Authenticated Attributes
2024
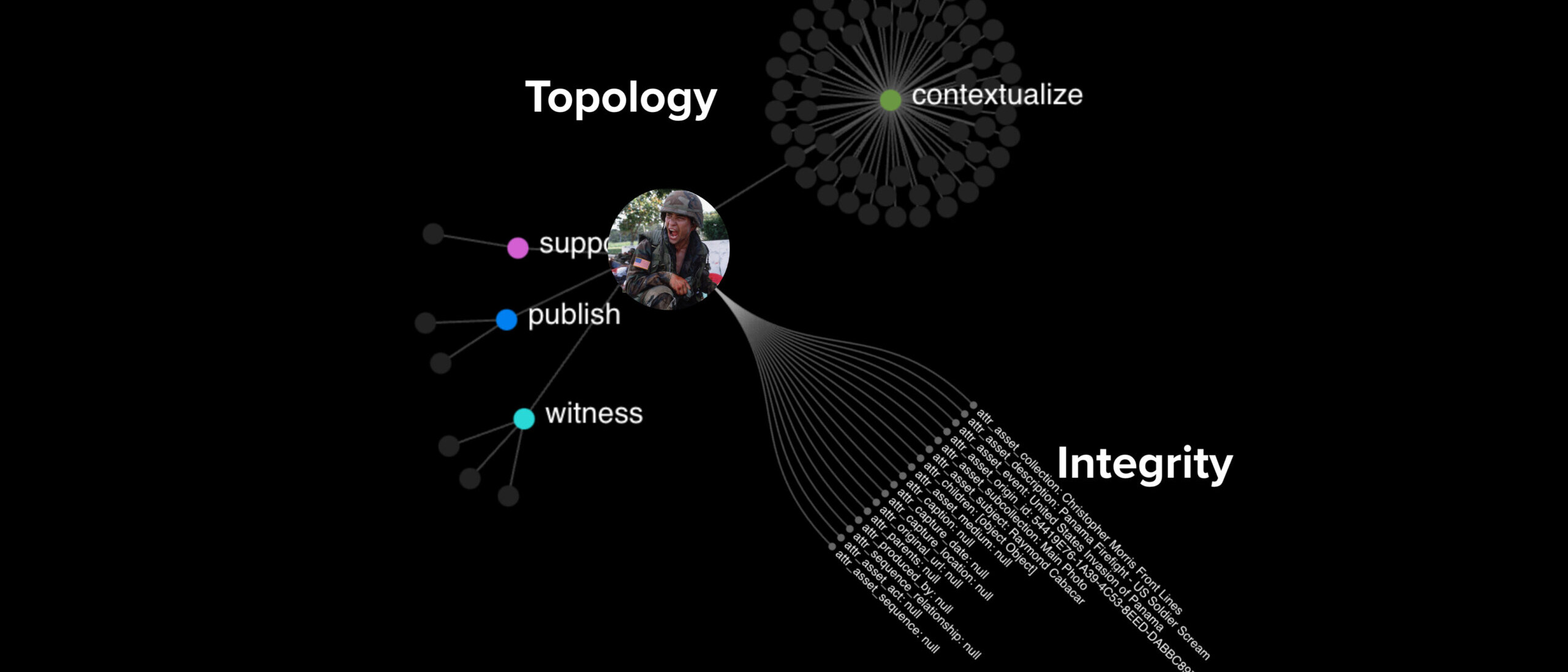
Authenticated Attributes (AA) is a decentralized infrastructure designed to restore trust in digital media by establishing the proven integrity of metadata. Moving beyond traditional, centralized databases, it treats every piece of information as an independently verifiable “atom” of fact, allowing investigators to construct unalterable timelines of evidence.
This concept shifts the verification paradigm from trying to detect AI-generated falsifications (deepfakes) to affirmatively proving authenticity. It anchors digital content to a “proof of existence,” utilizing third-party timestamping to demonstrate exactly when a file was created and ensuring it has not been altered since.
