Reuters and Canon Deploy Verifiable Photo Newswire
End-to-End Content Authenticity, from the Canon Camera to Reuters Desk
Learn how a collaboration between Reuters News Agency, Canon technologies, and the Starling Lab for Data Integrity created a novel end-to-end authenticity workflow to protect photojournalism.
Reading Time: 5min
Contents
Background
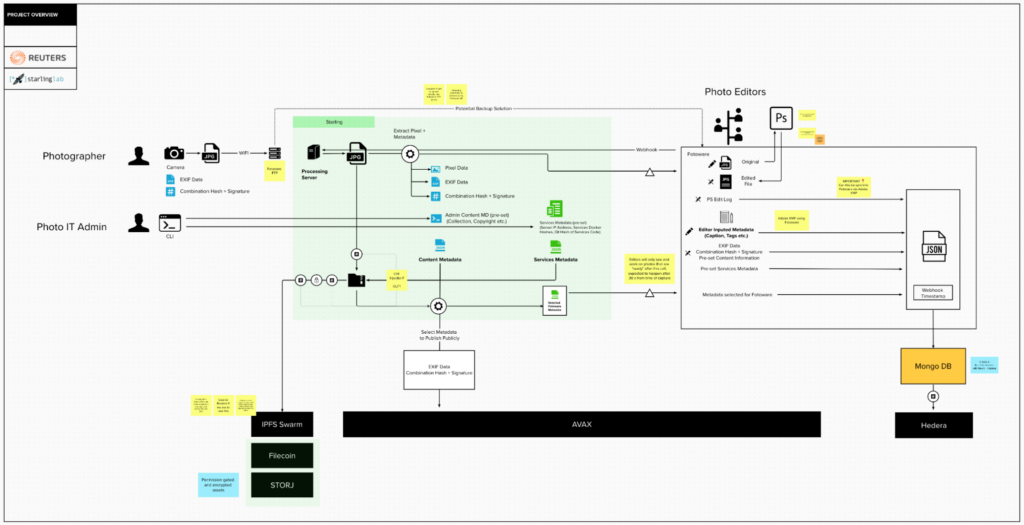
Reuters News Agency, Canon technologies, and the Starling Lab for Data Integrity teamed up to demonstrate a novel end-to-end authenticity workflow. By incorporating a content management system created by Fotoware, which is widely used by reporters and news agencies, the project achieved end-to-end preservation of all provenance metadata.
Editor’s Note (2025): Since the conclusion of this project, the landscape of image authentication has rapidly evolved. While this proof-of-concept required bespoke, modified prototype hardware, we are now seeing the integration of cryptographic hardware and software signatures directly into standard, consumer-grade cameras. Devices such as the latest Sony and Leica models, as well as smartphones like the Google Pixel 10, now provide built-in authenticity layers.
This commercial availability signals a significant step toward the widespread, accessible adoption of the provenance frameworks pioneered in this prototype.
Contents
Context
For this project, Starling Lab teamed up with Thomson Reuters and Canon to prototype the future of photo authentication, addressing the growing threats of visual mis- and dis-information. As a leading global news agency, Reuters works relentlessly to capture the first draft of history. To protect the hard-earned trust newsrooms have built—especially as generative AI makes digital deception increasingly accessible—we need robust technology that guarantees the provenance and auditability of photojournalism.
Canon, a world-leading imaging provider and Content Authenticity Initiative (CAI) member, built key cryptographic features directly into their camera firmware for this collaboration. This allowed the Canon camera to serve as the project’s root-of-trust, setting a new precedent for authenticity standards in the news community.
This project builds directly upon Starling Lab’s earlier 78 Days initiative. While that project successfully preserved capture information, it relied on tethering a camera to a cell phone via Wi-Fi to establish a root-of-trust. This method was logistically challenging and presented usability issues for journalists in the field. Furthermore, it lacked an automated way to track metadata end-to-end as media inevitably moved through newsroom content management systems (CMS) and photo editing software.
For this iteration, the team set out to solve these gaps by integrating emerging technologies from Canon, Hedera, Photoshop, and ProvenDB to build a seamless, end-to-end preservation pipeline.
