidth environments where uploading large raw files is impossible. This creates a tamper-evident timestamp that is significantly harder to manipulate than a device’s internal system clock.
This creates a multi-layered defense against disinformation: a hardware-signed image, a network-verified location, and a decentralized timestamp, all established at the point of capture.