The Problem
The traditional methods for trusting digital images and records are breaking down due to the rise of AI-generated content (deepfakes) and a general erosion of trust in institutions. Investigators and archivists face several specific challenges:
- There is no standard way to reference the same image or file across different organizations.
- Secondhand information is difficult to verify, and different sources often provide conflicting data.
- Centralized databases are vulnerable to tampering, often requiring strict access controls that limit collaboration
JOURNALISM
Authenticated Attributes allow newsrooms to cryptographically bind specific details (like location or time) to content so audiences can independently verify the reporting’s origin without compromising sensitive sources.
HISTORY
By attaching unalterable proofs of existence to digital artifacts, AAs ensure that future historians inherit primary sources that are traceable and immune to revisionism.
LAW
AA creates a tamper-evident link between evidence and its metadata, allowing investigators to prove that critical details haven’t been altered since the moment of capture.
The Solution
Authenticated Attributes is a tool that allows investigators to verify digital content by sharing authenticated metadata and attestations that cannot be faked or tampered with. It restores trust through a decentralized framework:
-
Cryptographic hashes and digital signatures uniquely identify files and authenticate sources.
-
Third-party timestamping proves exactly when data existed.
-
Flexible reconciliation lets investigators weigh conflicting sources without discarding data.
-
Peer-to-peer replication ensures data remains persistent and available.
—
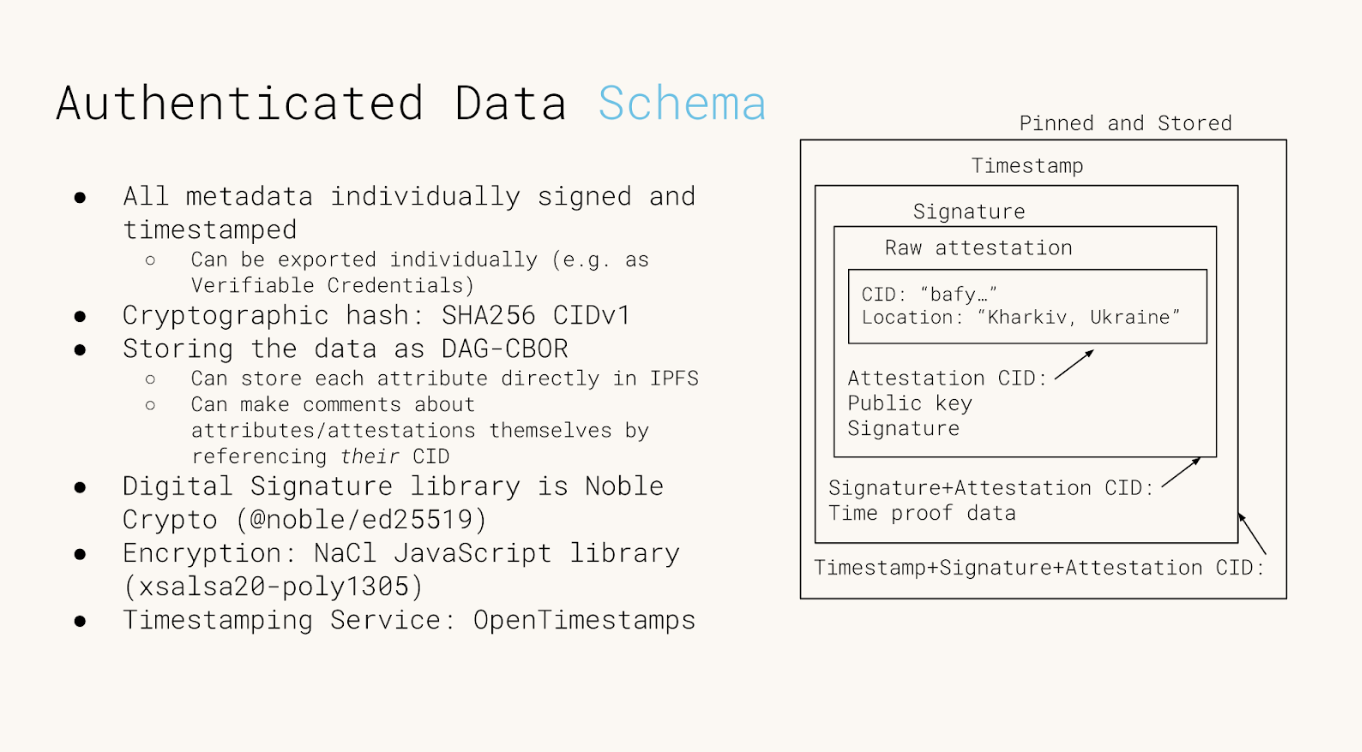
The initial implementation of Authenticated Attributes express them from the following data structure (more details in the Github repo):
SELECTED WRITING
Web Archives as Evidence (using AA)
Slide deck and Youtube video
Working on Authenticated Data with AA
By Cole Capilongo
Time for (Trusted) Timestamping
By Cole Capilongo
An Alternative to Deepfake Detection
By Kate Sills
UN Submission on ‘an Index for Accountability’, a prototype built on AA
Authenticated Camera Capture
2024
Authenticated Camera Capture establishes a root of trust at the absolute moment of creation by embedding cryptographically signed metadata directly into media files. Spearheaded by the C2PA standard and major manufacturers like Leica, Sony, and Nikon, these prototypes shift the verification paradigm from reactive deepfake detection to affirmative proof of origin.