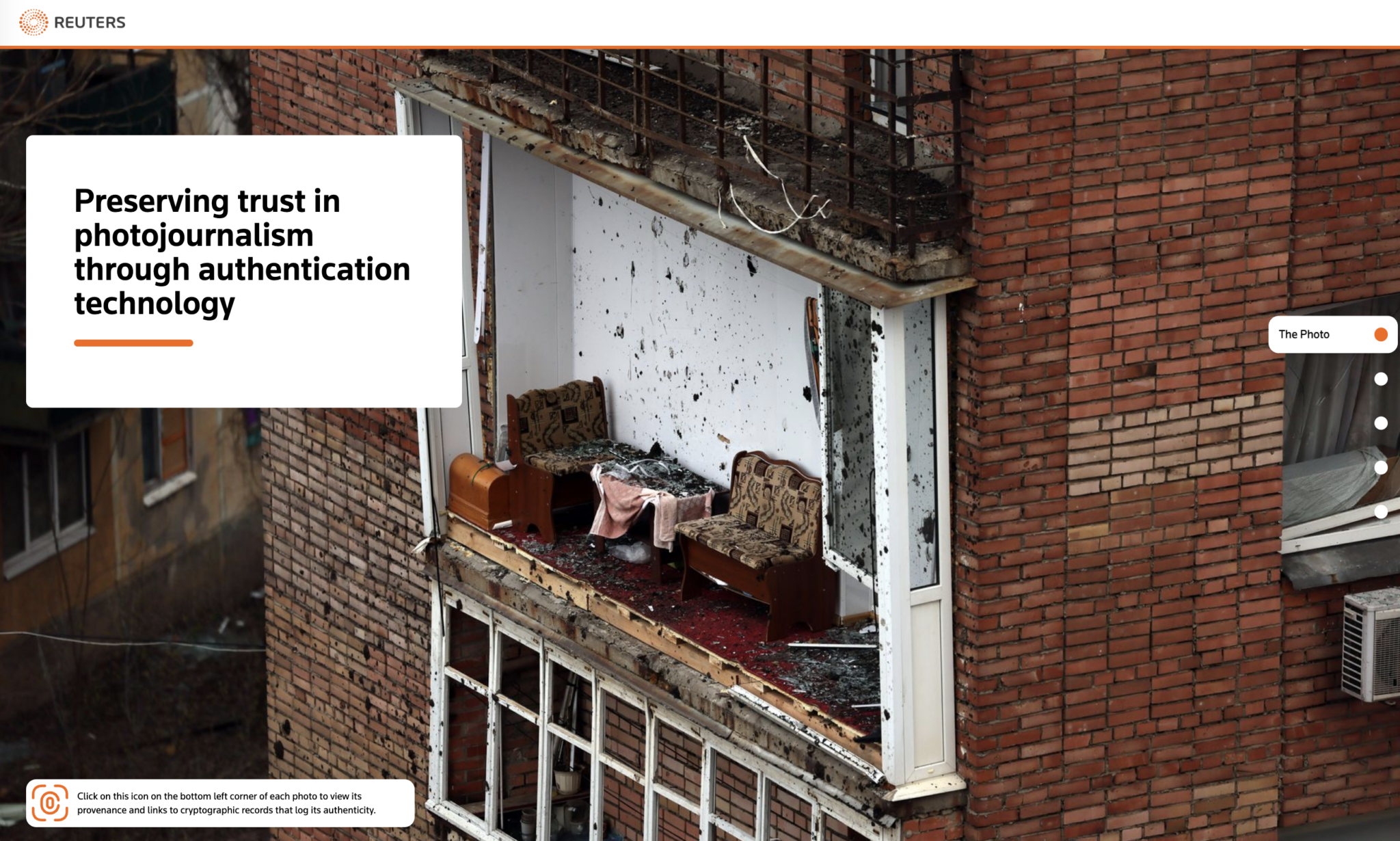
The project’s images were captured by photojournalist Violeta Santos Moura in eastern Ukraine during March and April 2023, documenting the devastation of Russian attacks along the front lines. Armed with a prototype Canon EOS R3 camera featuring built-in cryptographic integrity, Moura’s photos were processed through an integrated workflow that tracked every subsequent edit via Fotoware CMS and Starling’s Integrity Backend.