They rely on hardware-backed secure enclaves to sign images with private keys, ensuring that every photo or video carries a tamper-evident record – a “birth certificate” – that traces back to the original sensor and time of capture.
YEAR
2020-26
PARTNERS
Canon Cameras
Reuters
Adobe (Content Authenticity Initiative)
Leica Cameras
The Problem
Photographs circulate globally, often years after capture, stripped of metadata and decontextualized. Viewers are left unsure of who captured an image, or when and where events occurred. This vulnerability is exploited by bad actors using AI to manipulate content, giving rise to the “Liar’s Dividend” where even authentic evidence can be dismissed as a deepfake.
Furthermore, existing “companion device” workflows (pairing a camera to a smartphone) often suffer from field challenges like Wi-Fi connection issues, battery drain, and the technical complexity of managing multiple devices in high-pressure conflict zones.
Finally, a core challenge in authenticating news media is accounting for the reality of permissible edits. In photojournalism, editing a raw file is not inherently deceptive; it is a necessary step in the editorial process. Photo editors routinely crop images to fit specific publication layouts, adjust exposure or color balance to ensure visual clarity, and append critical contextual metadata such as captions, location data, and copyright credits. While these routine, ethical adjustments do not alter the factual truth of the scene, they inherently change the digital fingerprint of the file.
CASE STUDIES
– Canon-Reuters Collaboration on Preserving Trust in Photojournalism
LINKS
– The Canon-Reuters prototype POC
– Petapixel: Canon and Reuters develop new photo authentication technology
– On offline benefits: our submission to the UN Special Rapporteur on Human Rights Defenders
The Solution
We experimented with several authenticated camera-centric workflows that enabled professional cameras to natively generate and sign C2PA manifests upon capture. By integrating signing keys into hardware-based secure enclaves (Trusted Platform Modules), the system ensures that private keys cannot be extracted or cloned, establishing a permanent “root-of-trust” within the device’s silicon.