Because documenting conflict involves severe safety risks, extreme care was taken regarding data publication. While extensive contextual metadata was securely preserved and sealed for future evidentiary or historical use, only two photos and their provenance records were made public. These results were published on a Reuters microsite, providing a powerful demonstration of how end-to-end authenticity workflows can successfully protect the integrity of digital media.
Contents
Framework
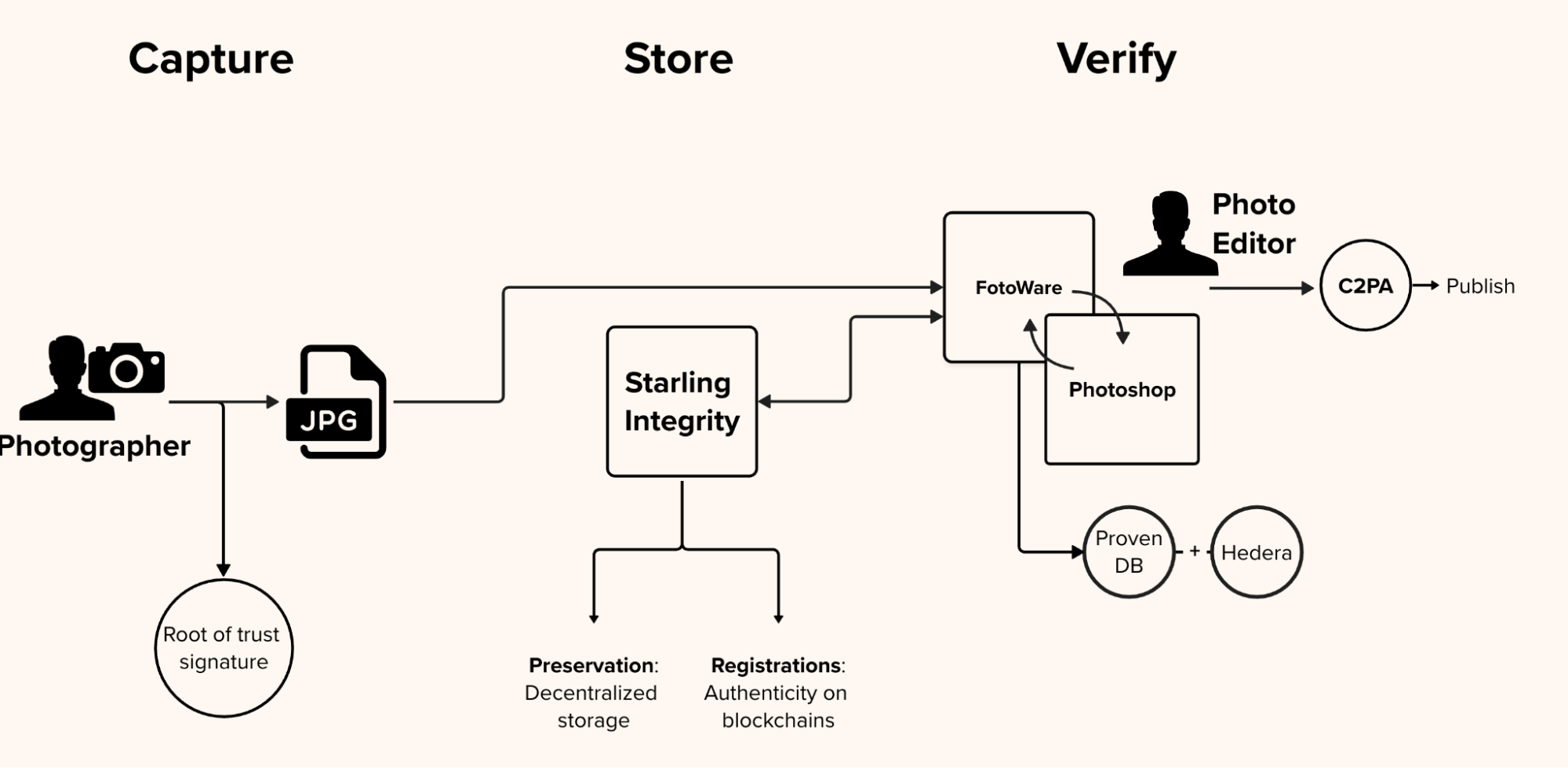
The Starling Lab Capture, Store, Verify framework was applied to the existing Reuters journalistic workflow and interlaced with distributed web technology and traditional cryptographic practices to create a record and interface to understand the provenance of images that are captured in the field.
The Challenge
The traditional journalistic process relies heavily on public trust in a publisher’s reputation. However, in the digital age, a photograph rarely reaches the public exactly as it was captured.
A core challenge in authenticating news media is accounting for the reality of “permissible edits.” In photojournalism, editing a raw file is not inherently deceptive; it is a necessary step in the editorial process. Photo editors routinely crop images to fit specific publication layouts, adjust exposure or color balance to ensure visual clarity, and append critical contextual metadata such as captions, location data, and copyright credits. While these routine, ethical adjustments do not alter the factual truth of the scene, they inherently change the digital fingerprint of the file.
At a global news agency like Reuters, this process happens at an industrial scale. Thousands of images flow daily from the front lines into centralized Content Management Systems (CMS), such as Fotoware, where they are accessed by editors worldwide. These enterprise systems are built for speed and efficiency, often automatically compressing files, reformatting data, or overwriting previous metadata with every single save. Because standard asset management systems lack the ability to immutably version these changes, the cryptographic chain of custody is easily broken the moment a photo enters the newsroom pipeline.
Therefore, the central challenge of this project was not just technical, but operational. A successful provenance system cannot disrupt the fast-paced business of producing the daily news. If journalists are burdened with clunky field equipment, or if editors must drastically alter their workflows to manually log changes, the solution will not scale. The goal was to establish a secure root-of-trust at capture and seamlessly track every permissible modification through existing CMS platforms, creating a friction-free, verifiable audit trail from the lens to the reader.
The Prototype
To solve this, the Starling Lab engineering team designed a seamless, end-to-end pipeline to register and preserve every step of a photograph’s journey. Crucially, this system was engineered to operate in the background, ensuring it would not disrupt the fast-paced newsroom environment. Moving away from the logistical constraints of previous experiments, the new prototype was built around three continuous phases:
First, the establishment of a root of trust. The process begins by embedding cryptographic capabilities directly into the journalist’s equipment. Rather than relying on clunky external tethers, Wi-Fi pairings, or companion smartphone apps, the prototype relies on a camera capable of cryptographically signing the image and its foundational metadata at the exact moment the shutter is pressed. This ensures the original file’s integrity is sealed at its inception.
Second, tracking the editorial pipeline. Once captured, the system creates an immutable audit trail that works invisibly alongside standard newsroom tools. As the image is transmitted to the publisher’s asset management system and undergoes permissible edits by photo editors—such as cropping, color correction, or captioning—an automated background process tracks the file. Every single modification is recorded in a private, verifiable database that is anchored to a public distributed ledger, creating a mathematically provable edit log.
And finally, the delivery of a verifiable asset. The final step focuses on empowering the end consumer. The prototype packages the initial hardware signature, the original metadata, and the complete, cryptographically secure edit history into a standardized, open-source manifest. This manifest is embedded directly into the final published image, allowing anyone—from researchers to everyday readers—to inspect the file and independently verify its authentic journey from the frontlines to their screen.
Contents
Technology
The Starling workflow we developed enabled Violeta Santos Moura, the photographer for this project, to take photos in Ukraine using a special concept camera from Canon, CMS software from FotoWare, and the Starling Integrity pipeline and authenticate that data immediately upon upload to the Fotoware CMS. The editing team was enabled in tracking all their edits and changes with integrations between Fotoware CMS & the Starling Integrity backend, as well as the use of Photoshop for any edits, tracking changes in a C2PA manifest.