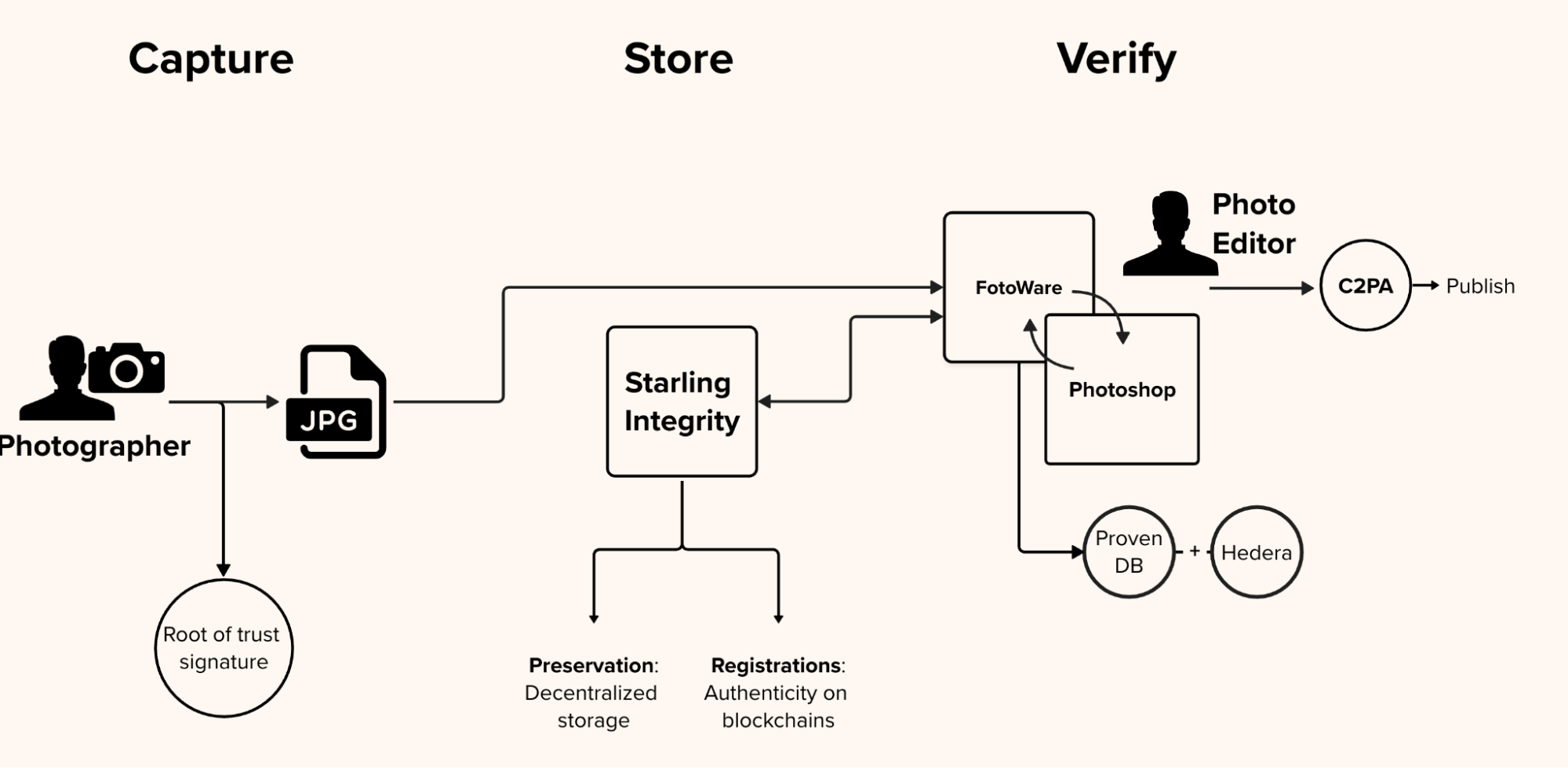
From lens to a reader’s screen, this “glass-to-glass” chain of custody, pioneered with specialized firmware for Canon devices, injects rich, signed metadata—including server-acquired timestamps and GPS coordinates—directly into JPEG files. This ensures that every asset carries its own proof of integrity, allowing audiences to audit the steps taken from the initial shutter click to publication through standard inspection tools.