Starling was able to use this process of authenticated capture by the photographer, put it into secure and verifiable sharing and storage, and publish verifiable versions of this data with ProvenDB and Hedera (hashgraph?). This work done alongside the Reuters team preserves the data about the lifecycle of an image and its integrity, which is tracked, verified, and registered on the blockchain.
Capture
The journey of establishing an unbroken chain of provenance began directly on the frontlines with a first-of-its-kind hardware integration. The prototype process starts with a photographer in the field who was given one of six prototype cameras. In our previous 78 Days project, establishing a root of trust required tethering a camera to a cell phone via Wi-Fi. This created severe logistical hurdles: congested networks interfered with the connection, and the camera could not simultaneously connect to the internet to upload files. Furthermore, the system only supported individual photographic shots, lacking the capability to hash and sign burst mode or large video files.
To solve this, Canon, Reuters, and Starling Lab spent three years developing a modified firmware for the Canon EOS R3 prototype. Advised by Stanford cryptography professor Dan Boneh, Richard Shepherd and Akiyoshi Ishii from Canon created a camera that can digitally assign a time, date, and location, then digitally hash and sign that set of information – without external tethers, using a firmware software signature.
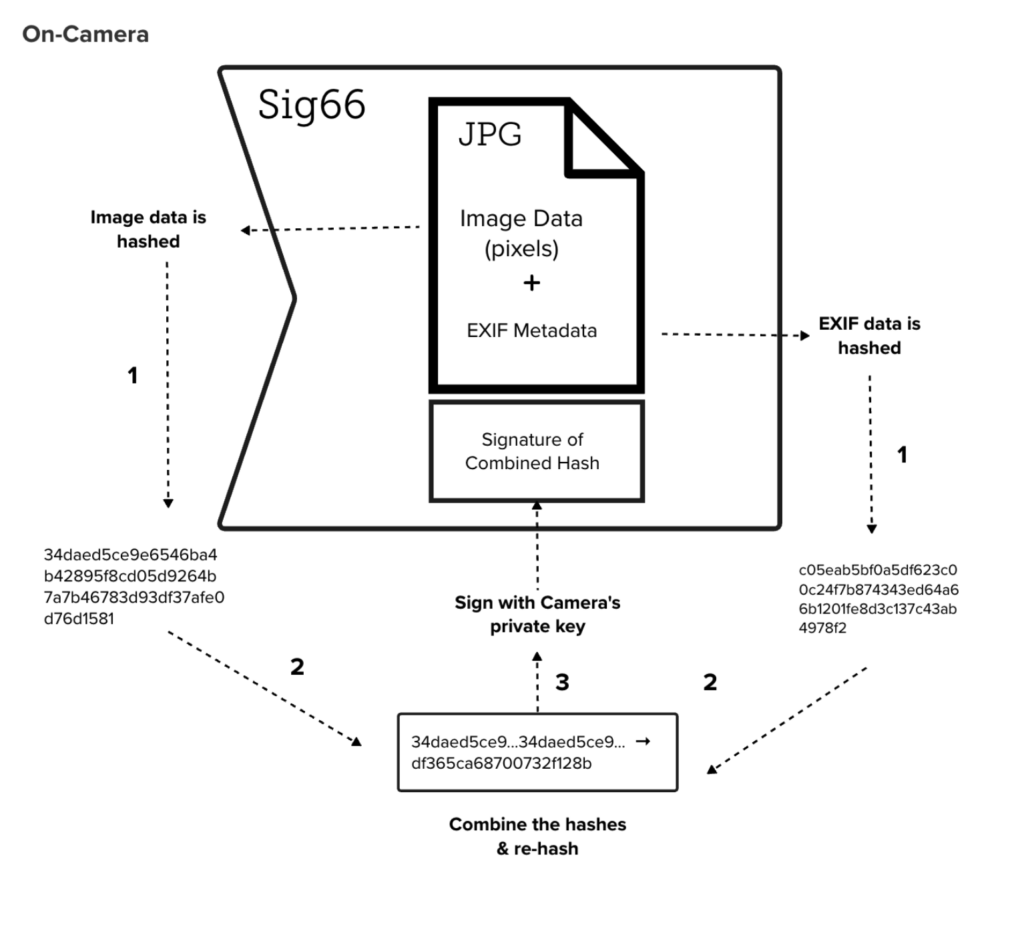
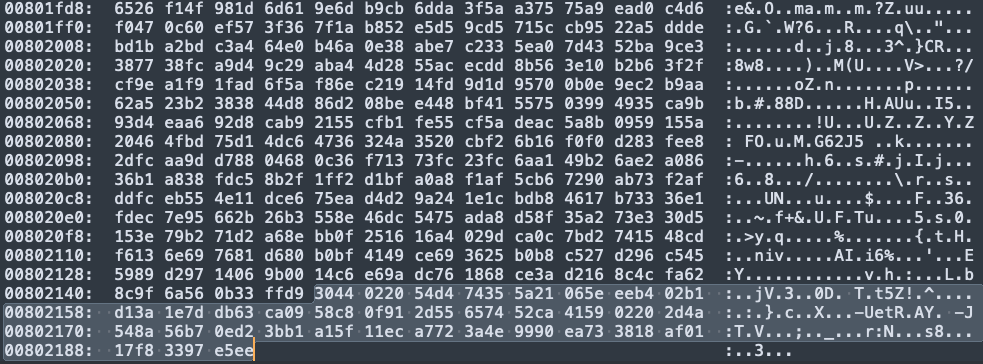
A private key is written directly into the firmware, programmed at the factory with a unique private key associated only with that specific device. At the exact moment of capture, the camera computes a combination hash derived from both the raw image pixels and the EXIF metadata. Images taken by the photographer are now hashed and signed before they are written to an SD card where they are stored. The camera, pre-programmed at the factory with a unique private key, uses this key to cryptographically sign the combination hash. This signature is then appended directly to the end of the JPEG data—specifically after the 0xFFD9 marker—using a custom scheme.
Bypassing the need for any companion apps or external devices, the camera instantly transmits these signed images straight from the device to a Fotoware FTP server via Wi-Fi.
Store
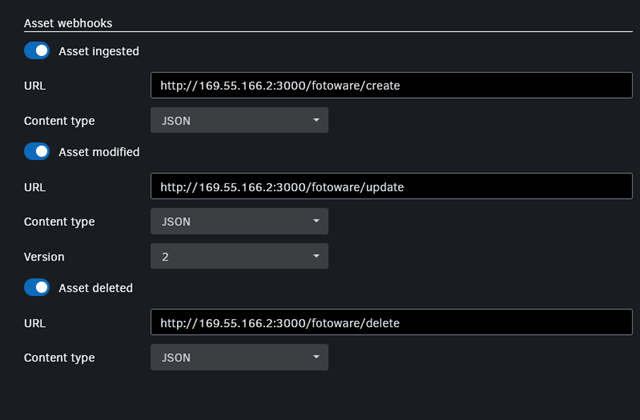
Once the image leaves the camera, the system must immediately secure the original asset before it can be altered by standard newsroom ingestion processes. When a new file hits the Fotoware FTP server, a custom webhook notifies the Starling Integrity server. Starling instantly downloads a copy of the file and verifies the Sig66 signature against the specific camera’s known public keys, ensuring the file hasn’t been tampered with in transit.
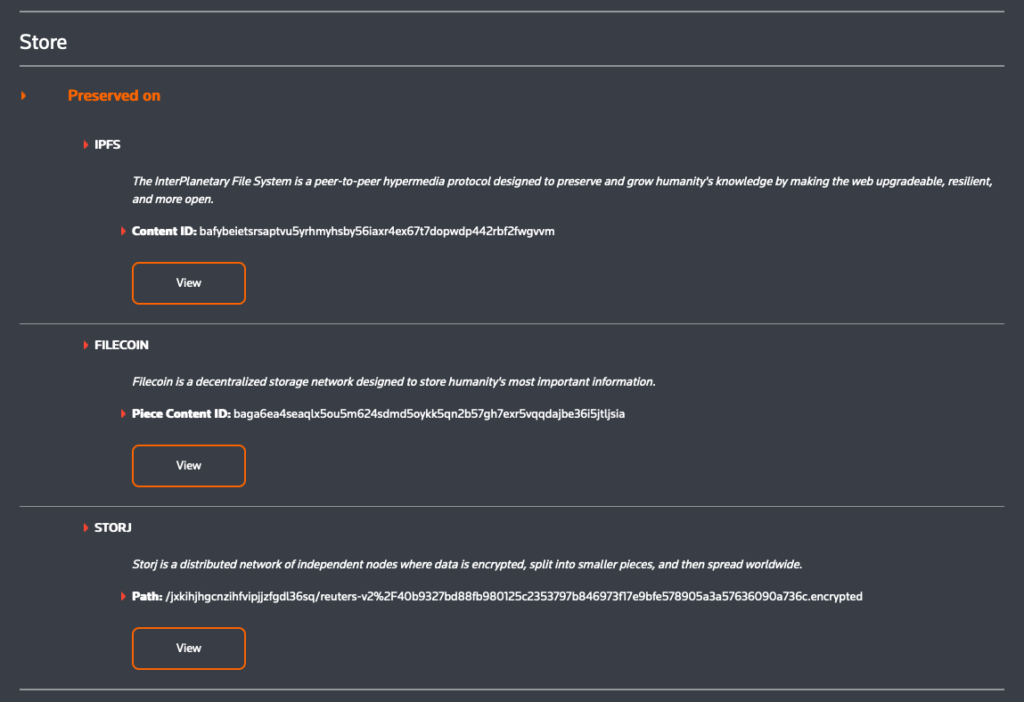
To guarantee the image’s long-term survival and immutability, the original file is preserved on decentralized storage networks, specifically utilizing the IPFS, Filecoin, and Storj protocols. Simultaneously, Starling constructs a secure metadata package and registers the asset immutably across several public blockchains. This registration process leverages OpenTimestamps, which is anchored to Bitcoin, as well as the Avalanche, Numbers, and LikeCoin (ISCN) networks, creating a permanent, decentralized public record of the original capture.
Verify
The most complex phase of the project involved tracking the permissible edits made by Reuters photo editors. Integrating the authentication into a piece of software like Fotostation adds in a critical piece of processing power that enables the creation of provenance records alongside the media itself. Centralized systems like Fotoweb are not built to preserve cryptographic integrity.
Once photos are uploaded via FTP to a Content Management System (CMS), journalists can view and download them on the FotoWeb asset management system. Editors can manipulate the photos; add metadata and change the content with cropping, recoloring, and other enhancements in preparation for the image’s publication. FotoWeb currently has no versioning features, so there are no logs or indicators when images are changed. Each change overwrites the previous metadata and image without a log to refer to and there is no way to see the original image taken by the photographer. Furthermore, when an image is first ingested, Fotoweb automatically parses the photo’s EXIF metadata, turns it into XMP, and puts it back into the photo. The new timestamp included in the XMP fundamentally changes the identifying hash of the image.
To create a verifiable edit log, Starling augmented the system to track specific actions. The content management system is augmented with triggers and processed by the Starling Integrity backend. Anytime Fotoweb is used—whether an editor is changing metadata, adding a caption, or altering the image—the XMP data changes and the timestamp updates. In response, Starling Lab adds another entry in a C2PA manifest. Simultaneously, the system runs a Hedera webhook to register the change on-chain. This makes it possible for us to record changes in a local database with hashes that are anchored to a public ledger.
The system meticulously recorded three main types of actions on Hedera and ProvenDB:
- Creation (the initial capture and ingestion).
- Metadata changes (e.g., when someone goes into Fotoweb and edits a caption; mapped as Fotoweb > ProvenDB > Hedera).
- Photoshop edits (executed within FotoStation, mapped as PhotoWeb > FotoStation > Photoshop > FotoStation > PhotoWeb + ProvenDB > Hedera).
Not only does this mean that a version history is created, it also means that we have an immutable, linked cryptographic record of all changes, in several systems, that can be used if the veracity of a journalistic image is ever called into question. Ultimately, the initial capture data and the complete editorial history are combined to produce the final C2PA image for publishing, empowering the public to independently verify the photograph’s authentic journey from the frontlines to their screen.