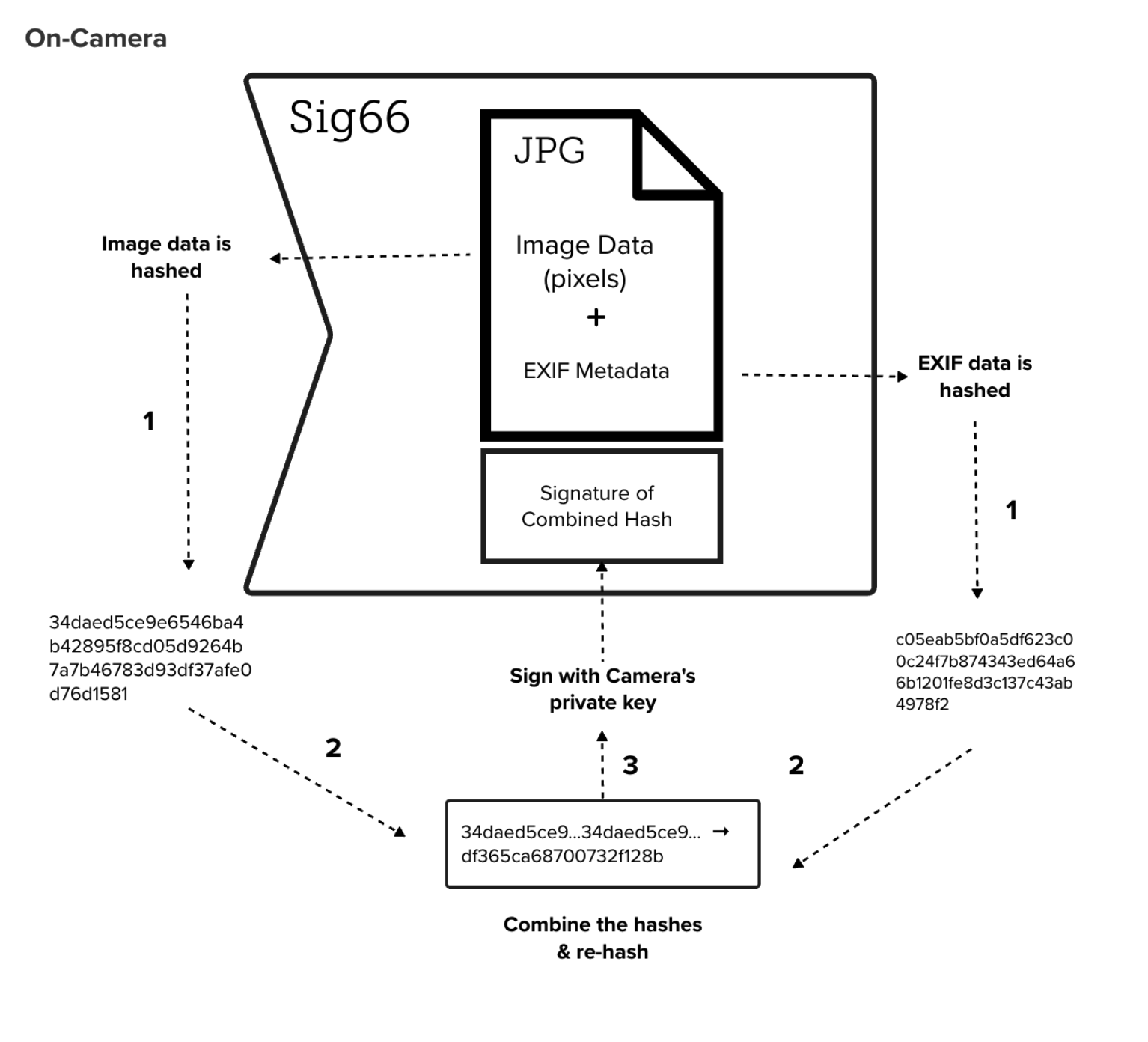
The on-camera process. The firmware computes a combination hash of image pixels and EXIF metadata, signs it with a unique factory-programmed private key, and appends the signature to the JPEG data.
To bridge the gap between capture and publication, the Starling Integrity backend tracks permissible modifications in the background. Using webhooks within the Fotoware CMS, every edit, from caption updates to Photoshop adjustments, is recorded as a new entry in a C2PA manifest and anchored to the Hedera public ledger. This creates a mathematically provable, immutable audit trail that survives the industrial scale processing of a global newsroom.