To protect potentially sensitive metadata, the original assets registered in the Reuters V2 proof-of-concept are encrypted using an AES key before being stored on IPFS and Storj. Because this specific prototype does not contain sensitive data, a single AES key is shared openly, allowing users to inspect the archives using three technical methods:
AES key: 8ff68fd1321c51570bee444eabcc44fd90610567e4bc87749bae46ad2537af67- Starling Archive Explorer (URL Parameters) For seamless access without technical expertise, users can view the decrypted assets directly in their browser using the Starling Archive Explorer. This is achieved via direct URLs that encode both the IPFS source file location and the AES encryption key, automatically decrypting the content upon loading.
The links for the two assets are as follow:
- Lit Protocol via Web3 Wallet Authentication To demonstrate decentralized, permissioned access, the system utilizes the Lit Protocol – a distributed key management network. Users can mint a “Starling Access Token” to a MetaMask wallet via the Starling faucet. By navigating to the token on OpenSea and clicking “View website,” users are redirected to the Starling Archive Explorer. Upon signing a MetaMask transaction to prove token ownership, the Lit network securely provisions the decryption key to reveal the archive.
There is an animation on how this works at the bottom of https://github.com/starlinglab/archive-explorer
- Command Line Decryption (OpenSSL) For manual inspection, users can download the encrypted file directly from an IPFS gateway using command-line tools like wget. Once downloaded, the file can be decrypted locally into a standard ZIP file using OpenSSL’s AES-256-CBC cipher. This requires running the openssl command:
openssl aes-256-cbc \
-d \
-in bafybeidgi3yqkppxydeh5znm4jg3pycjnteyt25nogzj7ru7yek2lzttcy \
-out archive.zip \
-iv 0 \
-K 8ff68fd1321c51570bee444eabcc44fd90610567e4bc87749bae46ad2537af67
Contents
Learnings
Tooling and Infrastructure Constraints
During the development of the prototype, the team encountered multiple software conflicts. For example, they discovered that Photoshop was unable to execute both C2PA injection and change log exports at the same time. Furthermore, the C2PA verification site struggled to decode large integers correctly, which required a collaborative bug fix from Adobe.
Integrating with enterprise content management systems also presented friction. The team had to figure out how to deal with FotoWeb fundamentally altering files upon every single upload, a process that inherently breaks C2PA manifests. To properly manage this metadata, a dedicated Starling XMP area was created. Finally, the project faced infrastructure disruptions when Hedera’s public tooling (DragonGlass) stopped working unexpectedly, forcing the engineering team to rapidly switch over to alternative tools
Overcoming Previous Tethering Limitations
The hardware integrations in this iteration were specifically designed to solve the significant hurdles encountered during the previous “78 Days” project. In that earlier workflow, establishing a root of trust required tethering a camera directly to a cell phone via Wi-Fi. This presented considerable usability challenges, starting with the difficulty of simply establishing the connection between the camera and the phone. In the field, noise and congestion over various network bands could easily interfere with this Wi-Fi tethering. Moreover, while the camera was tethered to the cell phone, the photographer could not upload photos because the camera lacked concurrent internet connectivity
Camera Capabilities and Future Work While the new prototype successfully eliminated the need for tethering, the bespoke camera hardware still faces functional limitations. For this specific proof-of-concept, the system only supported individual photographic shots. Advanced capture modes, such as burst mode and video capture, were not supported. In order to enable these capabilities in future iterations, additional engineering work will be necessary to support the hashing and signing of the significantly larger files associated with video media.
Editor’s Note (2025): Since the conclusion of this project, the landscape of image authentication has rapidly evolved. While this proof-of-concept required bespoke, modified prototype hardware, we are now seeing the integration of cryptographic hardware and software signatures directly into standard, consumer-grade cameras. Devices such as the latest Sony and Leica models, as well as smartphones like the Google Pixel 10, now provide built-in authenticity layers. This commercial availability signals a significant step toward the widespread, accessible adoption of the provenance frameworks pioneered in this prototype.

